Finding an instrumental or karaoke version of a song can be pretty easy unless you're dealing with a song that isn't popular. That leaves you with just the full version of the song, complete with vocals. So how do you convert it into an instrumental or karaoke track?

There are countless tutorials online that show how to use Netstat and Tasklist to find an intruder on your computer. But with a few PowerShell functions, it's possible for a hacker to evade detection from the almighty command line.
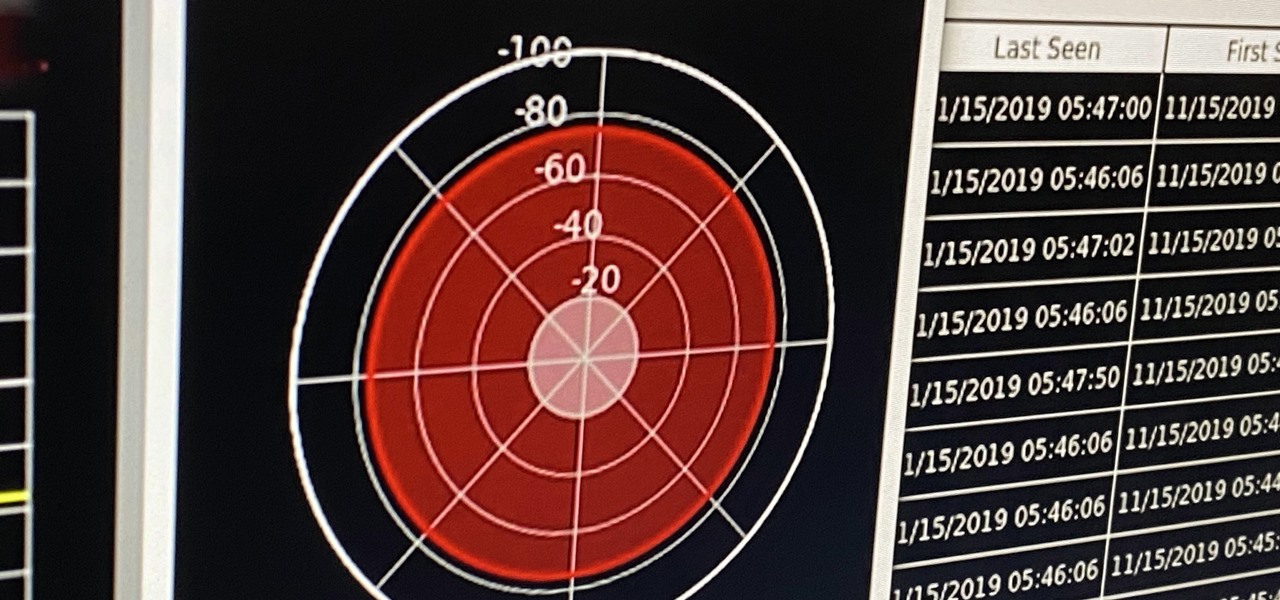
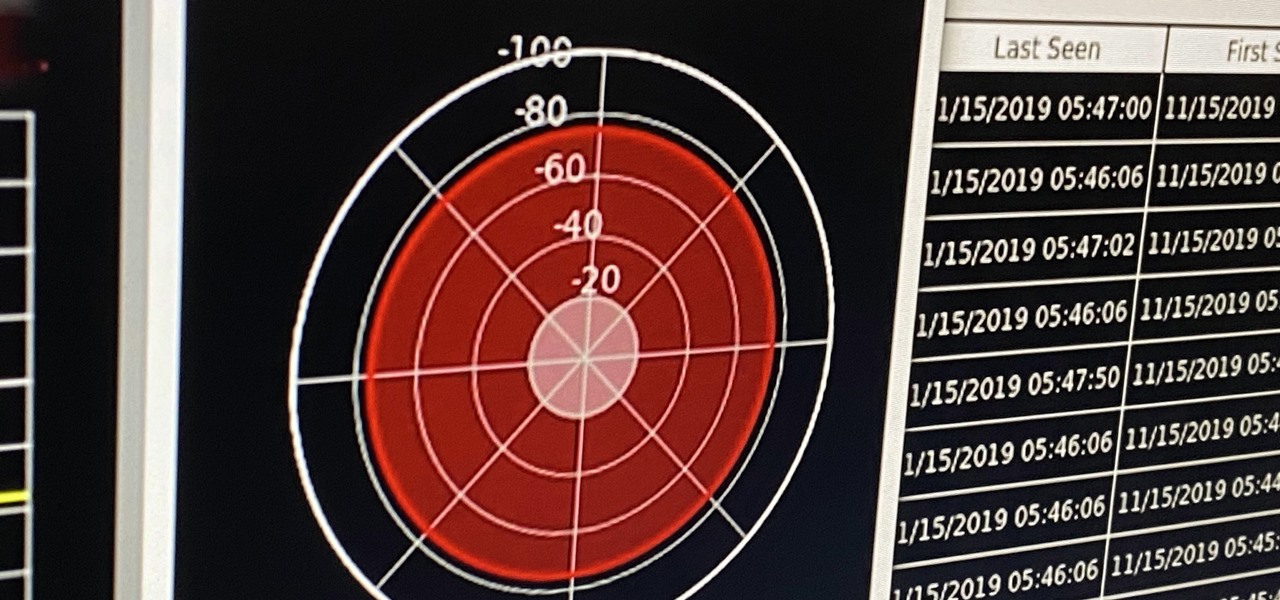
If you're ever in a situation where you need to take a peek at the wireless spectrum, whether it's for Bluetooth or Wi-Fi devices, there's a fascinating Python 3-based tool called Sparrow-wifi you should check out. It's cross-platform, easy to use, and has an impressive GUI that shows you the signal strength of nearby devices.
