As a hacker, the final stage of exploitation is covering their tracks, which involves wiping all activity and logs so that they can avoid being detected. It's especially crucial for persistence if the target will be accessed again in the future by the attacker.

When Microsoft unveiled Mesh a couple of weeks ago, the move revealed a major part of Microsoft's next steps toward dominating the augmented reality space, particularly with regard to enterprise customers.
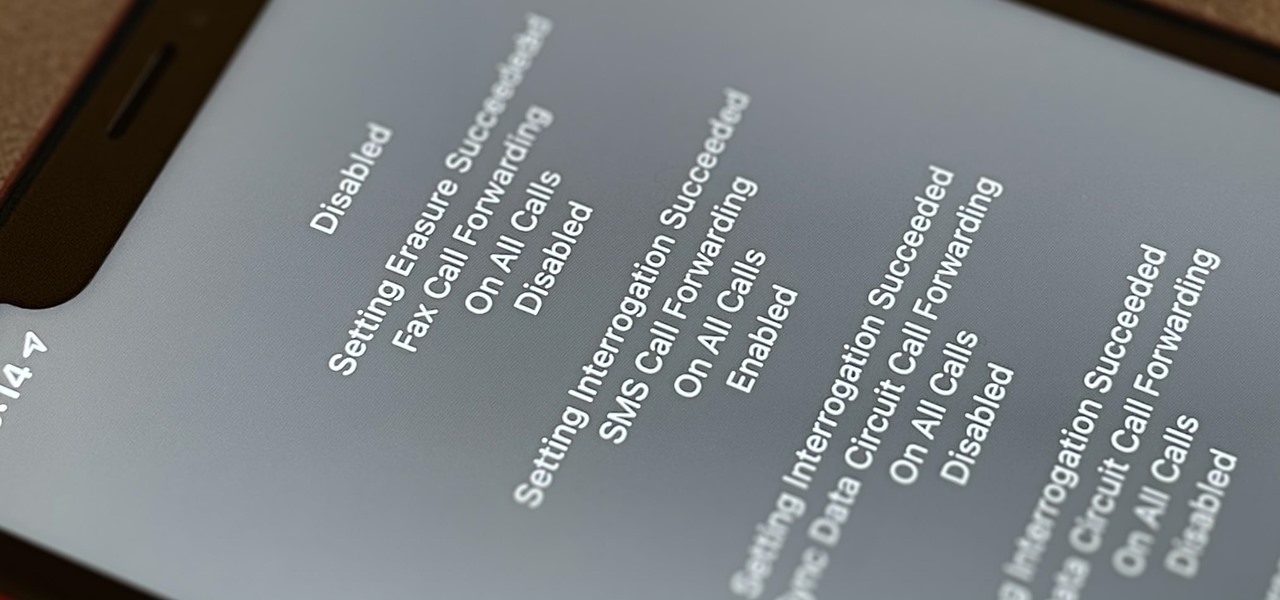
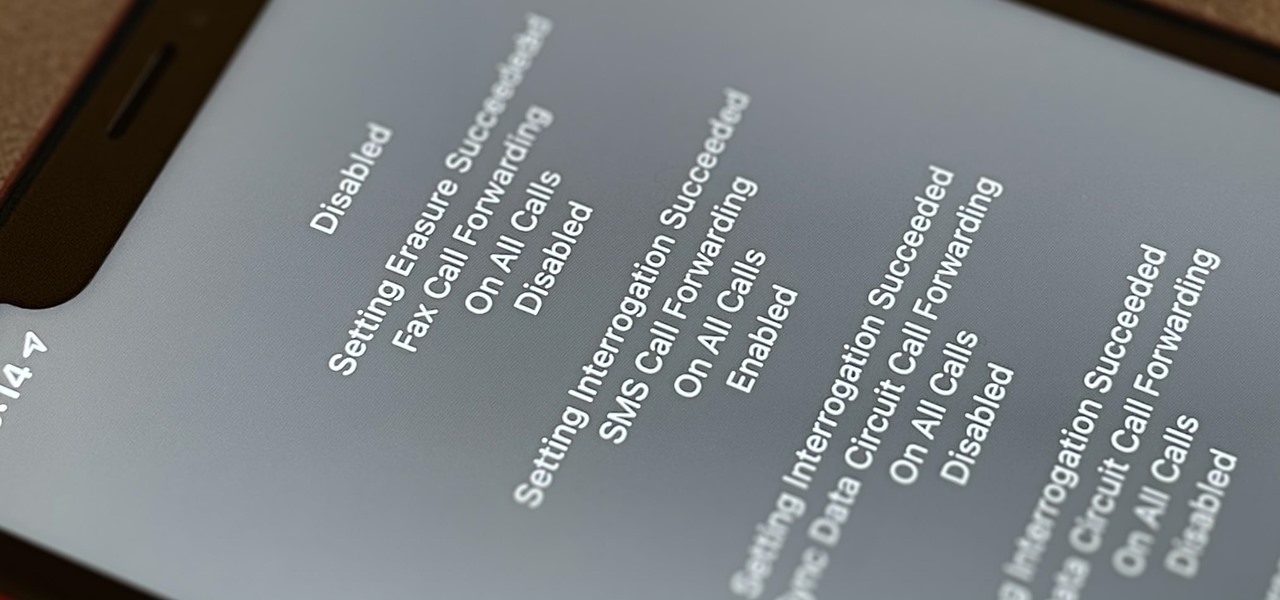
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

