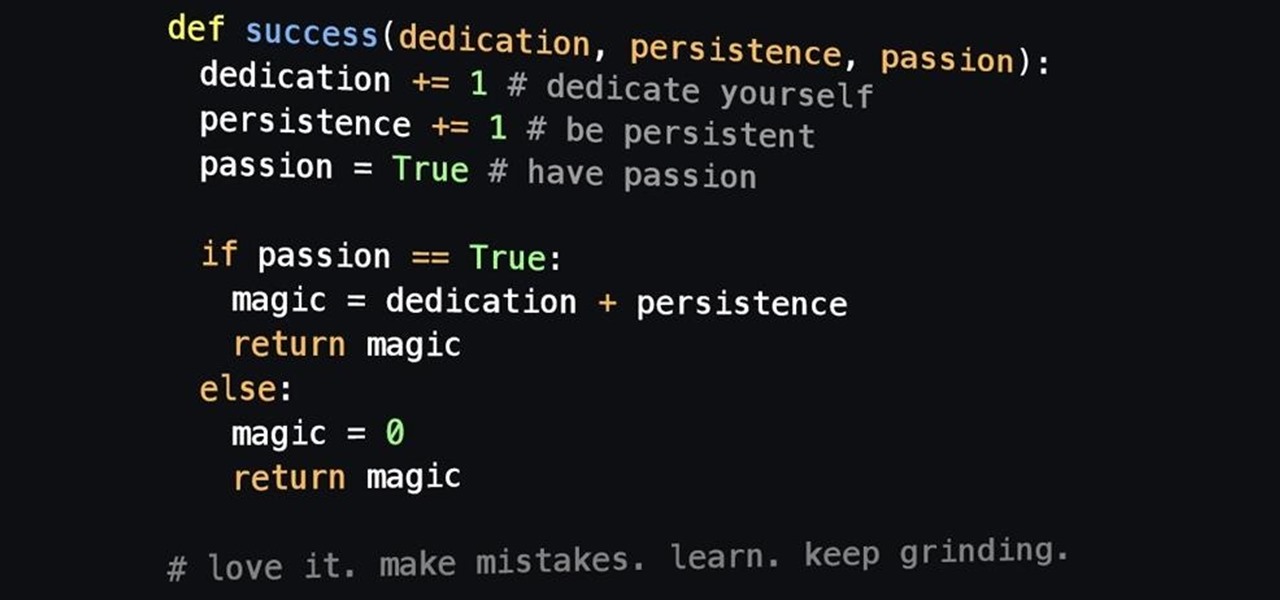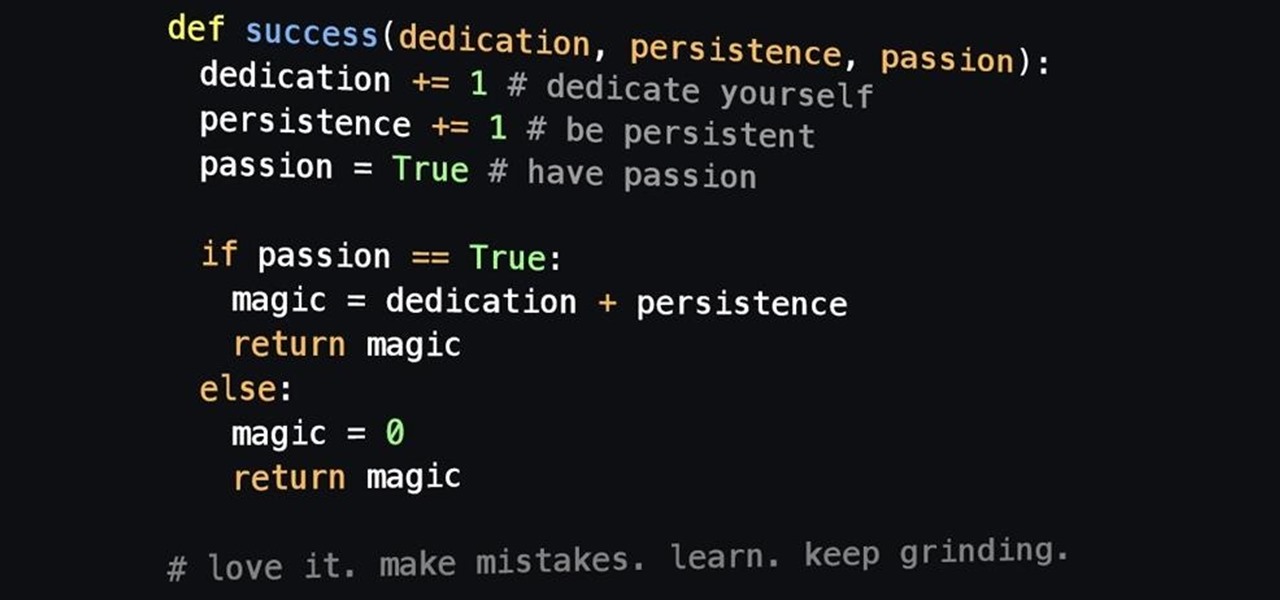
Welcome back! In the last iteration of how to train your python, we covered error detection and handling. Today we'll be diverging from this and discussing functions. More specifically, we'll be creating our own functions. First we'll need to understand exactly what a function is, then we'll get on to making our own! So, let's get started!

In this tutorial, learn to setup private properties(variables) and private methods(functions) with your PHP OOP programming. This tutorial will have the file logger run through some private methods. Check it out and open the door to the world of PHP programming.

