JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

Hello Guys, Today I have made a script for ddosing sites with VBScript! And I don't know how you guys do it, but I've made a script that refreshes the page in a chosen amout of milliseconds. And if you want it a number of times or if you want it to go on and on. And this is a script to run it on your botnet. But again I don't know if this works on your botnet too.

Welcome back, everybody. In the previous article, we covered the ideas and concepts of well-known ports and trust exploitation in order to evade a firewall. Today, we'll be building the shell, the part that receives commands, executes them, and sends the output back to the attacker.

Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photography, payment services, and so on.

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

As we're all aware, recon is vital to a successful hack. We need to know everything we can about the target in order to perform the best possible attack. Port scanning is a basic recon concept that is introduced very early in learning proper reconnoissance. The issue with port scanning is that is makes a lot of noise. Every connection to every port will be logged. This is where stealth scanning comes in. Also known as SYN or half-open scanning, stealth port scanning is a bit quieter, and is l...

Welcome back, my hacker novitiates! In the previous two posts in this series, we looked at the basics of buffer overflows. In this post, we will look at one technique for finding buffer overflows. We will try to send random, oversized, and invalid data at a variable to see whether we can make it crash or overflow. This process is known as fuzzing. It is often the first step to developing an exploit, as we need to find some variable that is susceptible to overflowing.

Looking at homes is the fun part. But before you go house hunting, make sure you have your financial ducks in a row.

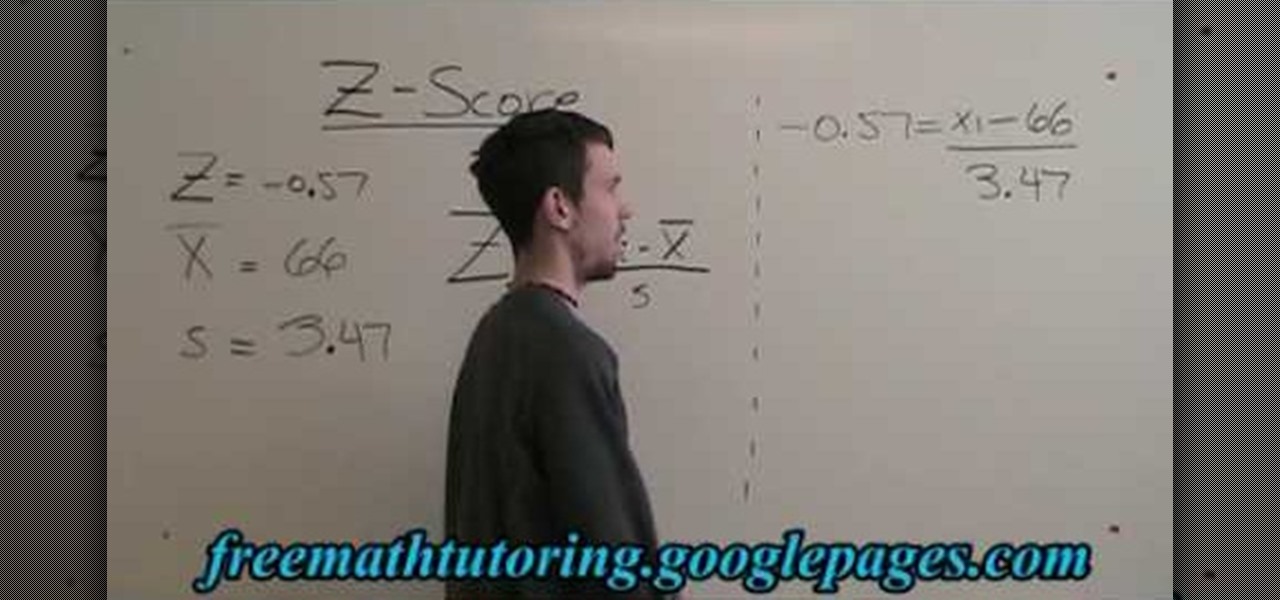
In this free video math tutorial, we learn how to use the Z-Score formula to find a data point (Xi) in statistics. With mathematics, as with anything else, not everyone progresses at the same rate. Stats is no exception. Happily, in the age of Internet video tutorials, this isn't a problem. Those who progress quickly can go beyond what's being taught them and those who are struggling likewise have all the time in the world to catch up. Whether you need help finishing your homework or studying...