Finding an instrumental or karaoke version of a song can be pretty easy unless you're dealing with a song that isn't popular. That leaves you with just the full version of the song, complete with vocals. So how do you convert it into an instrumental or karaoke track?

The art of fuzzing is a vital skill for any penetration tester or hacker to possess. The faster you fuzz, and the more efficiently you are at doing it, the closer you come to achieving your goal, whether that means finding a valid bug or discovering an initial attack vector. A tool called ffuf comes in handy to help speed things along and fuzz for parameters, directors, and more.

There are countless tutorials online that show how to use Netstat and Tasklist to find an intruder on your computer. But with a few PowerShell functions, it's possible for a hacker to evade detection from the almighty command line.

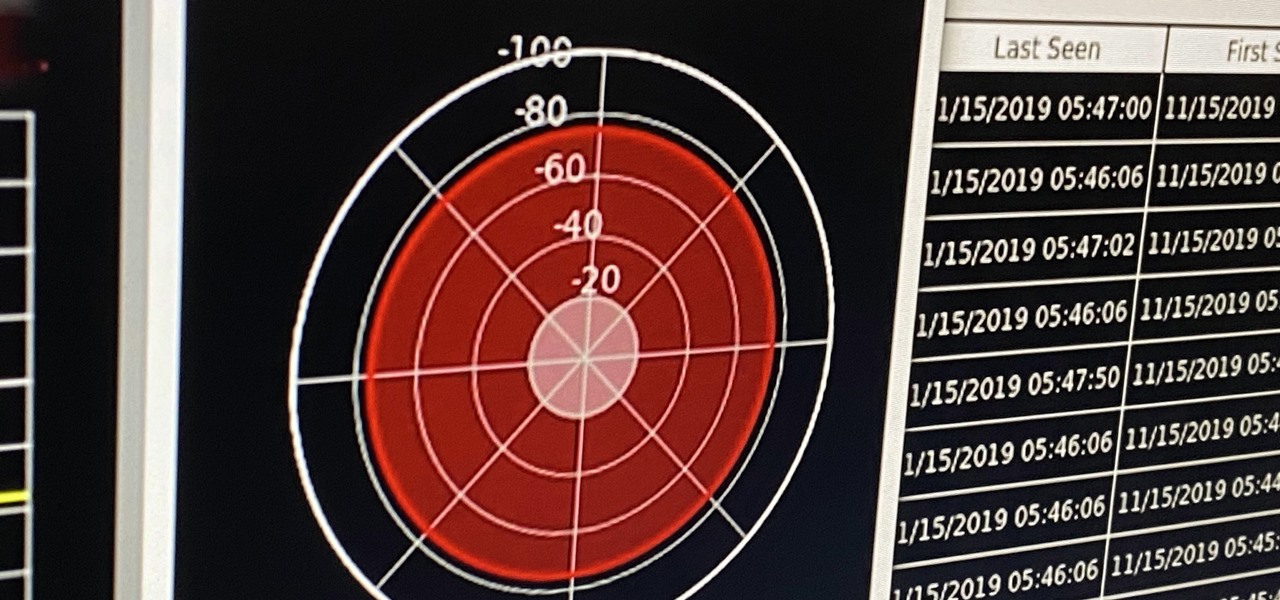
If you're ever in a situation where you need to take a peek at the wireless spectrum, whether it's for Bluetooth or Wi-Fi devices, there's a fascinating Python 3-based tool called Sparrow-wifi you should check out. It's cross-platform, easy to use, and has an impressive GUI that shows you the signal strength of nearby devices.