Need help reducing radical expressions without perfect square or cube roots? Take heart: this free math lesson will ensure that you know everything you need to know for that next big test. Examples include square roots, cube roots, and 4th roots. You'll also learn a technique to simplify n-root expressions as well as how to simplify variables in radical expressions.

The leaf pattern is a variable shape in crocheting projects. Learn how to crochet a leaf pattern by watching this video handicraft tutorial.
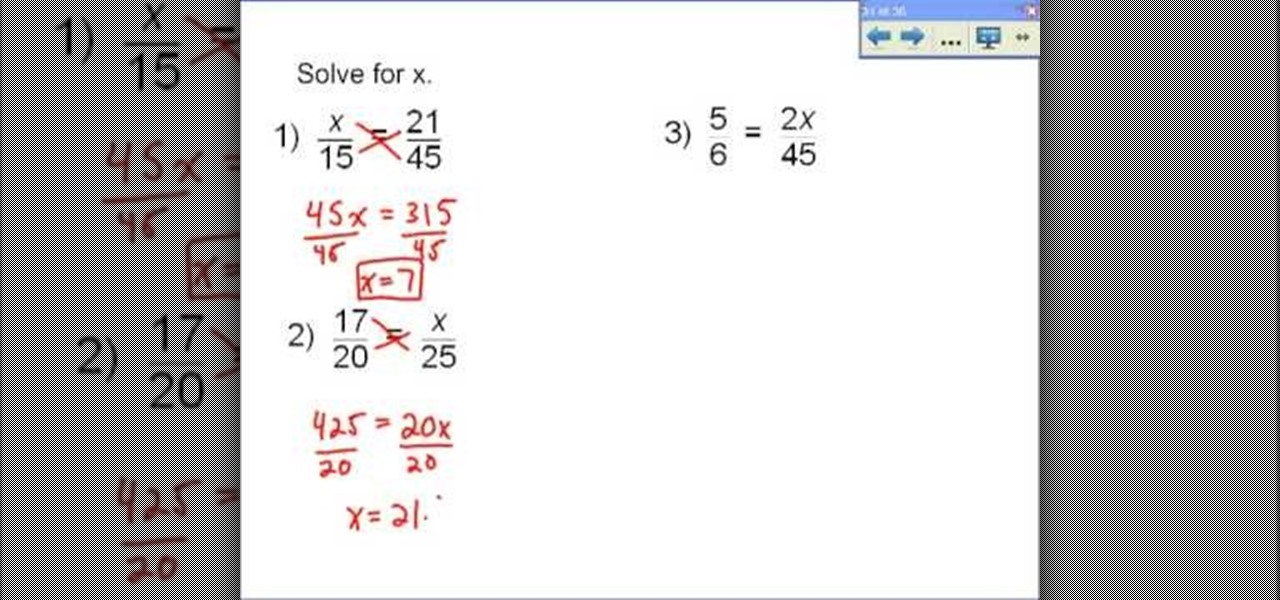
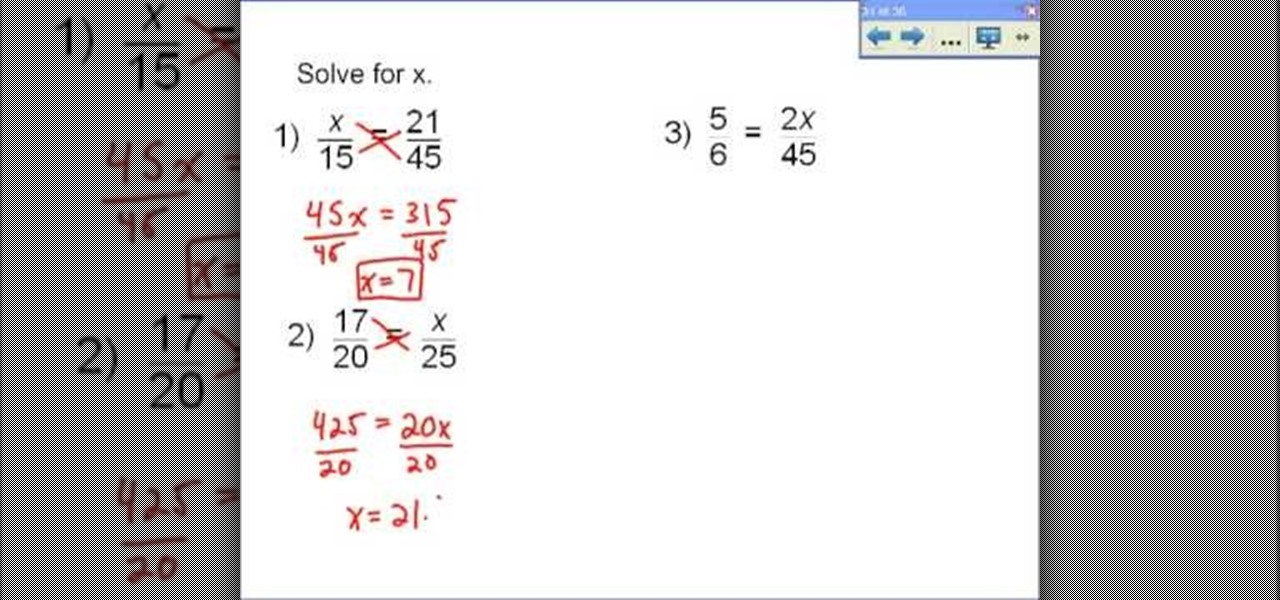
To solve a proportion for a variable you should employ cross multiplication. The basis of cross multiplication is the property which states that the product of the numerator of one fraction and the denominator of what it is set equal to is equal to the product of the remaining denominator and numerator. For example if you have x/15=21/45 you simply need to multiply x by 45 and 15 by 21 then set them equal to each other. The result of this is 45x=315. To solve this new problem for x, divide bo...