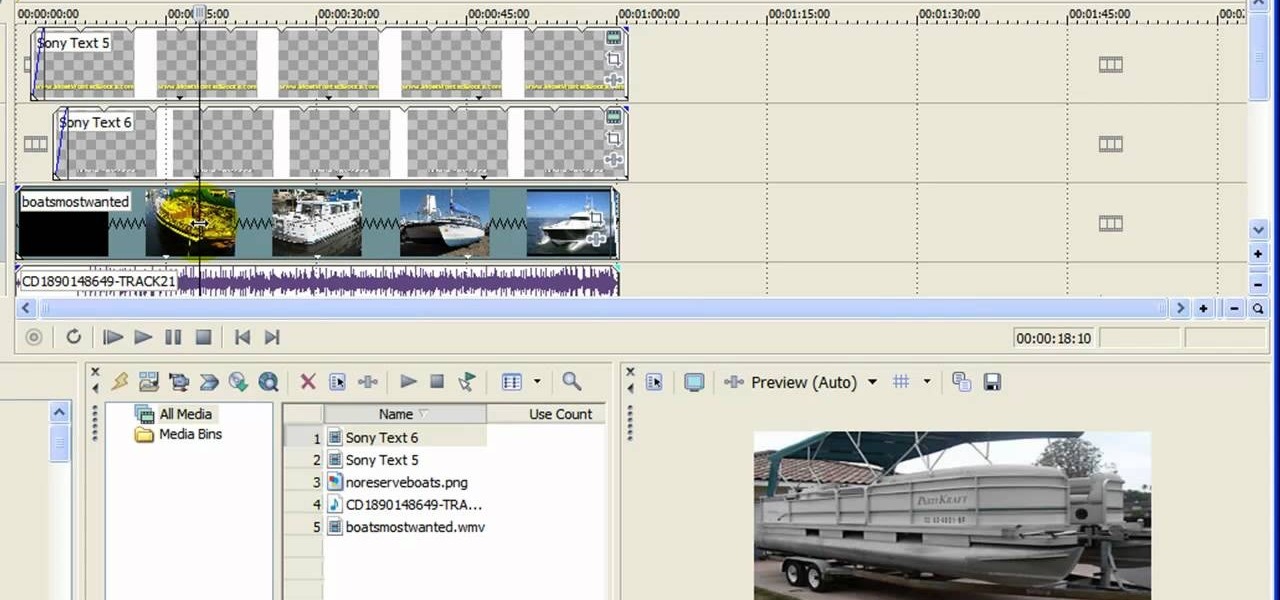
In this Computers & Programming video tutorial you will learn how to get widescreen videos on YouTube from normal videos. This can be done in Sony Vegas Movie Studio. Go to project > properties > video. Here you set the template width to 640, height 360, frame rate 30, field order as none, pixel aspect ratio to square, full resolution rendering quality to good and deinterlace method to blend fields. Next you save this template for future use and click apply. One of the quickest ways of conver...

If you're curious about how powerful your PC is, the Windows Experience Index can give you a snapshot of its capabilities and help you decide if it's good enough for you. This video will help you understand the basics of what the Windows Experience Index can do in Windows 7.

In this video, we learn how to do a grass silhouette effect in GIMP. First, draw a black mound and then close off your selection. After this, turn the path into a selection and fill it in with a black color. Next, select your smudge tool and use a small circle brush. Set the rate up to 95, depending on the length of grass you want. Now, use your mouse to push up on the mound and you will see wispy pieces of grass form where you are moving your mouse. Cross them over and cover as much of the a...