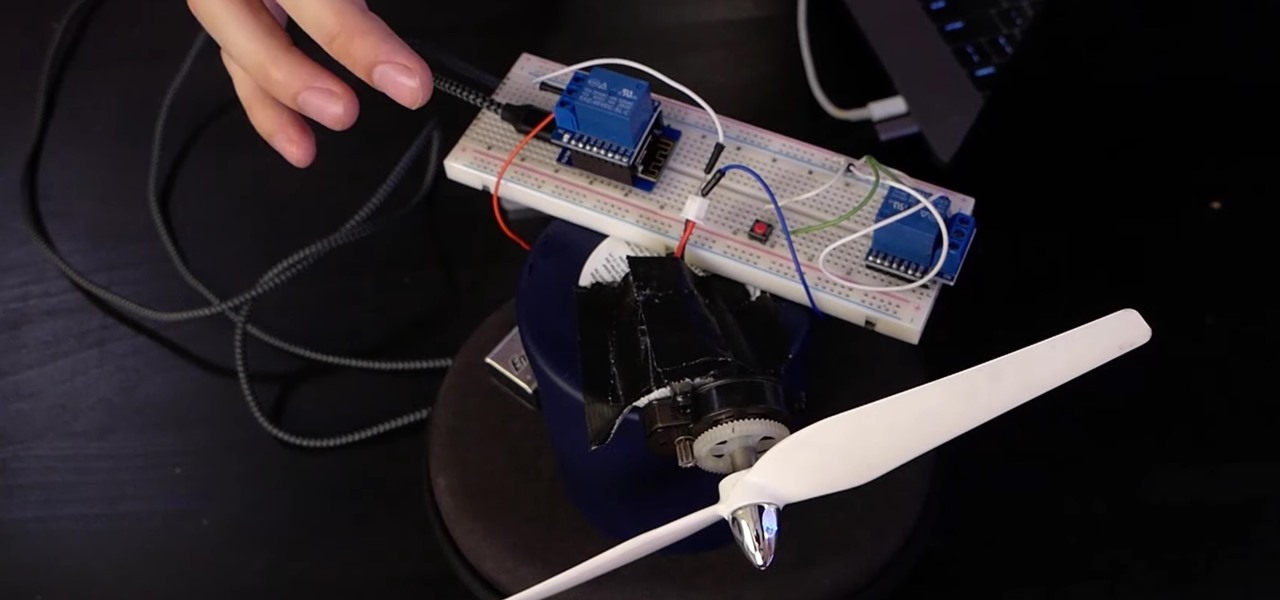
If you want to control electronic devices, such as a relay or motor, you can do so using MicroPython with an ESP8266 and web browser. Usually, you'd program an ESP8266 using Arduino, but C++, which Arduino uses, is not always the easiest programming language for beginners to learn.

The internet has undoubtedly changed the way we work and communicate. With technological advances, more and more people can collaborate on the web from anywhere in the world. But this remote-friendly environment inherently brings security risks, and hackers are always finding ways to exploit systems for other uses.

In the case of Apple Watch v. Fitbit, the winner comes down to the judge at hand. Apple currently offers two smartwatches — the Series 5 and the Series 3 — while Fitbit offers three models — the Fitbit Versa 2, Fitbit Ionic, and Fitbit Versa Lite. Whatever your assumptions about these devices are, throw them out the window, as each has something unique to bring to the table.

If you have a modern iPhone, you have an excellent video recorder at your disposal. Every iPhone since the 6S has the ability to shoot in 4K resolution, and each new iteration has brought new capabilities to the table. But even the best mobile shooter can use a little extra help. That's where these video recording apps come into play, to ensure the footage you capture is as good as can be.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