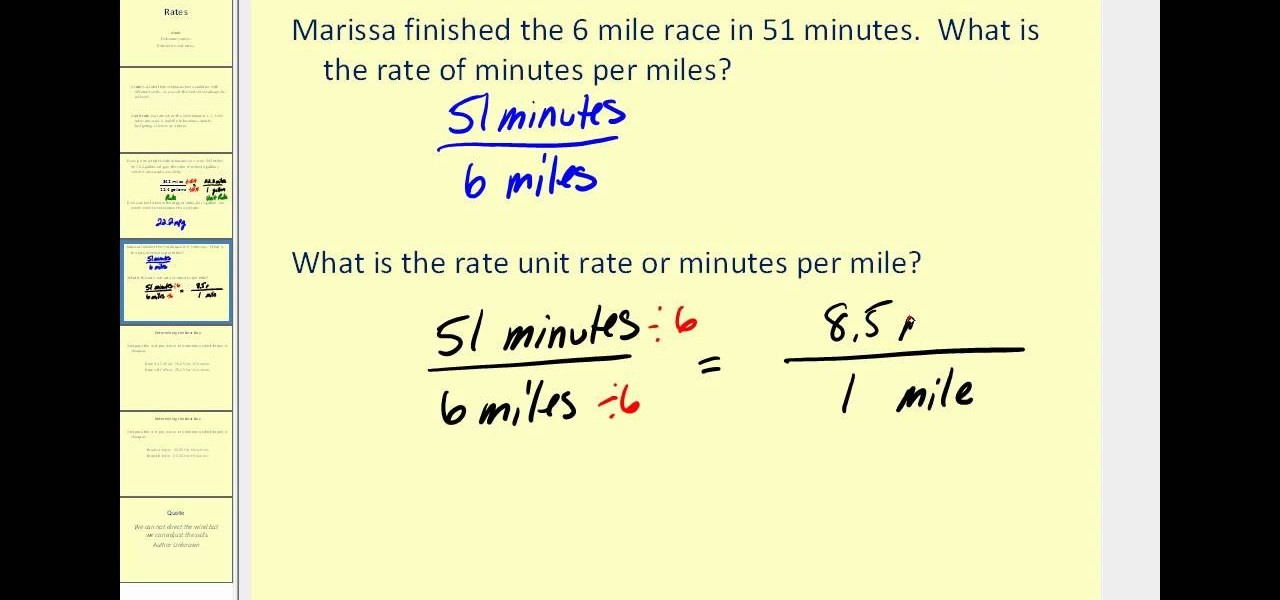
This video shows the method to solve word problems using proportions. In the given problem, we have to find the time taken by a person to type 390 words if the person takes 1 minute to type 30 words. This can be solved using proportions. We take two fractions which are equal. We type '30 words' in the numerator of the first fraction and 1 minute in its denominator. This fraction must be proportional to the second fraction. The second fraction has '390 words' in the numerator and the variable ...

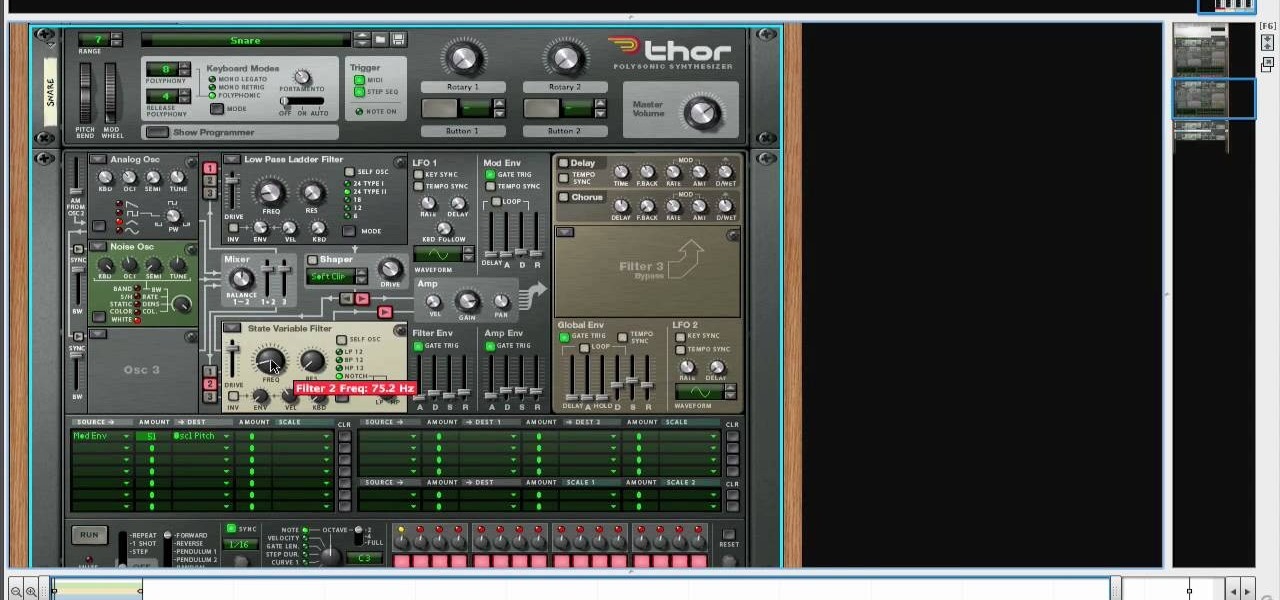
Create drums sounds using Reason's Thor synthesizerYou can use the Thor synthesizer to make a kick, snare, hat and clap sound.Kick:Use the analog oscillator with triple wave form octave3. Set the source to mod envelope 45 destination oscillator 1.Use a very short attack to K and release time. You get the short effect of pitch. Try different oscillator types to get different textures.Snare: Use the same basic patch that we created for the kick. We will keep it as the basis for most patches for...