When playing sports, warming up is an integral pre-game must, and with kids, there's an entirely different approach to coaching them through warmup drills. This video will help coaches keep their team in good condition by talking about the process of teaching your youth players to successfully complete dynamic warmups. The biggest part is to prevent injury. The muscles have to be warm upped, the blood needs to flow, and the heart rate need to be up as well. See all of the necessary exercises ...

Firefighters Al Bennett and Jesse O’Quinn of the Houston Fire Department give instructions on using a fire extinguisher. Most fire extinguishers have a rating of ABC, which are suitable for most fires that occur in the home. There are also D and K fire extinguishers, but these are not commonly used in the home.

This video is a tutorial on how to arrange a dozen yellow roses for a vase. The speed of the video is increased four times faster than the normal rate of speed. The man arranging the flowers does not explain the step-by-step process of his arrangement. The viewer sees the man first arranging green leaves in the vase. Second, he dips the yellow roses into a liquid solution in a separate container before putting them into the vase. The tallest yellow rose is the center rose in the arrangement, ...

Learn how to solve the Hanayama Cast Quartet metal puzzle. Hanayama cast iron puzzles are the perfect solution to being bored. This video tutorial will show you exactly how to solve this mind boggling Cast Quartet puzzle, which is rated a 6 out of 6 in difficulty by Hanayama.

Check out this cool video where you will learn how to create the liquid rope coil effect. Honey is dribbled off the end of a chopstick into a pot below. As the falling stream stikes the pool of honey below, it turns itself into tight circular coils which rapidly begin to pile one on top of the other. A growing column of liquid coils of rope begin to emerge from above the surface of the honey in the pot in an effect referred to as the liquid rope-coil effect.

Tutorial on how to create a shutdown shortcut on the desktop to shutdown the computer when clicked. shutdown -s -t 1000 -c "comment"