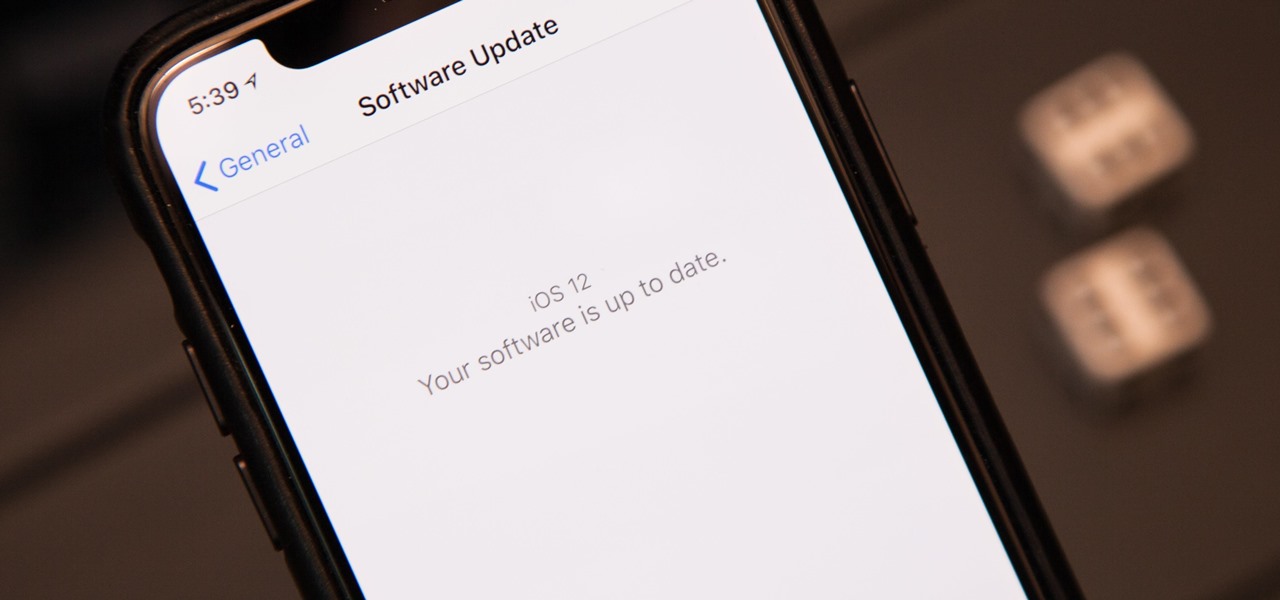
The next big iOS version for iPad, iPhone, and iPod touch was revealed by Apple at WWDC 2018 and dropped for everyone on Sept. 17, 2018, less than a week after Apple revealed the new iPhone lineup. We've rounded up all the big picture items and secret features and changes we could find so you know exactly what to expect when updating to iOS 12 on your iPhone.

Welcome to the first annual Next Reality 30, our list of people who've made the biggest impact on the augmented reality space in the last 12 months — and what a 12-month roller-coaster ride it's been. Apple introduced ARKit-powered apps last fall, Google launched ARCore for Android soon after, Snapchat began monetizing AR, and the Magic Leap One headset finally came out. These are historic times.

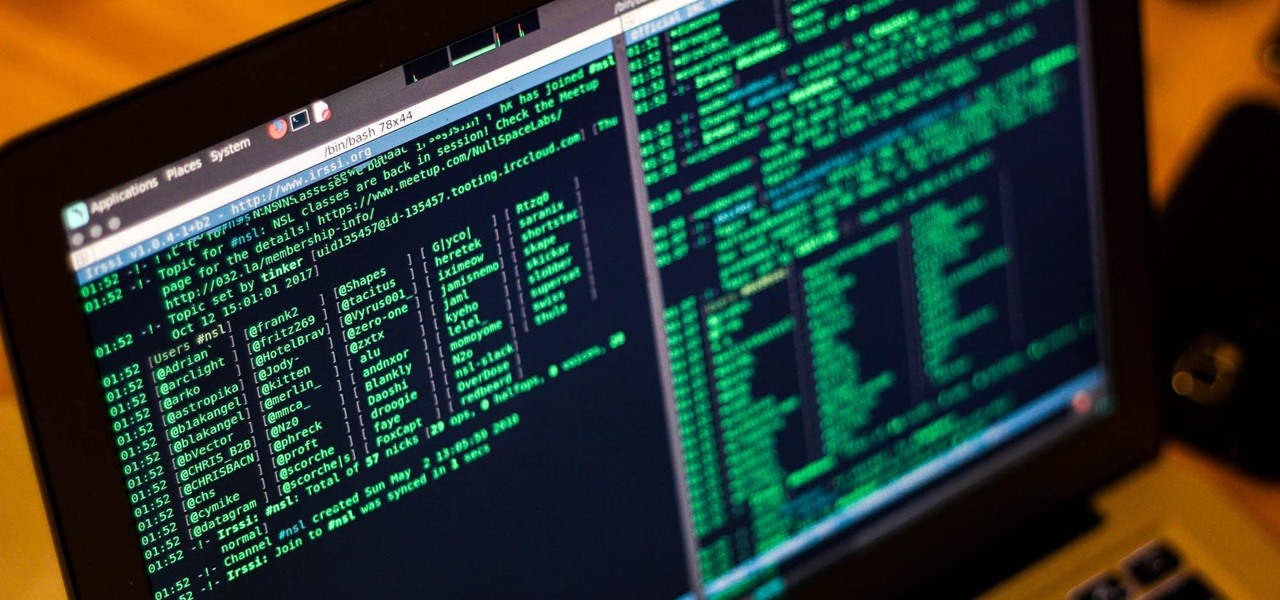
Internet Relay Chat, or IRC, is one of the most popular chat protocols on the internet. The technology can be connected to the Tor network to create an anonymous and secure chatroom — without the use of public IP addresses.