Developers creating login systems know better than to store passwords in plain text, usually storing hashes of a password to prevent storing the credentials in a way a hacker could steal. Due to the way hashes work, not all are created equal. Some are more vulnerable than others, and a little Python could be used to brute-force any weak hashes to get the passwords they were created from.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

Welcome, in this tutorial we shall we looking at creating a safe(r) way to back up your important files. The contents we will be covering are as follows;

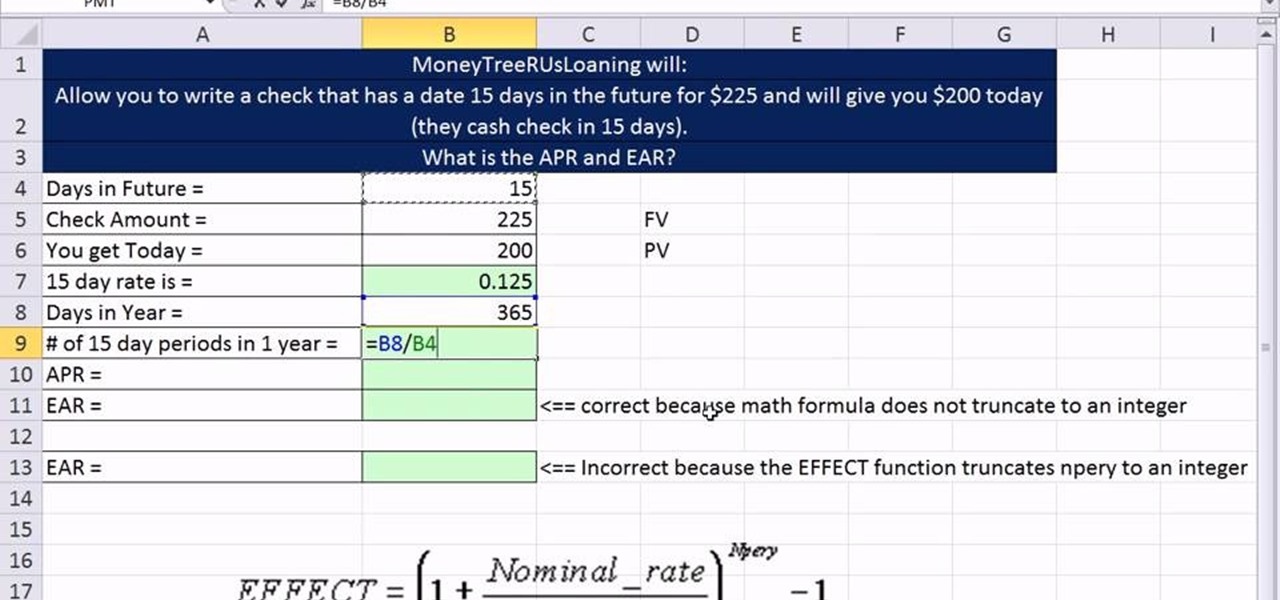
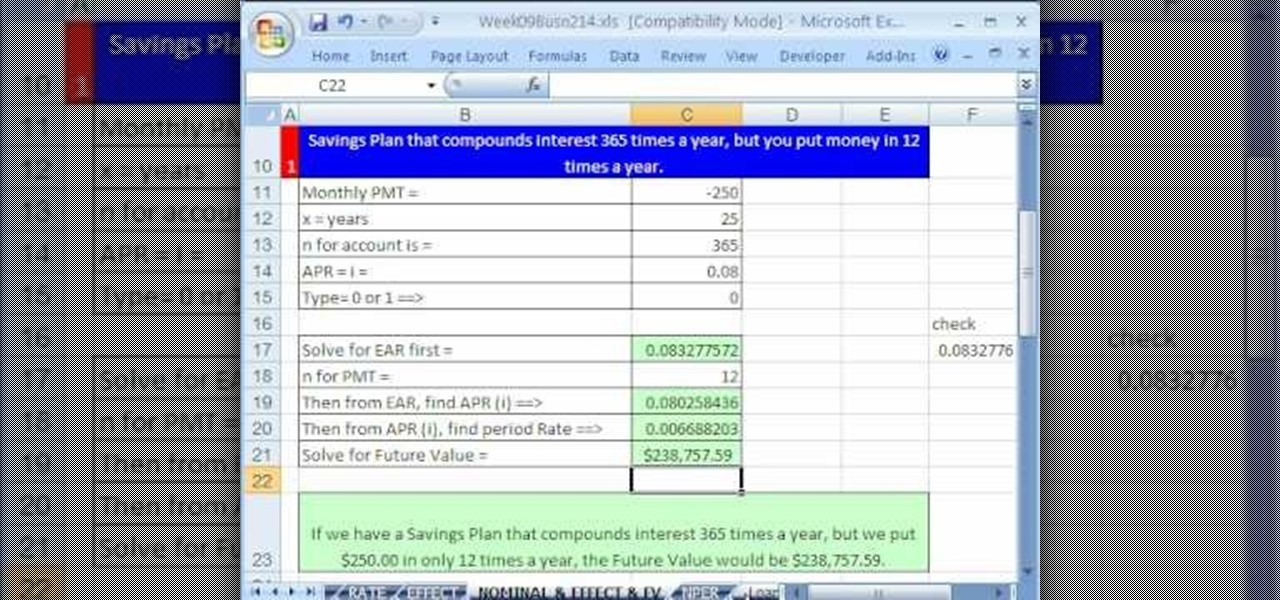
As you might guess, one of the domains in which Microsoft Excel really excels is finance math. Brush up on the stuff for your next or current job with this how-to. In this tutorial from everyone's favorite digital spreadsheet guru, YouTube's ExcelIsFun, part of his "Excel Finance Class" series of free video lessons, you'll learn how to calculate APR (Annual Percentage Rate), EAR (Effective Annual Rate) and Period Rate.