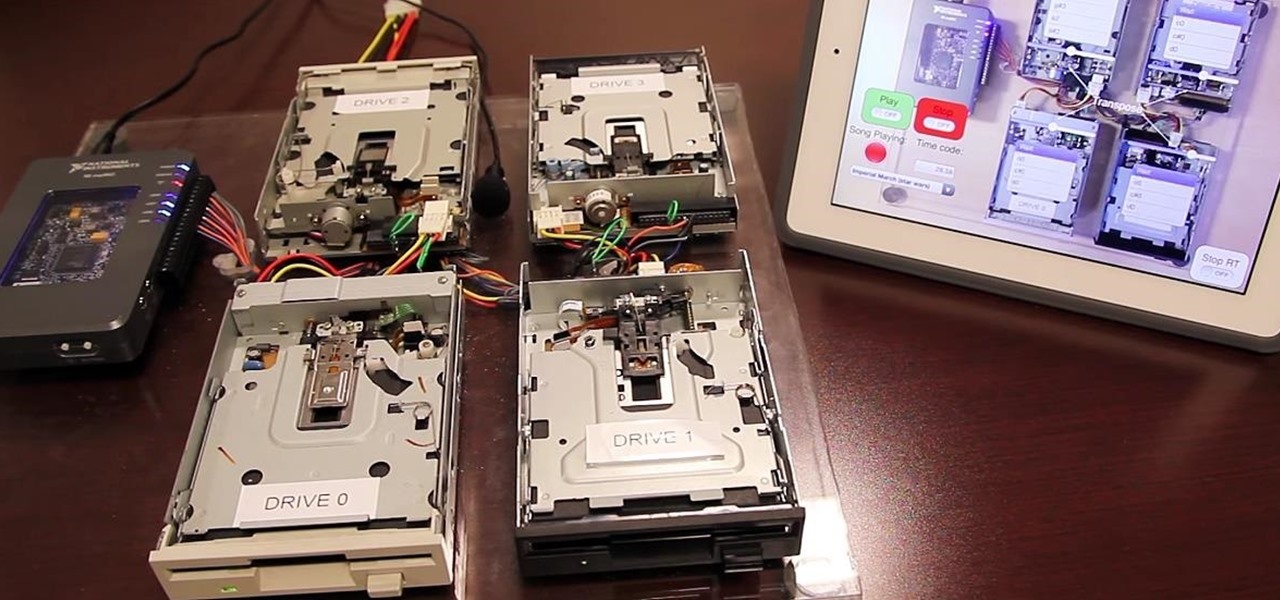
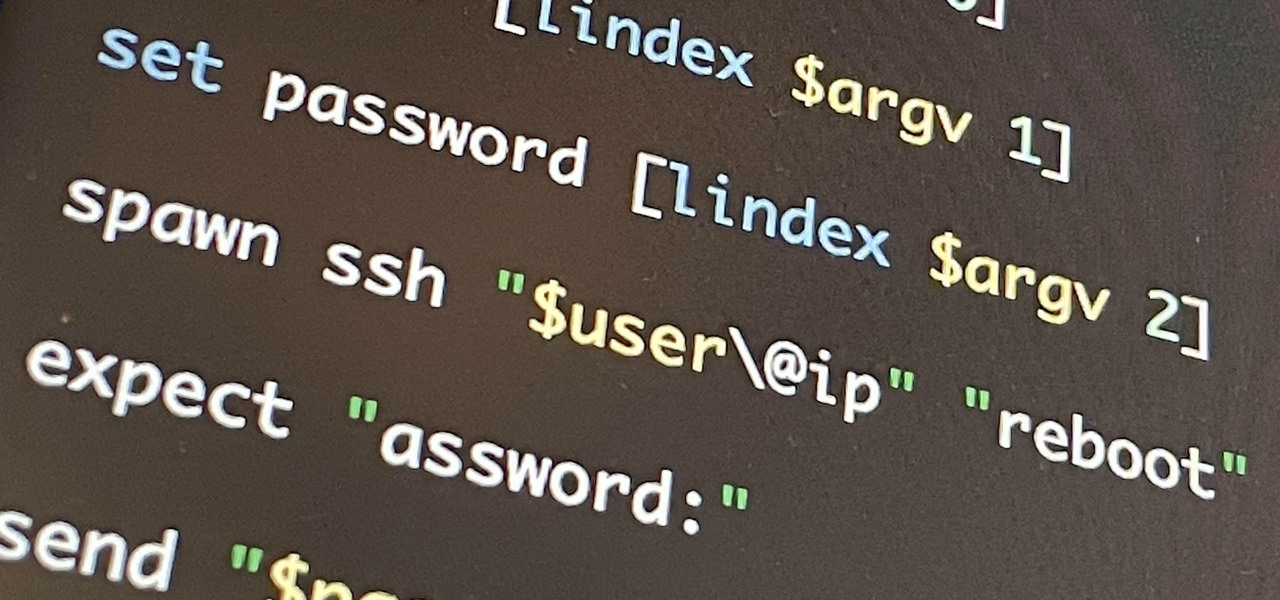
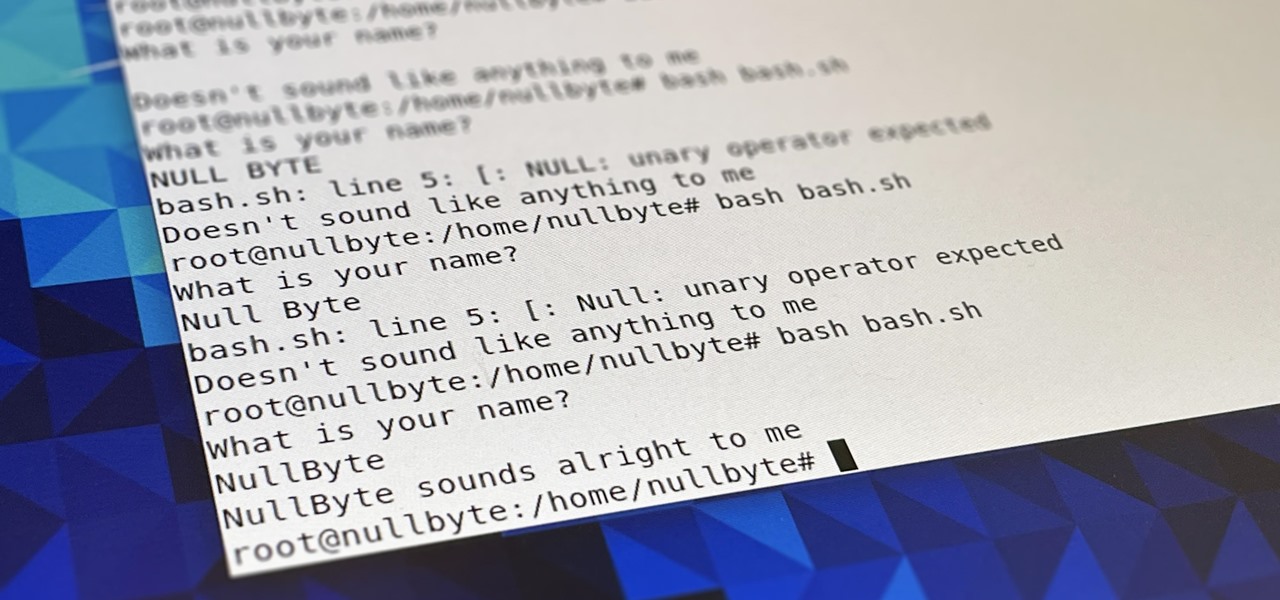
If you're getting into automation, Bash scripting is usually the way to go. However, there are a couple of limitations, and one of them is logging into another device like a Raspberry Pi and running a script automatically. To help in those situations, we're going to automate delivering an SSH payload with an "expect" script.