A PirateBox creates a network that allows users to communicate wirelessly, connecting smartphones and laptops even when surrounding infrastructure has been disabled on purpose or destroyed in a disaster. Using a Raspberry Pi, we will make a wireless offline server that hosts files and a chat room as an educational database, a discreet local chat room, or a dead-drop file server.

What began as a regional specialty has turned into a national trend that looks like it's here to stay: Nasvhille hot chicken has caught on like wildfire, with hot chicken restaurants popping up across the country—not to mention the 8 hot chicken restaurants that you can find in Nashville alone! The history of this Deep South dish is fascinating, and you can read more about it here.

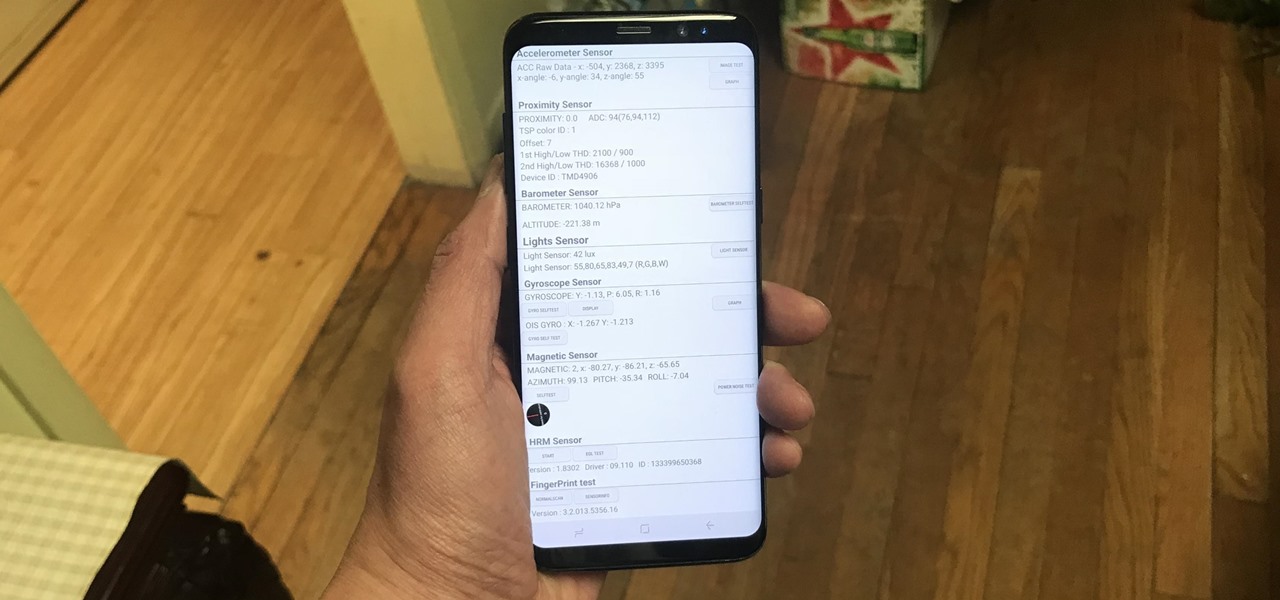
Besides obvious features like a touchscreen and biometric sensors, the modern smartphone comes with an array of state-of-the-art hardware in the form of various sensors that help your device sense the environment around it. And if you have a Samsung handset, chances are, you have a handy feature built in that enables you to check if these sensors are functioning 100 percent.