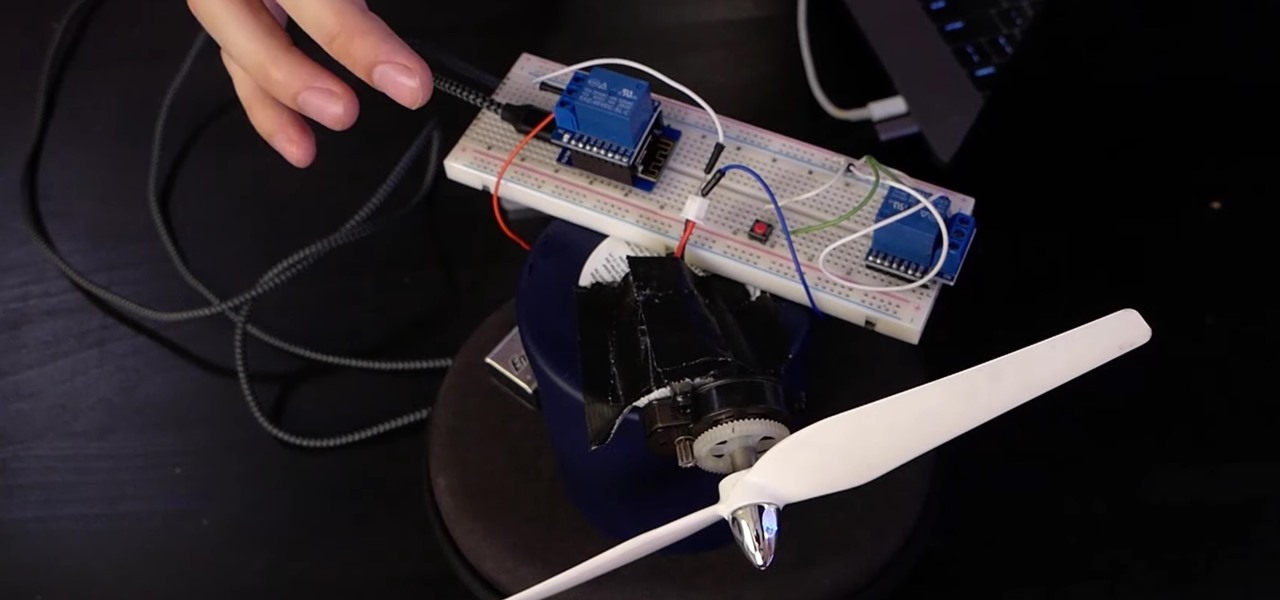
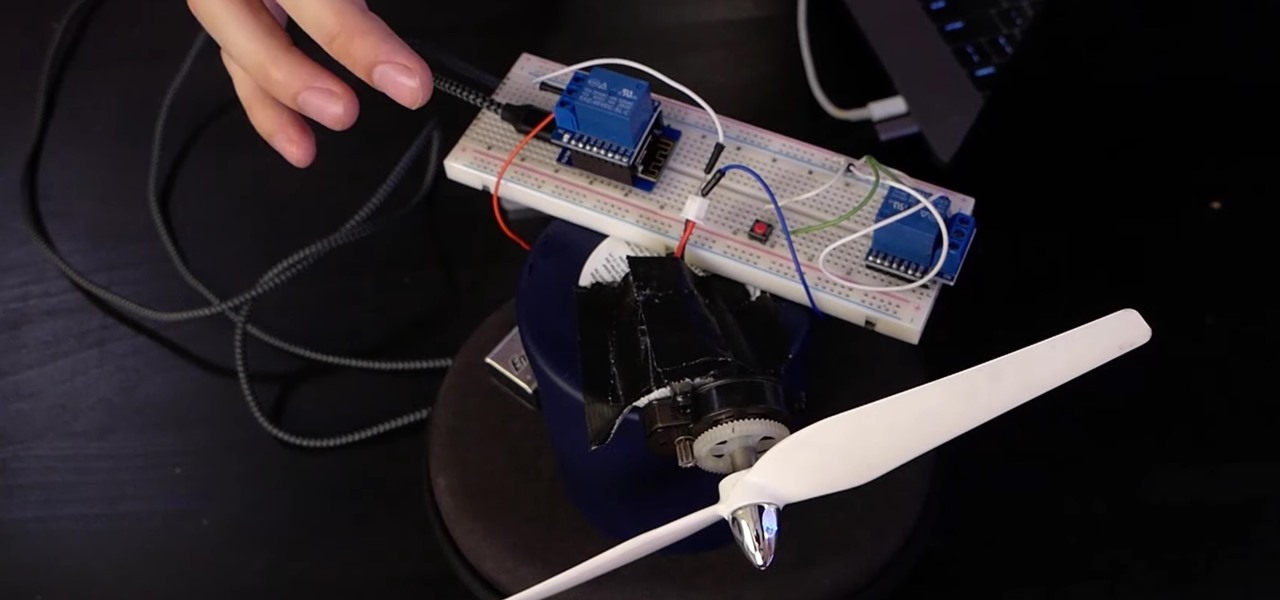
If you want to control electronic devices, such as a relay or motor, you can do so using MicroPython with an ESP8266 and web browser. Usually, you'd program an ESP8266 using Arduino, but C++, which Arduino uses, is not always the easiest programming language for beginners to learn.
The internet has undoubtedly changed the way we work and communicate. With technological advances, more and more people can collaborate on the web from anywhere in the world. But this remote-friendly environment inherently brings security risks, and hackers are always finding ways to exploit systems for other uses.

