You've decided you want to lose weight or build lean muscle. That's great! Now grab your smartphone. It's a valuable asset that can help you achieve your physical fitness goals, whether to improve your health or enhance your appearance, and I'm going to show you how.

If you use the Notes app on your iPhone and haven't updated to the newest software yet, you're missing out on some pretty valuable upgrades that improve smart folders, note security, collaboration, and more. So what are you waiting for?
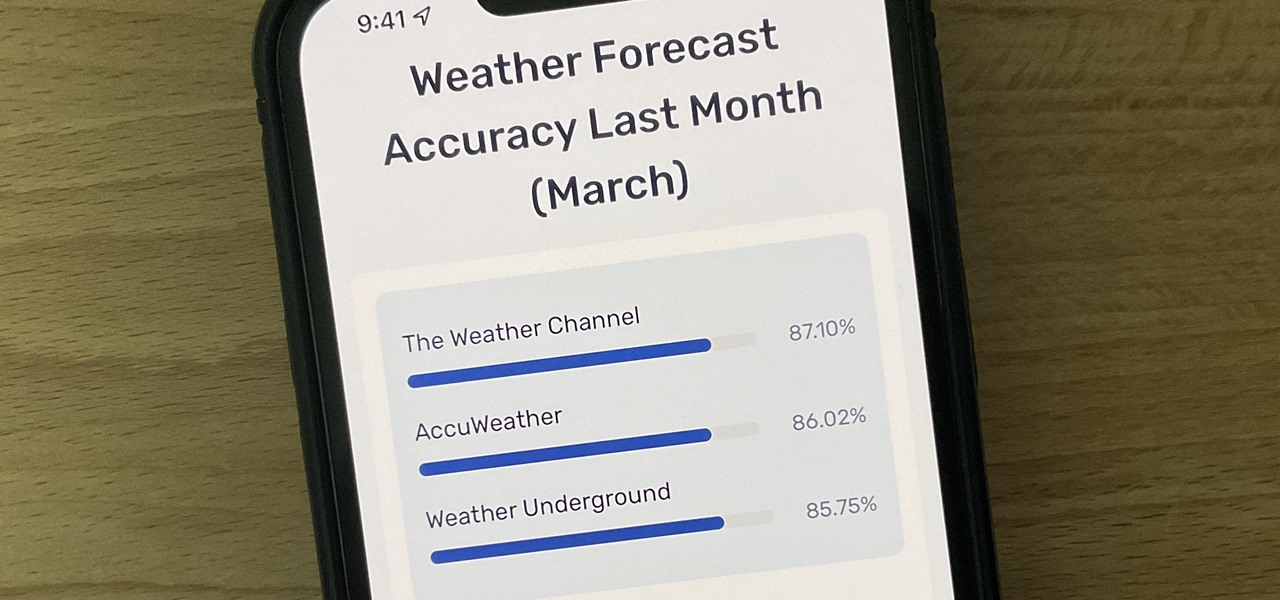
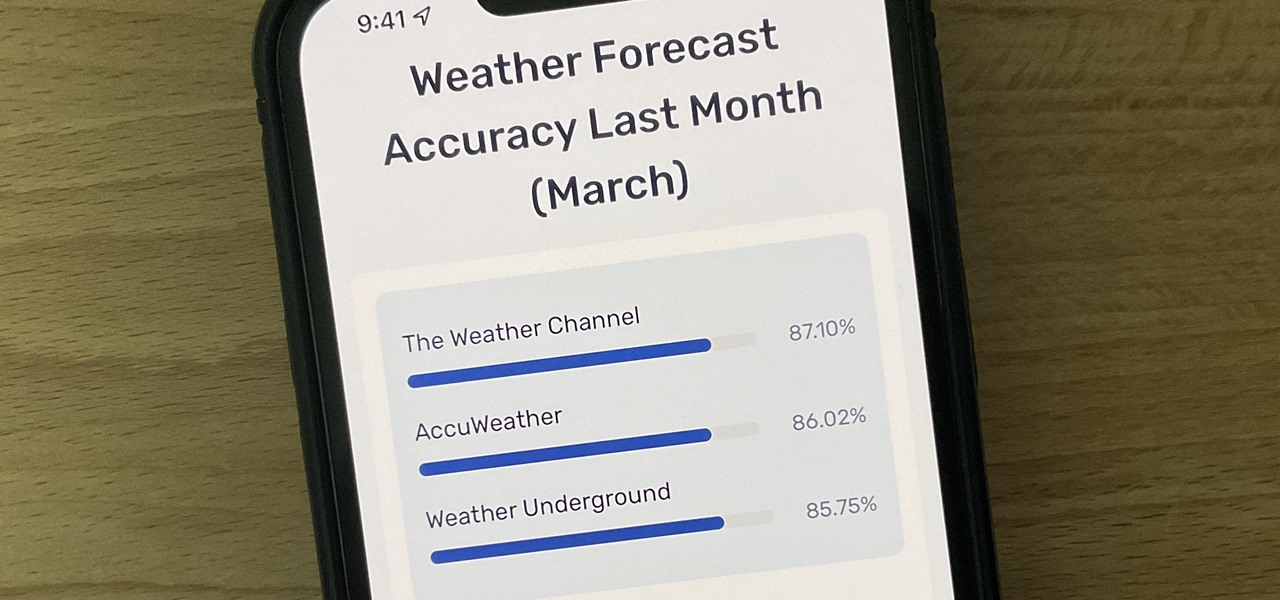
Not all weather sources are equal. When you're looking at the forecast, you hope that it's at least semi-accurate so you can plan the week and days ahead, but many sources are unreliable. And with the famous Dark Sky API shutting down on March 31, 2023, you'll need an alternative source of weather information if you use an app that utilizes that API.