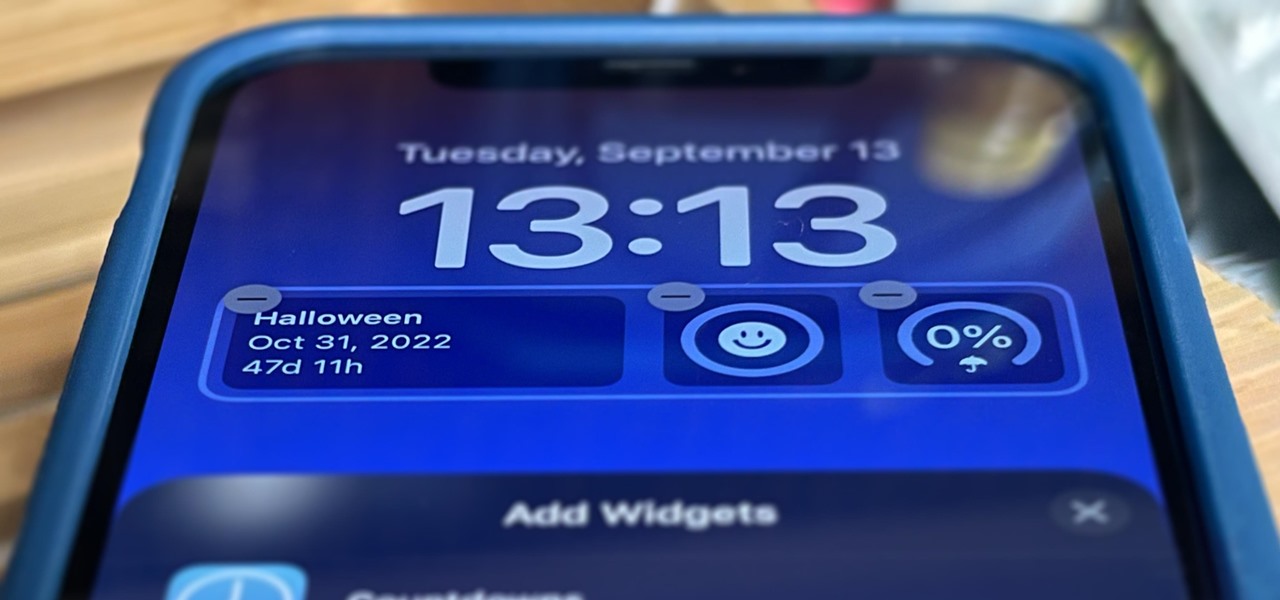
Apple's just ushered in a new era for widgets on your iPhone. With the iOS 16 update, each of your lock screens can have up to five widgets. While Apple's apps were the first to get lock screen widgets, third-party developers can code their own ones into their apps — and here's a list of every app we know so far that does.

Your days as an ordinary Muggle are over — as long as you have an iPhone. With just a word or two, you can use your iPhone and newfound Muggle-born powers to cast spells or utilize charms just like Harry Potter and team. Only your "wand" is from Apple, not Ollivanders in Diagon Alley.