In the case of Apple Watch v. Fitbit, the winner comes down to the judge at hand. Apple currently offers two smartwatches — the Series 5 and the Series 3 — while Fitbit offers three models — the Fitbit Versa 2, Fitbit Ionic, and Fitbit Versa Lite. Whatever your assumptions about these devices are, throw them out the window, as each has something unique to bring to the table.

If you have a modern iPhone, you have an excellent video recorder at your disposal. Every iPhone since the 6S has the ability to shoot in 4K resolution, and each new iteration has brought new capabilities to the table. But even the best mobile shooter can use a little extra help. That's where these video recording apps come into play, to ensure the footage you capture is as good as can be.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Welcome to the first annual Next Reality 30, our list of people who've made the biggest impact on the augmented reality space in the last 12 months — and what a 12-month roller-coaster ride it's been. Apple introduced ARKit-powered apps last fall, Google launched ARCore for Android soon after, Snapchat began monetizing AR, and the Magic Leap One headset finally came out. These are historic times.

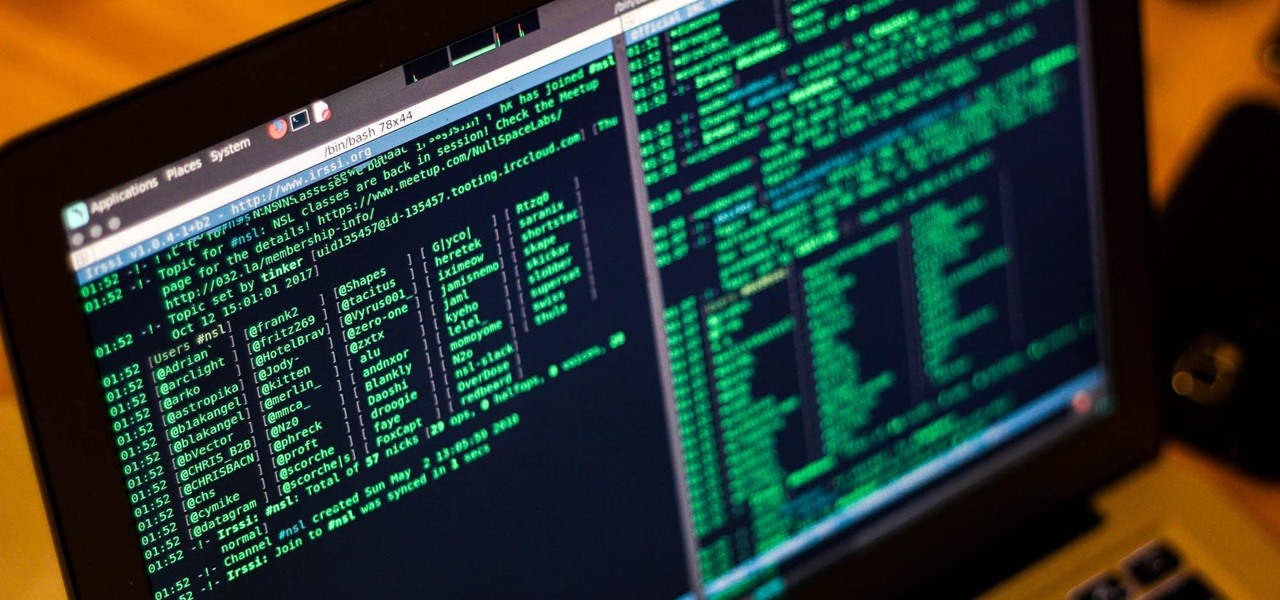