Believe it or not, there are legitimate iOS apps beyond the App Store that you can install on your iPhone. Some of them even work for iPad, Apple TV, and Mac, and there are also benefits to using them over apps found in the App Store.

One of the biggest grievances with Safari on iPhone was always its lack of customization, and iOS 15's browser upgrades tackle that problem head-on. Apple added many great features, including Safari extensions, Tab Bar, and Tab Groups, but the most prominent feature caters to those obsessed with finding the perfect Home and Lock Screen look.

As a hacker, the final stage of exploitation is covering their tracks, which involves wiping all activity and logs so that they can avoid being detected. It's especially crucial for persistence if the target will be accessed again in the future by the attacker.

ESP8266-based microcontrollers can be used to create exciting and legal Wi-Fi hacking games to test your or your friends' Wi-Fi hacking skills.

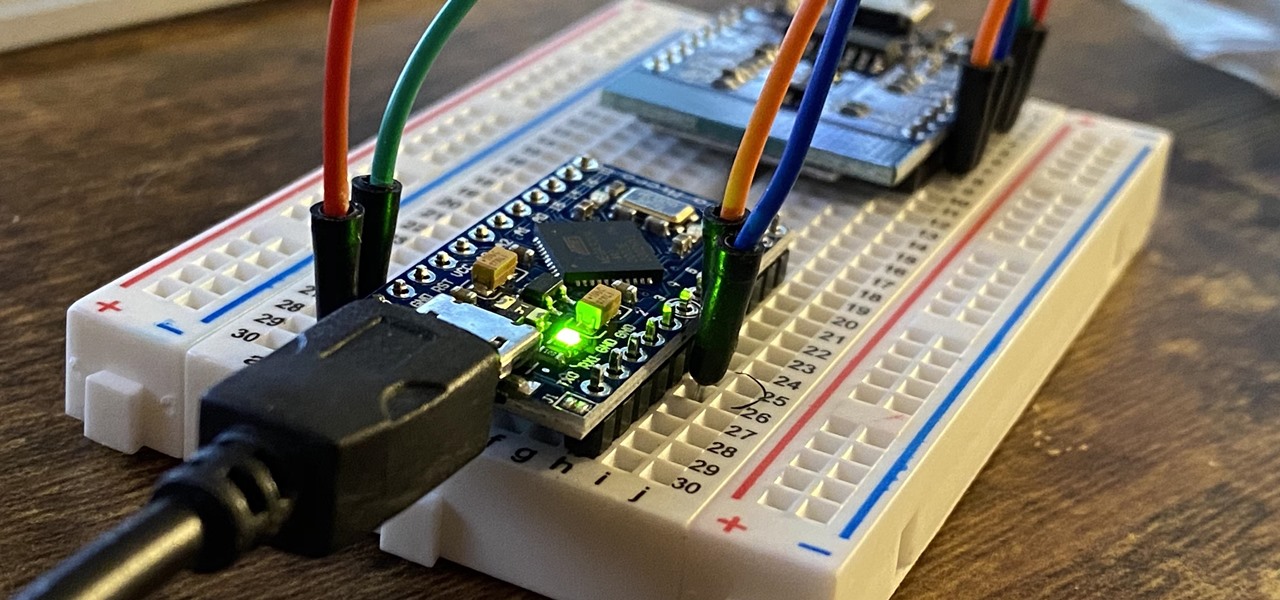
The USB Rubber Ducky is a well-known hacking device in the cybersecurity industry, but it needs to be preprogrammed before it can be used. That means it's not easy to issue commands to a target computer since you can't interact with it from afar after plugging it in. And if you don't know what the target computer is, you might come up empty. That's where the WiFi Duck comes in handy.