One formula that you will run into in Calculus is calculating the percentage growth rate using a logarithmic derivative, elasticity of demand, relation among elasticity of demand and also revenue. In this video you will learn the different formulas that are used, methods of solving each formula, and also the full solutions.

In this tutorial you are shown exactly how to do algebraic long division when terms are missing in the polynomial. Follow these steps and you can divide whatever you'd like:

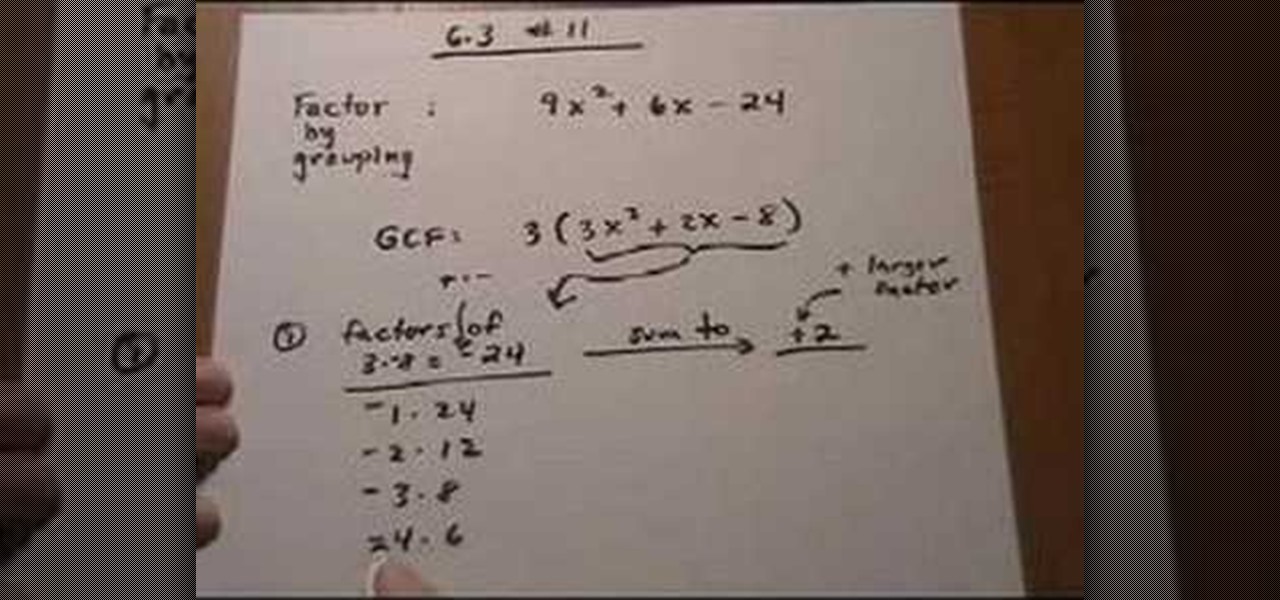
This lesson describes the method to find the factors of a trinomial, which consists of three terms, by grouping. First of all, factor out the greatest common factor (GCF), and write the reduced trinomial in parentheses. Let the terms of the trinomial be written in order of exponent of the variable. For example, 3(3X2+2X-8) trinomial is written in the order of variable, with 3(GCF) factored out. Now identify the coefficient of the first and last terms, for example in this case, it is 3 and 8. ...

This video will show you how to drill a clean hole in ceramic, porcelain, clay, glass or tile. Materials needed for this project are: carbide tile bit, normal variable speed drill (not a hammer drill), air tool oil, plumbers putty, MDF board or a scrap piece of wood.

After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vulnerability.

Hey there, reader! In this tutorial we are going to explain how values are stored in variables as either signed or unsigned. Try to not get lost!

In this article, I'll be continuing my series on microcontrollers. If you haven't read part one, I'd recommend heading over there and reading it!