Internet Relay Chat, or IRC, is one of the most popular chat protocols on the internet. The technology can be connected to the Tor network to create an anonymous and secure chatroom — without the use of public IP addresses.

Apple's iOS 11 is finally here, and while they showed off several of the new features it brings to your iPhone, iPad, and iPod touch back at WWDC 2017, they've only just touched the surface of what iOS 11 has to offer. There are a lot of cool new (and sometimes secret) features to explore, so we've collected them all here for you.

A PirateBox creates a network that allows users to communicate wirelessly, connecting smartphones and laptops even when surrounding infrastructure has been disabled on purpose or destroyed in a disaster. Using a Raspberry Pi, we will make a wireless offline server that hosts files and a chat room as an educational database, a discreet local chat room, or a dead-drop file server.

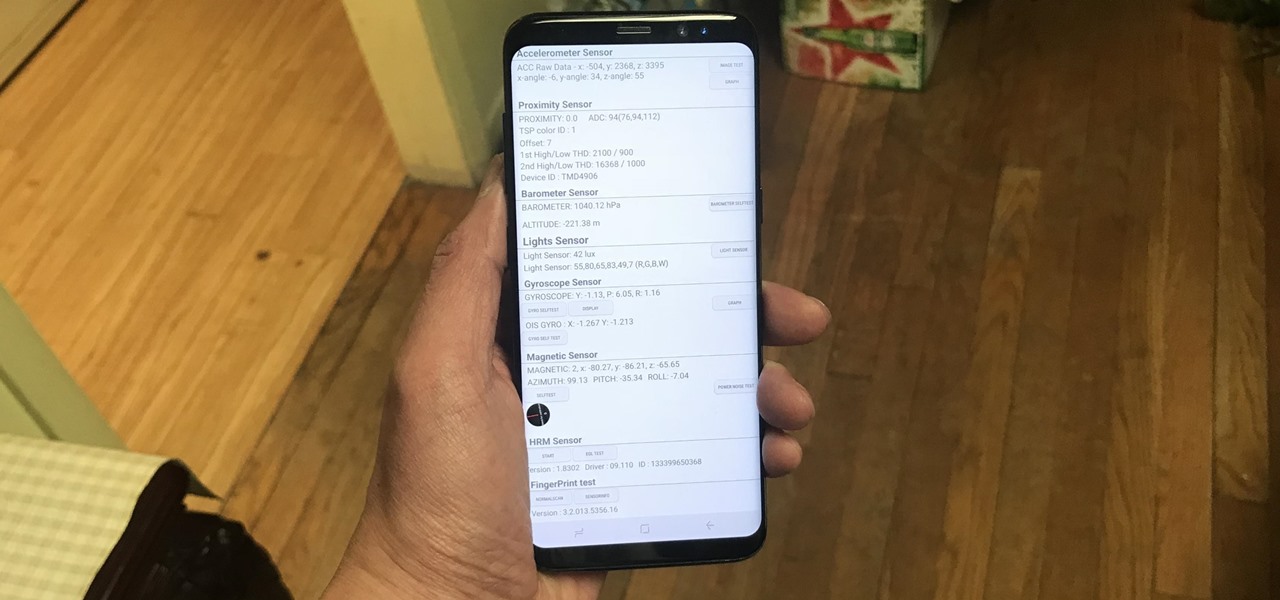
Besides obvious features like a touchscreen and biometric sensors, the modern smartphone comes with an array of state-of-the-art hardware in the form of various sensors that help your device sense the environment around it. And if you have a Samsung handset, chances are, you have a handy feature built in that enables you to check if these sensors are functioning 100 percent.