If it has an internet connection, it's got a huge attack surface for hackers. But what makes your phone even more dangerous is its portability and the collection of sensors it houses that can be just as good at tracking you as the camera and mic.

The art of fuzzing is a vital skill for any penetration tester or hacker to possess. The faster you fuzz, and the more efficiently you are at doing it, the closer you come to achieving your goal, whether that means finding a valid bug or discovering an initial attack vector. A tool called ffuf comes in handy to help speed things along and fuzz for parameters, directors, and more.

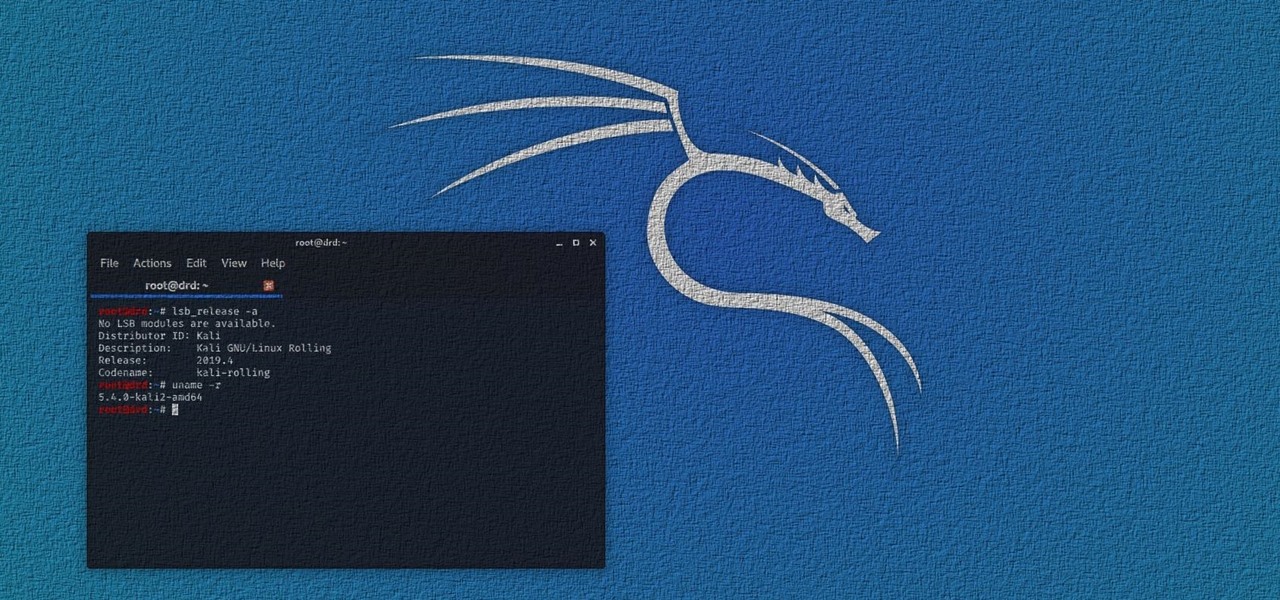
Kali Linux has come a long way since its BackTrack days, and it's still widely considered the ultimate Linux distribution for penetration testing. The system has undergone quite the transformation since its old days and includes an updated look, improved performance, and some significant changes to how it's used.