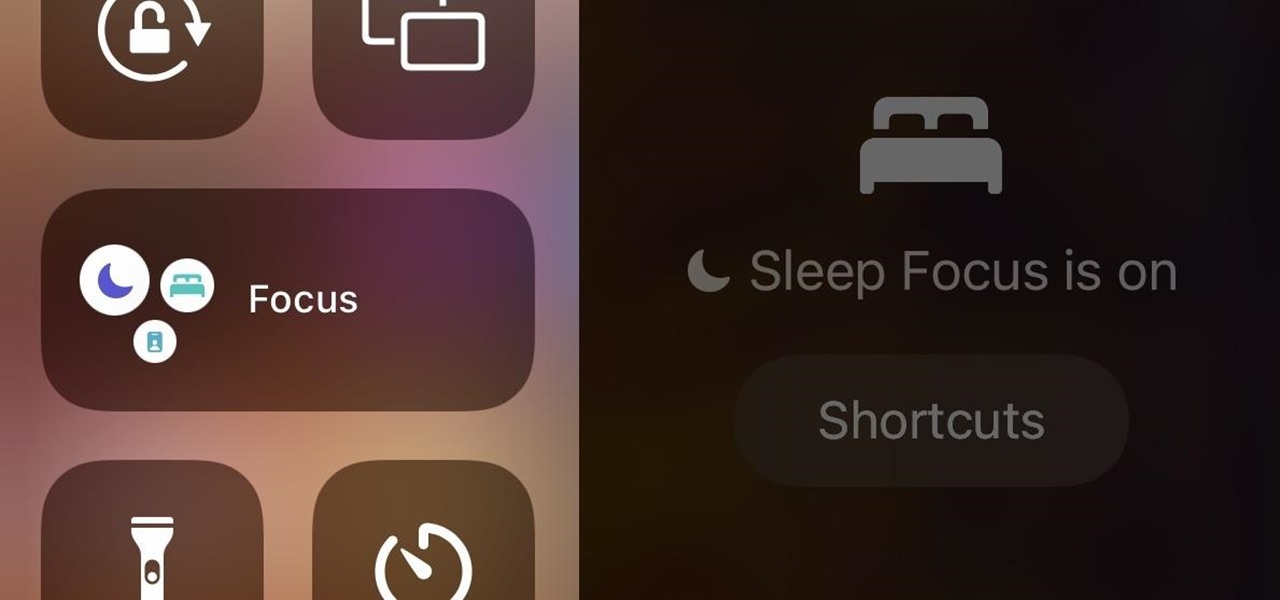
In iOS 15, Apple unveiled a new feature called Focus, an extension of Do Not Disturb that lets you focus on the one thing that's important at any particular moment. It does so by minimizing distractions from your iPhone and other Apple devices, but there's a lot you should know about setting up and using Focus on your iPhone or iPad before you dig in.

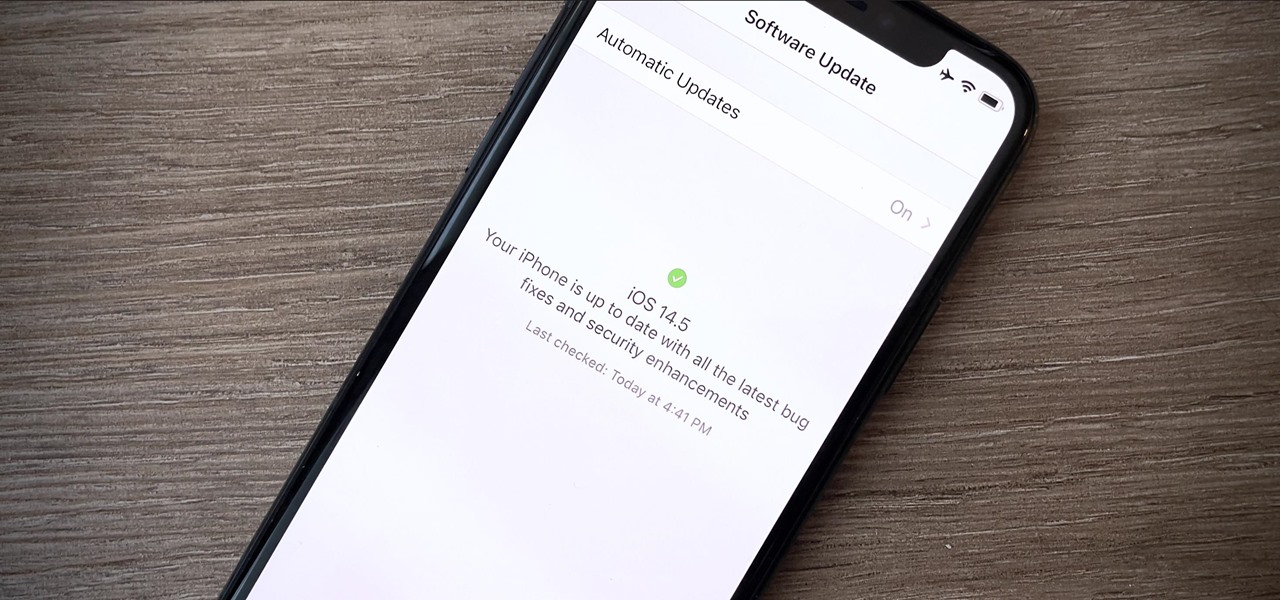
Your iPhone is full of features, many of which you might not even know about yet. Still, Apple keeps adding feature after feature with each new iOS update, and iOS 14.5 is no exception. The latest iOS version adds at least 69 features for your iPhone that you should be happy about.