Bash scripting is a convenient way to automate things on any Linux system, and we're going to use it here to automate certain tasks we use all the time.

Once again, Samsung has certified its flagship Note series with an IP68 rating. With this rating, the Galaxy Note 20 and 20 Ultra have some degree of dust and water resistance.

The time to wait for an absolutely killer phone from Samsung is over. They've released a giant of a phone known as the S20 Ultra, and at least on paper, it's a grand slam. But only a few months ago, Apple released its first "Pro" iPhone, and it was giant in its own right. So which is better?

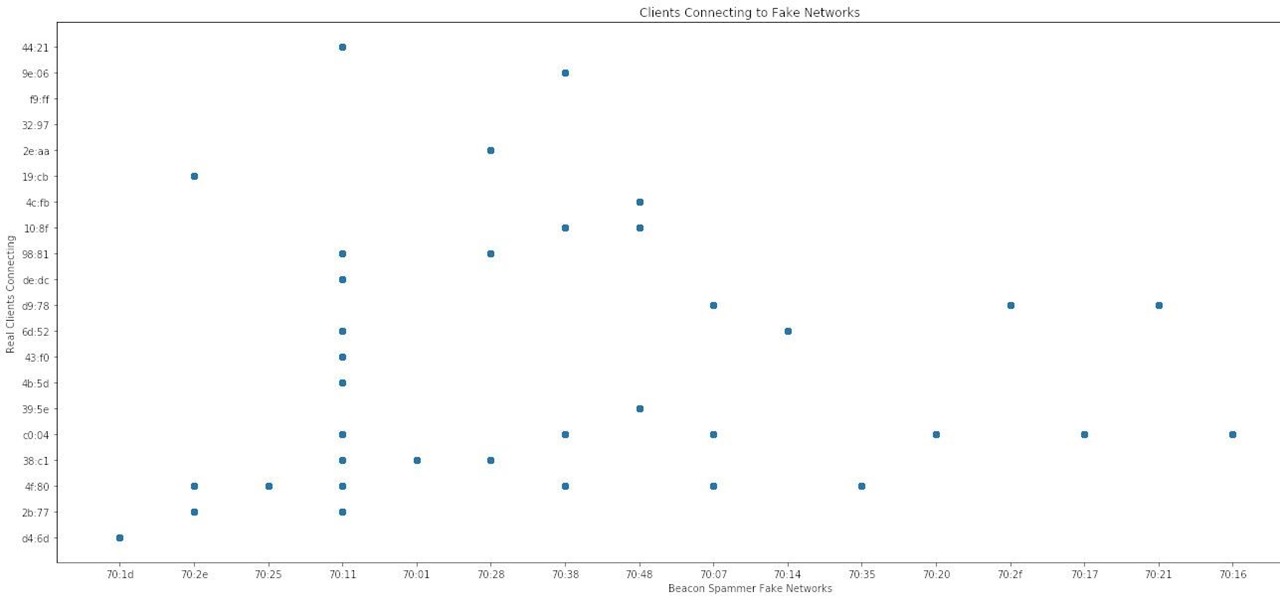
When it comes to sniffing Wi-Fi, Wireshark is cross-platform and capable of capturing vast amounts of data. Making sense of that data is another task entirely. That's where Jupyter Notebook comes in. It can help analyze Wi-Fi packets and determine which networks a particular phone has connected to before, giving us insight into the identity of the owner.