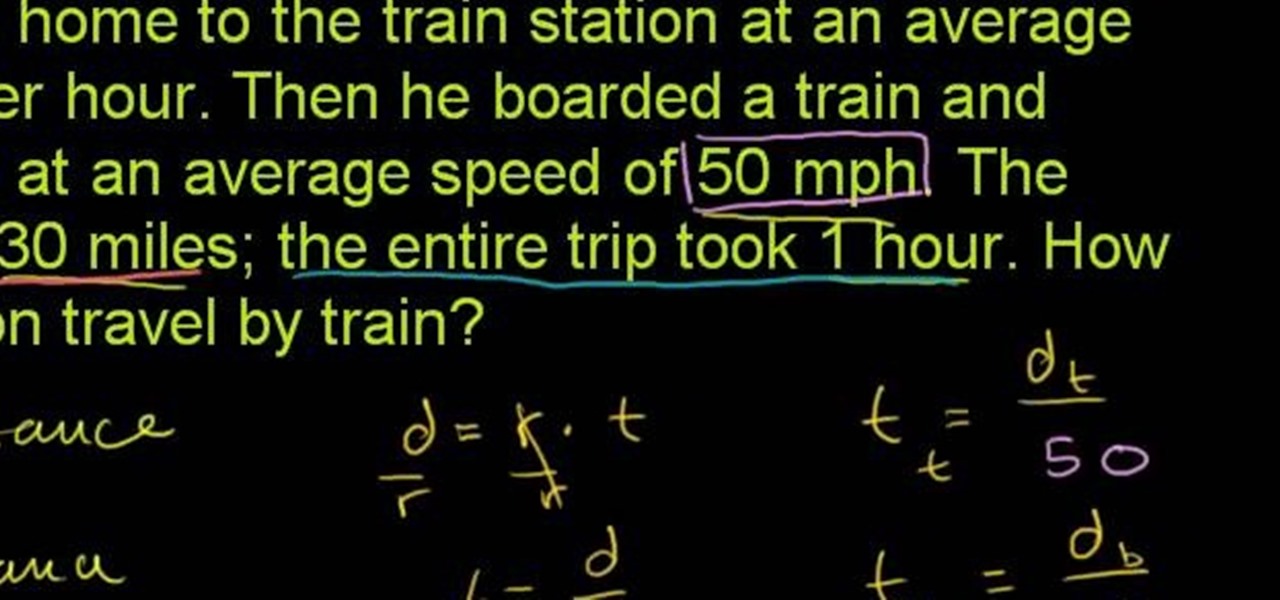
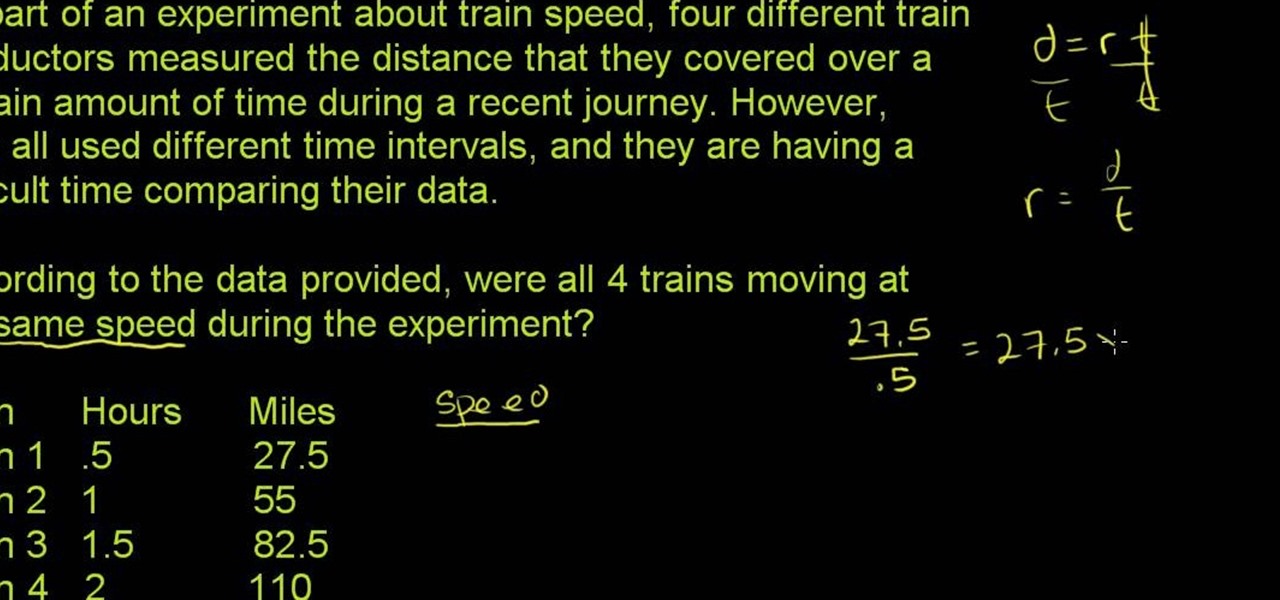
From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever to follow in their footsteps (or just finish your homework or study for that next big test). With this installment from Internet pedagogical superstar Salman Khan's series of free math tutorials, you'll learn how to work with and solve rate problems in algebra using the distance formula.

Need some help figuring out a simple rate problem (involving the rate of a train for example? See how it's done with this free video math lesson. Need help finding the From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever to follow in their footsteps (or just finish your homework or study for that next big test). With this installment from Internet peda...

Want to calculate percentage growth rates (also known as the relative rates of change)? Learn how with this free video calculus lesson, which covers calculating the percentage growth rate using a logarithmic derivative, elasticity of demand and the relation between elasticity of demand and revenue. From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever t...

A lot of time can be wasted performing trivial tasks over and over again, and it's especially true when it comes to hacking and penetration testing. Trying different shells to own a target, and testing out privilege escalation commands afterward, can eat up a lot of time. Fortunately, there is a tool called One-Lin3r that can quickly generate shells, privesc commands, and more.

When we are building programs that communicate over a network, how can we keep our data private? The last thing we want is some other lousy hacker sniffing our packets, so how do we stop them? The easy answer: encryption. However, this is a very wide-ranging answer. Today we're going to look specifically at how to encrypt data in Python with dynamically generated encryption keys using what is known as the Diffie-Hellman key exchange.