Cases and stickers are always great, but they aren't the only way to customize an iPhone. The software on your device is full of customization options, from a better-looking home screen and cooler lock screen wallpapers to app icon changes and a system-wide dark mode. There's literally over 100 ways to make iOS on your iPhone genuinely unique, some of which are hiding in plain sight.

Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings change, interface update, or hidden improvement.

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.

It's not Keebler or Nabisco that rules the cookie market. It's your daughter. It's your next door neighbor's niece. It's that uniform-clad girl with the badges on her chest sweetly smiling at you in front of Walmart, trying to get you to buy some cookies for her organization.

Can you handle it? I'm not entirely sure I can, but my taste buds are definitely curious. Soft, doughy chocolate chip cookies stuffed with Nabisco's sugary sweet Oreos. This joins the ranks with: deep-fried trick-or-treat candy, deep-fried butter, deep-fried cheesecake... you get the idea.

A shortbread cookie is made from sugar, butter, salt and flour. Because the dough is so simple, you can use cookie cutters to cut them into fun shapes and then decorate. A great recipe to bring to any party or potluck. Make traditional shortbread cookies for decorating.

Chocolate chip cookies are always a crowd-pleaser, not to mention it's some of the easiest baking you can do.

You don't need to invest in a bakery to get the sort of professional looking cookies you want! All you need are a few tools, some more implements you probably already have, and a few basic decorating techniques to get beautifully decorated cookies! Decorate sugar cookies just like a professional.

A delicious dessert for your Valentine's Day dinner! For this recipe, you will need: 3 sticks of butter, 1 cup granulated sugar, 1 large egg, 3 1/2 cups flour, 1/4 teaspoon salt, 1 teaspoon vanilla extract, 1 cup thick raspberry preserved, confectioner's sugar (powdered sugar), parchment paper, a stand mixer, a sheet pan, plastic wrap, a round cookie cutter and a heart shaped cookie cutter. Make raspberry filled, nut free Linzer cookies.

You can cut these out in fancy shapes, or just leave them as simple round cookies. This recipe calls for: 3 sticks unsalted butter, 1 1/3 cups granulated sugar, 2 teaspoons kosher salt, 3 large egg yolks, 2 tablespoons vanilla and 3 3/4 cups all purpose flour. Make a basic sugar cookie.

A great holiday treat! For the cookies, you will need: 2 cups all purpose flour, 1/3 cup sugar, 1 teaspoon salt, 1/2 teaspoon baking soda, 1 teaspoon cinnamon, 1 1/2 teaspoons ground ginger, 1/2 teaspoon ground cloves, 1 teaspoon nutmeg, 1/4 cup hot water, 1 cup molasses, 1/2 cup melted butter and 1 egg. Bake delicious gingerbread men cookies.

Making icing is a really simple process, even this recipe for royal icing, which is definitely a must for Christmas cookies. Royal icing makes it easy to decorate holiday cookies for parties or for (and with) you kids. This kind of icing is a staple for decorating your families favorite cookies.

Got lots of pretty cookies to share with friends and family during the holidays? While it's true you could hand them off in tins as is, it's so much more fun to experiment with packaging and favor ideas.

In this video tutorial, viewers learn how to block third party cookies in AOL 8.0 for Windows. Begin by opening AOL. Click on Settings, go to Preferences and select Internet Properties (WWW), which is located under the Organization column. Then click on the Privacy tab and click on the Advanced button. Check the "Override automatic cookie handling" box and select Block under Third-party cookies. Finish by clicking OK. This video will benefit those viewers who use AOL 8.0 and would like to lea...

Your perfect home-baked chocolate chip cookie may be thick and chewy, or crispy and thin, or something in-between. With a little cooking know-how and experimentation, you can adjust the different ingredients and cooking steps in the baking process to create the perfect chocolate chip cookie that best suits your particular sweet tooth preferences.

I will illustrate a simple, yet effective way to stop tracking and third-party cookies without installing any additional software on your computer. Third-party cookies are often used to track your visits and activities on webpages and can slow down your browser and hinder your privacy. They are often the most common detected adware or spyware installed on most computers.

When you're baking your cookies this holiday season with the children, try something that's both beneficial to your family and your guests— cookies that also act as sweet party favors. Dani tells you what to do in order to transform your Christmas cookies into beautiful holiday treats— tasty, take-home ornaments. Decorate your centerpiece with them before having guests take their favorite home for an easy, affordable way to be an innovative holiday host! Make homemade Christmas cookies as tre...