So you've been playing Call of Duty Mobile for some time but can't seem to get MVP at the end of the battle. Well, since the game is a competition of players and bots, you're in an uphill battle. But you don't have to languish at the bottom. With the help of these tips, you might just nab your first MVP.

Apple added "Announce Messages with Siri" with the release of iOS 13.2, and it came as a welcome surprise for me; I missed the feature from its initial run during iOS 13 beta testing. However, while users online gleefully showed off their newfound Announce Messages with Siri capabilities, I was frustrated to see that I didn't have the setting, even though I just updated my iPhone to 13.2. So, what's the fix?

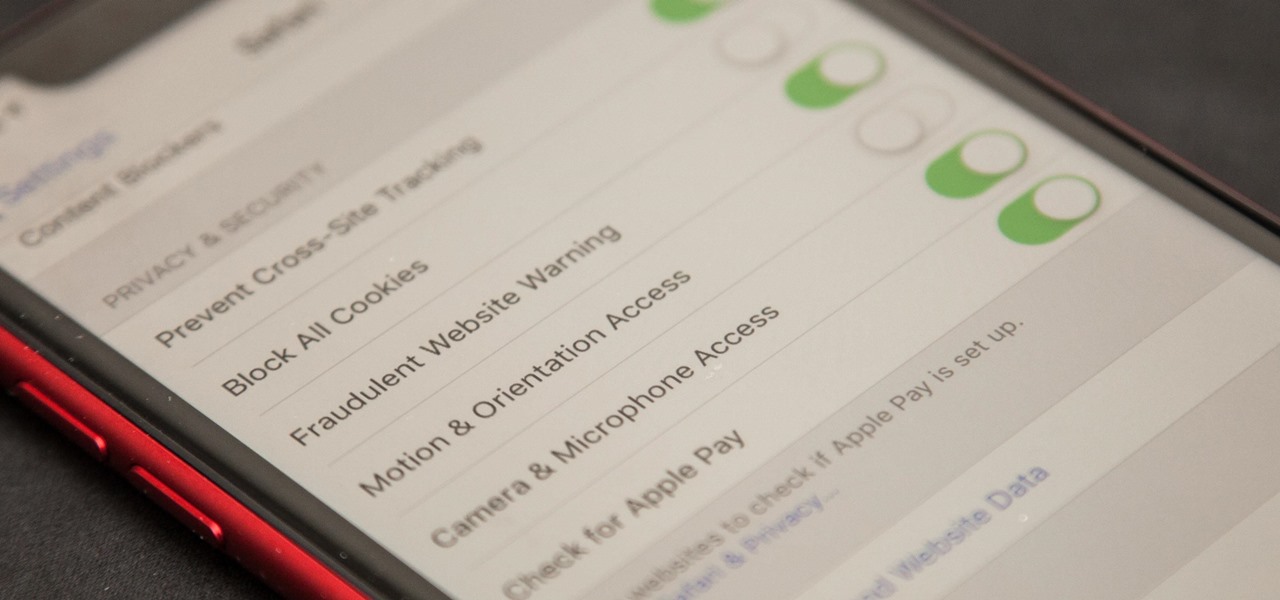
Apple first added the "Do Not Track" option to Safari in iOS 7, which sent a request to site owners and advertisers to not track your browsing activity. By tracking your activity, those third-parties could tailor content to you that you're more likely to interact with. While the feature was always opt-in, it's no longer a feature at all in iOS 12.2 on your iPhone.