Welcome to a tutorial explaining functions. This article will help clarify some things we have already been exposed to such as function prototypes, function calls, return values, etc.

In this tutorial I will be explaining the purpose of unique encryption/decryption scripts ( I will be referring to these at "UEDS" for this tutorial). Then, I will show you how to make one. Finally I will talk about the downsides to the method I use. I will also provide links explaining the concepts and algorithms used in encryption to anyone who wants to see what is going on under the hood.

Welcome back, my fledgling hackers! Scripting skills are essential is ascending to the upper echelons of the hacker clique. Without scripting skills, you are dependent upon others to develop your tools. When others develop your tools, you will always be behind the curve in the battle against security admins.

Welcome back, my hacker apprentices! To enter the upper echelons of hackerdom, you MUST develop scripting skills. It's all great and well to use other hacker's tools, but to get and maintain the upper hand, you must develop your own unique tools, and you can only do that by developing your scripting skills.

What Is a Rate? A rate is a comparison of two quantities that have different units. An example is 90 miles/3 hours, which is read as 90 miles per 3 hours.

Whether you're interested in learning Microsoft Excel from the bottom up or just looking to pick up a few tips and tricks, you've come to the right place. In this tutorial from everyone's favorite digital spreadsheet guru, ExcelIsFun, the 48th installment in his "Highline Excel Class" series of free video Excel lessons, you'll learn how to use the RATE, EFFECT, NOMINAL and NPER Excel functions to solve the following problems:

As you might guess, one of the domains in which Microsoft Excel really excels is business math. Brush up on the stuff for your next or current job with this how-to. In this tutorial from everyone's favorite digital spreadsheet guru, YouTube's ExcelIsFun, the 29th installment in his "Excel Business Math" series of free video lessons, you'll learn how to solve for rate, amount of change and rate of change.

Want to learn how to do quick scoping in BO? It's easy: use the variable scope and zoom in to the second or third level of magnification. Voilà. No more two-second delay when shooting. For a complete walkthrough of how to quick scope, watch this gamer's guide.

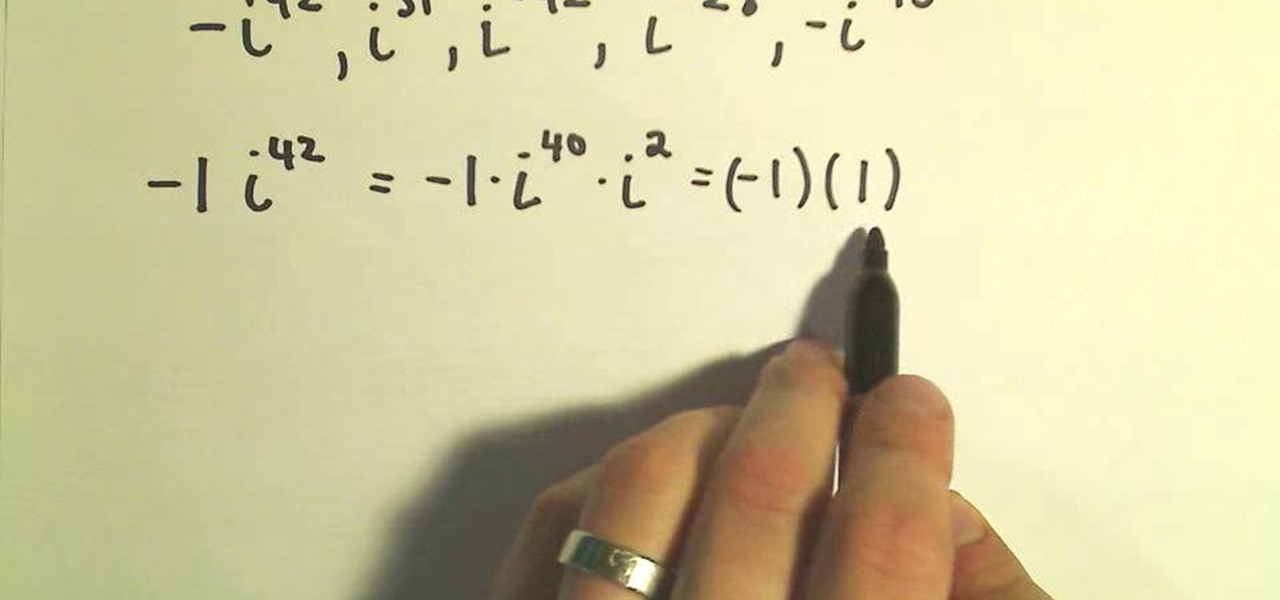
The powers of the complex number "i" run their course in a cyclical nature, like annual seasons of "American Idol." Simplify your life - or at least your math class life - by learning how to rewrite the powers of "i" into simple, single variable expressions.