Your days as an ordinary Muggle are over — as long as you have an iPhone. With just a word or two, you can use your iPhone and newfound Muggle-born powers to cast spells or utilize charms just like Harry Potter and team. Only your "wand" is from Apple, not Ollivanders in Diagon Alley.

In the 21st century, we're all looking for ways to stay private, especially on our electronic devices. We have big tech corporations, enemy countries, malicious hackers, and other prying eyes watching our every move, so it's only natural to want to limit what they can see. Making your web browsing experience on iPhone and iPad more private is one way to do that.

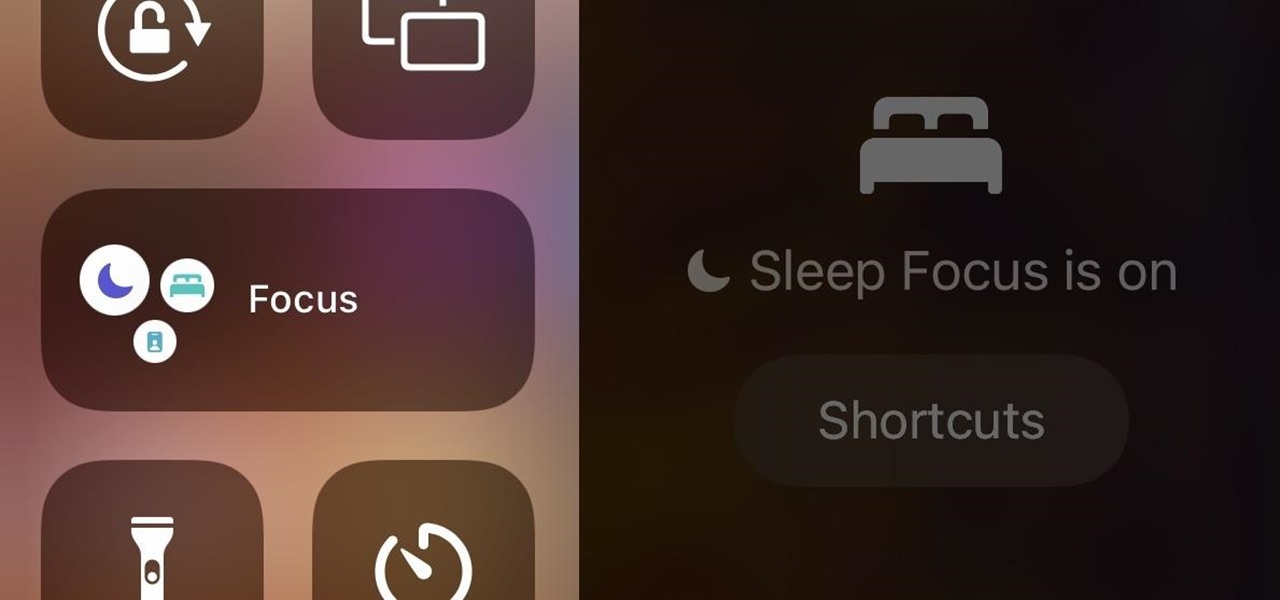
In iOS 15, Apple unveiled a new feature called Focus, an extension of Do Not Disturb that lets you focus on the one thing that's important at any particular moment. It does so by minimizing distractions from your iPhone and other Apple devices, but there's a lot you should know about setting up and using Focus on your iPhone or iPad before you dig in.

Cases and stickers are always great, but they aren't the only way to customize an iPhone. The software on your device is full of customization options, from a better-looking home screen and cooler lock screen wallpapers to app icon changes and a system-wide dark mode. There's literally over 100 ways to make iOS on your iPhone genuinely unique, some of which are hiding in plain sight.

Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings change, interface update, or hidden improvement.

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.

Do not ever laugh or shrug off what medical bottles or boxes give you as side effects or warnings. All of the side effects and warnings are put on the medication for a purpose. Priapism is a topic we all laugh or giggle about but it is a very serious emergency problem.