In the current state of the augmented reality space, Leap Motion is the only well known name in DIY AR headset kits with its Project North Star design, which gives makers the blueprints to build their own headsets.

Designing and manufacturing waveguides for smartglasses is a complex process, but DigiLens wants us to know that they have a software solution that partially solves that problem.

For some, going to the dentist can be a terrifying experience, but a new use of augmented reality could go a long way toward making the trip feel more like it's worth the orthodontic angst.

When it comes to mobile gaming, you have a lot of fantastic options. Most flagship devices on the market, such as the Galaxy Note 8, iPhone 8 Plus, or OnePlus 5T, are perfectly capable of giving you an excellent, immersive experience. If you're looking for the ultimate way to experience Animal Crossing: Pocket Camp or something with more action like Into the Dead 2, the Razer Phone is the winner.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

While hackers adore the command line, working with the GUI (graphical user interface) of an operating system has some advantages. This is especially true when it comes to post-exploitation. When we can control the mouse and keyboard of a remote computer, we can truly say we have complete control over the device. Today, I'm going to introduce to you the PyAutoGUI module, which does just that, and just how much fun you can have with it!

About a year ago, a certain watershed mobile augmented reality game based on a familiar video game franchise was released into the wild. Today, a number of imitators and emulators have introduced their own location-based games with hopes of similar success.

Usually, the mucus lining of the female genital tract presents a barrier that helps prevent infections. But, somehow, the bacteria that causes gonorrhea gets around and through that barrier to invade the female genital tract.

Bats are an important part of the US economy. They devour metric tons of bugs every night that would otherwise ravage crops and also be generally disgusting-looking and make you itchy. But they're in danger from a nasty fungal infection called white-nose syndrome, which has just popped up in Texas and has been spreading across the country.

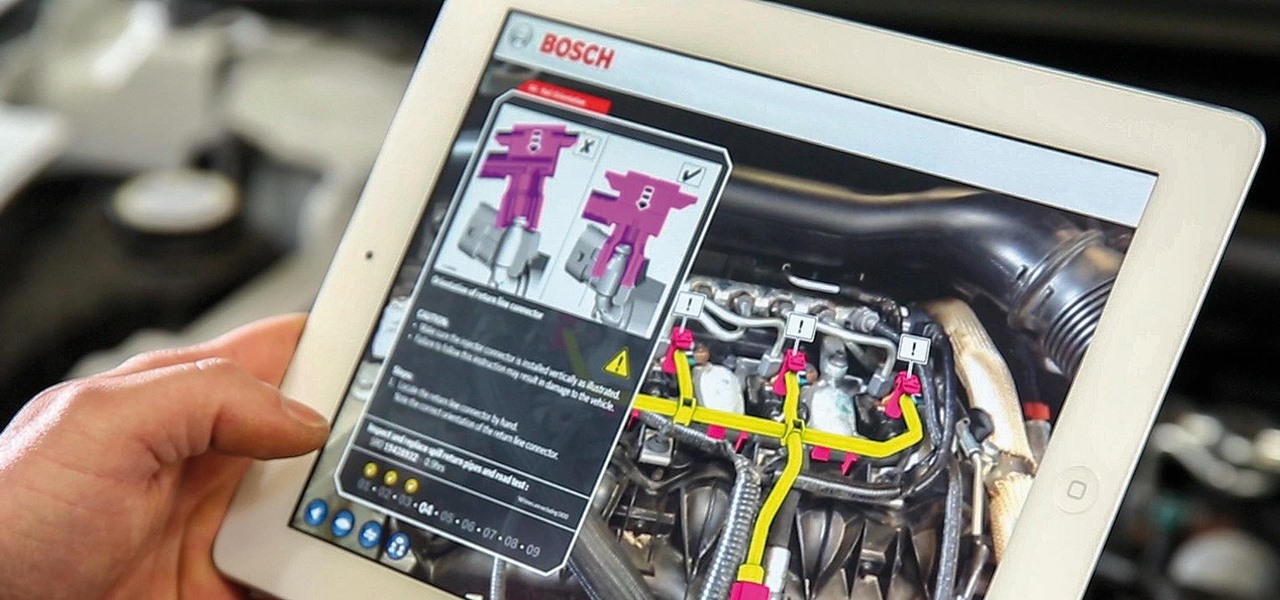
While there are many uses for augmented reality in the automotive industry, adoption has been slow. With the plethora of makes and models on the road today and rolling off assembly lines tomorrow, developing and deploying knowledge bases that utilize augmented reality to dealerships and garages can be costly and difficult to scale.