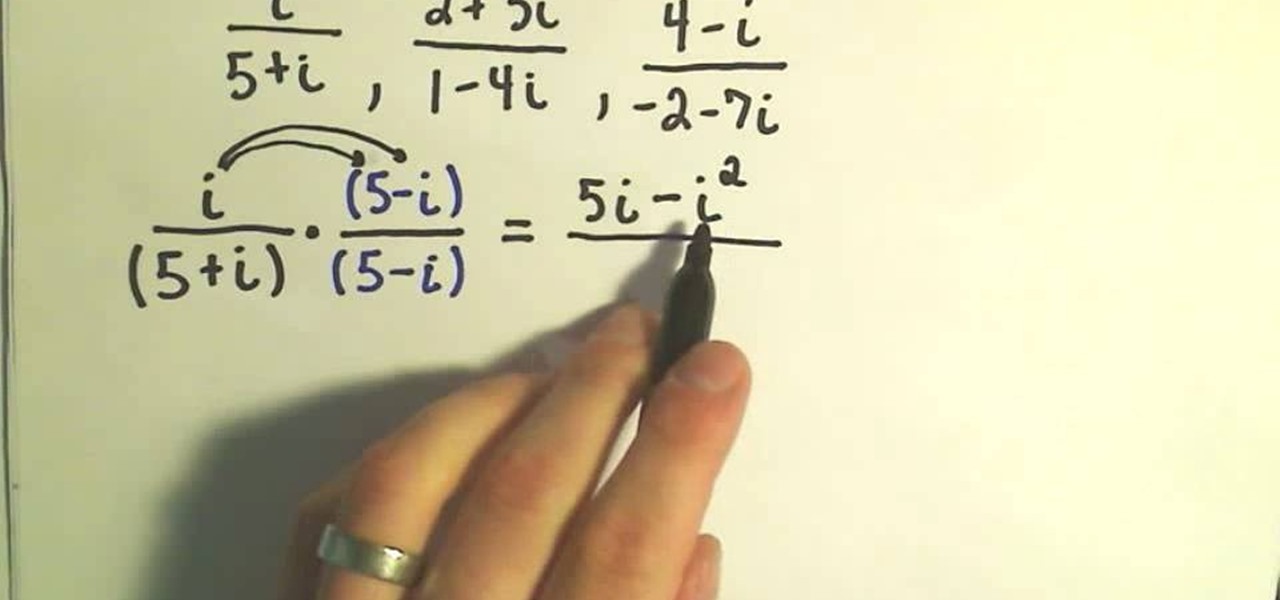
This series on complex numbers will help you solve equations with the cute variable "i" with ease by multiplying by the conjugate.

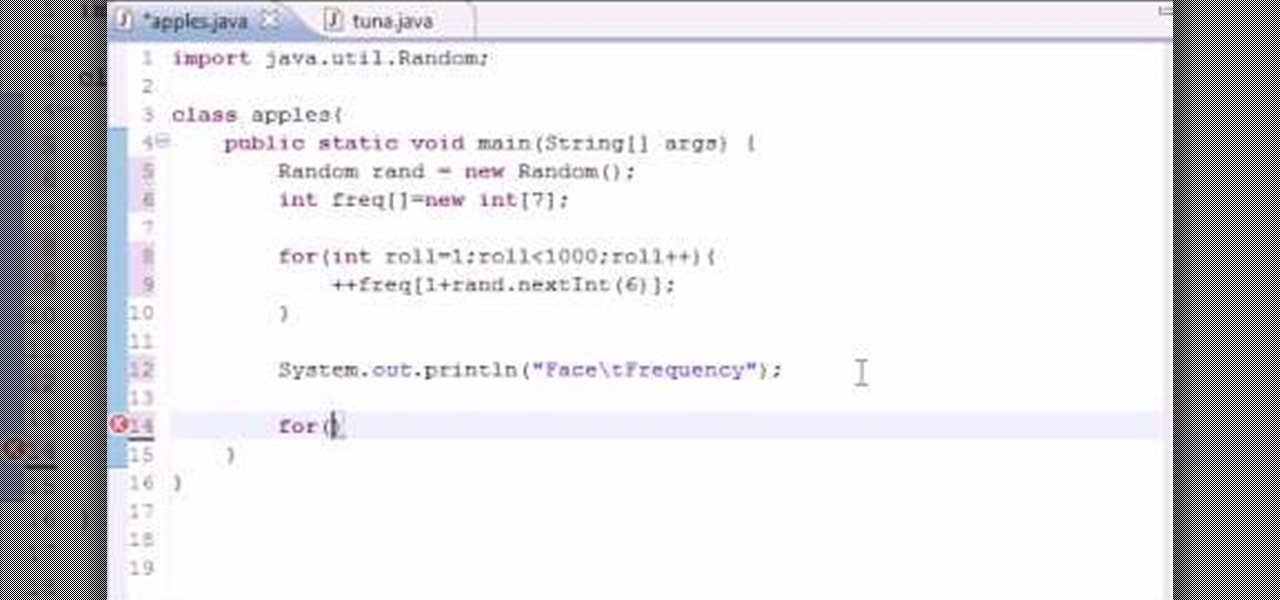
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBostonian will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to store variables in an array index when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

The Wedge ROP is a render output driver, which can be used to change variables on the fly while rendering. This can be very useful when simulating, in that you can test out different parameters to see the different results. It's a relatively new feature in Houdini 9.5.

I'm back! We're learning Java WhileLoops today.

OK, In my last Tutorial we made a Server for sending Instructions to a Client. This time we will build the Client. Fire up your favourite Python environment and get the Code here.

Ruby is a dynamic, general-purpose programming language created by Yukihiro "Matz" Matsumoto in Japan around the mid-90's. It has many uses but with it's flexibility, it makes a great language to write exploits in. In fact, the entire Metasploit Framework is written in Ruby! The sole purpose of this series is to teach hackers the basics of Ruby, along with some more advanced concepts that are important in hacking.

Welcome back, friends! Many times, businesses, friends, and family will lock their zip files with a password to keep their files secure. It is reasonable, and understandable. Well, thanks to hackers, there are many ways to get past this wall of security.