Here is the movie trailer for the feature film "Love and Other Drugs" Here are 6 clips from the film Love and Other Drugs
Multiple airport screeners have been arrested for allegedly taking handsome bribes to look the other way while loads of illegal drugs slipped through security at Los Angeles International Airport, federal officials announced today.
The Minnesota Department of Public Safety issued a press release today announcing the suspension of a drug recognition program conducted by the Minnesota State Patrol. The program was exposed earlier this month by activists and members of Communities United Against Police Brutality in Minneapolis.

Though it's unlikely you'll ever have a need for hostage survival skills, it never hurts to take in a few tips on what to do in the event of being accosted by Somali pirates off the Horn of Africa. Wired has tracked down a HowTo guide that addresses such a scenario. Though most of the advice is fairly general, one important point addresses the dangers of lighting up with the enemy:

This weekend in a jungle estuary, the DEA and local Ecuadorian police seized a prototype narco sub that may be the most sophisticated one yet. Complete with air conditioning and periscope, this 100 foot creation would have carried a more cocaine tonnage than any previously captured narco sub. To give you a perspective on the resourcefulness of these outlaws, consider this. A U.S. Navy Virginia Class attack submarine will run around $2.8 billion. But a drug lord in Cartagena would make you one...

In this tutorial, Dr. Coral Arvon tells us how to support a relative through substance abuse. If you have a loved one who is suffering from an addiction to drugs or alcohol, you need to know that if they are using they are probably lying to you. If you are giving them money, they will most likely be using that for drugs or money. They will do anything to get what they want, including lie and manipulate. You need to try your best to get your loved one into a 12-step program or into a detox cen...

Hair loss is not a final destination. You can do something about it. Learn how to make your hair grow! If you're one of the millions who suffer from alopecia or hair thinning, learn your options.

Top-Windows-Tutorials is a great site dedicated to Windows tutorials for almost all things Windows. Whether you are a computer novice or an expert in Windows operating systems, you'll find useful information in these guides catering to your level of expertise. These user friendly and easy to follow free Windows tutorials will show you all that you can do with your Windows PC.

Top-Windows-Tutorials is a great site dedicated to Windows tutorials for almost all things Windows. Whether you are a computer novice or an expert in Windows operating systems, you'll find useful information in these guides catering to your level of expertise. These user friendly and easy to follow free Windows tutorials will show you all that you can do with your Windows PC.

A new study from John Rogers of the University of Illinois at Urbana-Champaign promises an exciting new tech-chic addition to the world of body modification: flexible, implantable LEDs that would radiate sub-dermal luminescence. Just imagine the possibilities.

Indianapolis-based motor junkie Paul Stender and his team of vehicle modders called the Indy Boys Inc have created the ultimate anti-fuel economy: a school bus outfitted with a Phantom fighter jet engine, which clocks 367 mph and burns 150 gallons of fuel in just a quarter mile. Stender says:

For some of you out there, today may be a looooong Friday. But have no fear, if you've yet to furtively accomplish shaving off a few extra minutes from the office clock, there is an alternative for getting through the day: computer pharmaceuticals. Relax, moms, we're not talking illicit drugs. Computer pharmaceuticals (AKA: optical and audio illusions) are completely natural, harmless highs that promise to alter your perception and consciousness- without the risk of drugs or alcohol.

Dopamine is a neurotransmitter that motivates us to engage in rewarding activities such as eating and sex. Animals without dopamine stop eating and starve to death.
A San Diego college student who was forgotten by federal drug agents and left in a holding cell for five days without food or water or access to a toilet says he drank his own urine to survive.
From 1955 to 1975, military researchers at Edgewood were using not only animals but human subjects to test a witches' brew of drugs and chemicals. They ranged from potentially lethal nerve gases like VX and sarin to incapacitating agents like BZ.

Brad Pitt in the nuthouse with Bruce Willis, asks what drugs did they give you? What are they? Please leave your answer in the comments.
This great website has programs for drug and alcohol addiction, child services, inpatient/outpatient services, disorders, etc. Check it out!

Below is the psychedelic movie trailer for "Zardoz" Yes that is Sean Connery not Burt Renolds. This movie is essential watching to see what happens to you when you take too many drugs. <>

Video walkthrough of the Shadow mission in Grand Theft Auto 4 (GTA IV), in which Niko wastes a rival drug dealer for Little Jacob. Beat the Shadow mission in GTA IV.