With the exception of New York, D.C., and maybe San Francisco, public transportation in the United States is downright abysmal. Like it or not, you need a car to get around. This is why Uber and Lyft have seen so much success in recent years. Both ride-sharing services get you from point A to point B in an efficient manner, and they do it without costing an arm and a leg. Well, in most cases.

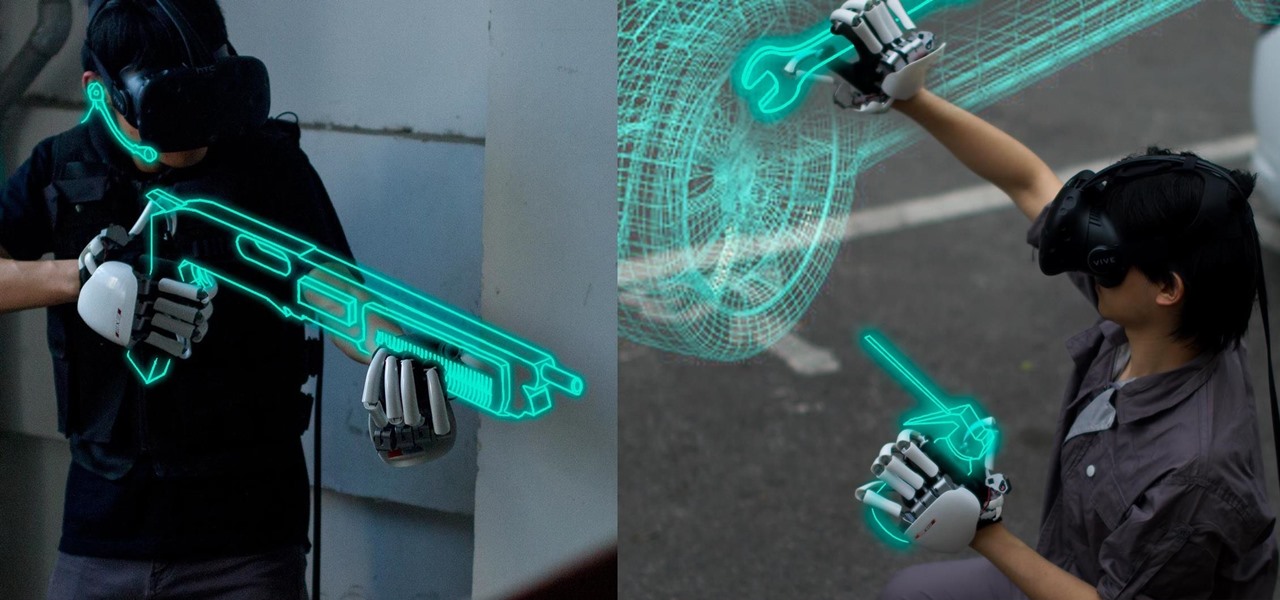
One of the disadvantages of the digital world is that you can't pick it up and touch it. While that can feel like less of a problem in virtual reality, where you're already holding controllers, mixed reality environments—like the one you'd experience in Microsoft's HoloLens—suffer from a lack of physical connection with the digital objects that appear in your real world. Dexmo aims to solve that problem with a relatively intimidating new controller that encompasses your hands.