Smartphones are vital travel companions. While you're on the go, they connect you with loved ones back home, help you find tickets and passes for tourist attractions, and make it easy to find your way through foreign roads — but even the most powerful smartphone could use help from travel accessories.

If we were to assign a theme for the 2019 edition of the Next Reality 30 (NR30), it might be something along the lines of, "What have you done for me lately?"

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.

Ports allow network and internet-connected devices to interact using specified channels. While servers with dedicated IP addresses can connect directly to the internet and make ports publicly available, a system behind a router on a local network may not be open to the rest of the web. To overcome the issue, port forwarding can be used to make these devices publicly accessible.

OpenBSD implements security in its development in a way that no other operating system on the planet does. Learning to use the Unix-like operating system can help a hacker understand secure development, create better servers, and improve their understanding of the BSD operating system. Using VirtualBox, the OS can be installed within a host to create a full-featured test environment.

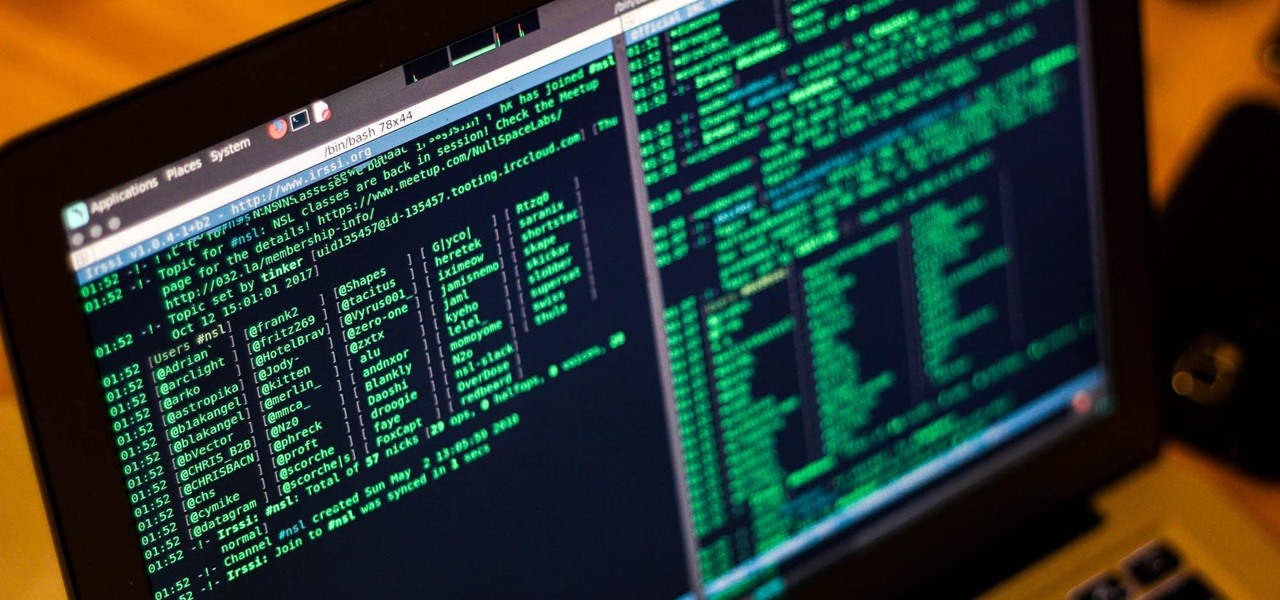
Internet Relay Chat, or IRC, is one of the most popular chat protocols on the internet. The technology can be connected to the Tor network to create an anonymous and secure chatroom — without the use of public IP addresses.

The private automobile has been an intrinsic part of our lives for around a hundred years. But over the last decade, car sharing has gained a very small but growing part of the mobility market. The more recent rise of companies like Uber and Lyft is witness to a more dramatic shift in mobility and car ownership. Private vehicle ownership to a transportation-as-a-service model has already started, and high capability SAE Level 4 vehicles will complete this trend.

While it's not usually the first thing everyone looks at after installing a new iOS software update, I'd give the new accessibility features on your iPhone priority attention because there are some highly valuable tools that even users without disabilities can enjoy.

In the 21st century, we're all looking for ways to stay private, especially on our electronic devices. We have big tech corporations, enemy countries, malicious hackers, and other prying eyes watching our every move, so it's only natural to want to limit what they can see. Making your web browsing experience on iPhone and iPad more private is one way to do that.

Apple officially unveiled iOS 14 on June 22 at its first all-virtual WWDC. After months of beta testing, iOS 14 hit iPhones on Sept. 16, but that doesn't mean that Apple is done beta testing iOS 14. There will be new features to try out right up until iOS 15 comes out next year.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.

Weapons Plus Mod Weapons Plus Mod 1.7.2 This mod adds a lot of new weapons to the game, such as guns, swords, and more. Destroy buildings, even whole biomes with this mod! All guns have 3D Item Renderers and Models! This mod also uses 32×32 textures.

The Mechanic character class is now live in Global MapleStory (GMS), the international version of Nexon's popular free massively multiplayer online role-playing game. Celebrate the release by building a super-powerful Mechanic to call your own! No idea how to invest your skill points? No problem! The build guide excerpted below eliminates the guesswork, permitting you to focus on what matters: playing the game.

Keeping track of your money and expenses is one of the hardest things to do in life, not to mention one of the most hated things. But it's also one of the most important things. Making sure your finances are in order means keeping track of them. So watch to see how to balance a checkbook. The last thing you need is a bad check.

A senior Syrian government spokesman just confirmed his nation did indeed possess chemical weapons, and might employ them against a "foreign aggressor."

All you LARPers out there, watch and see how you can make a blue boffer sword for LARPing. This weapon passes all weapons specs as of Ragnarok XXI War Council for Eryndor.

http://www.howtogeek.com/howto/19020/microsoft-desktop-player-is-a-valuable-tool-for-it-pros/

TANK DOG!!! Most hilarious costume I've seen this year. YouTube user darkbluedrew won first place at their local Petsmart's Howl-o-ween costume contest. Complete with a real enough weapon...

In this book you can build all sorts of 'Dangerous Weapons'. I came across this youtube video of a gun made from the directions within the book.
I have axes,machine gun,fake peanus that shoot,rifles,bombs ,pistols a guide the game world at war

So You're New to Counter Strike Source? So you're new to Counter Strike Source and you want to improve your gameplay? Great. You've come to the right place.

Tesla coils are totally insane, yet undeniably captivating. And they can be used for many things, from electric painting to dueling musical battles. But one trigger happy fellow has a different use for Tesla's lightning shooting coil. A weapon.

Want to keep your money and valuables safe while traveling abroad? Play it safe and outsmart thieves by placing your money, passport, jewelry and other expensive things in unexpected places. Sew a secret inner pocket in your pants, or if that's too much work, try cutting open a tennis ball, using empty film canisters, or simply placing a small amount of money in a spare wallet while your real wallet is more concealed within your luggage or purse.

This prank starts with a small plexiglass box (about 12in X 12in X 12in) with a round hole in the top big enough for someones hand/arm. Next, Knoxville goes around collecting the other cast member's valuables (car keys, wallets, phones, etc.) and places it in the box. The kicker is, the box is filled with scorpions. A scorpion sting won't kill you, but who the hell wants to get stung by a scorpion? Knox can then look on in laughter as they try to get their valuable out of the box.

All-Star Harold Reynolds shows the proper techniques for stealing, running the bases more effectively and mastering the base paths! Baserunning is a valuable skill for earning runs and stealing bases. Steal and run the bases with Harold Reynolds.

Water leaks weaste too much of our water. The amount of water you use is measured by a water meter. Your water meter is a great way to check if your property is leaking valuable water. For more, or to get started checking for leaks with your own water meter, watch this water-conscious video how-to. Check your water meter.

In my second article of the laser weapon series (see the first part here on CO2 lasers), I'll be expanding on the potential of pulsed lasers.