
News: Magic Leap & Weta Workshop Release Dr. Grordbort's Invaders for Magic Leap One
As promised last week, Magic Leap has finally released the long-awaited augmented reality game Dr. Grordbort's Invaders.


As promised last week, Magic Leap has finally released the long-awaited augmented reality game Dr. Grordbort's Invaders.

Another massive piece of the mysterious augmented reality puzzle known as Magic Leap fell into place on Wednesday as AT&T announced that it will be the exclusive launch carrier for the device.
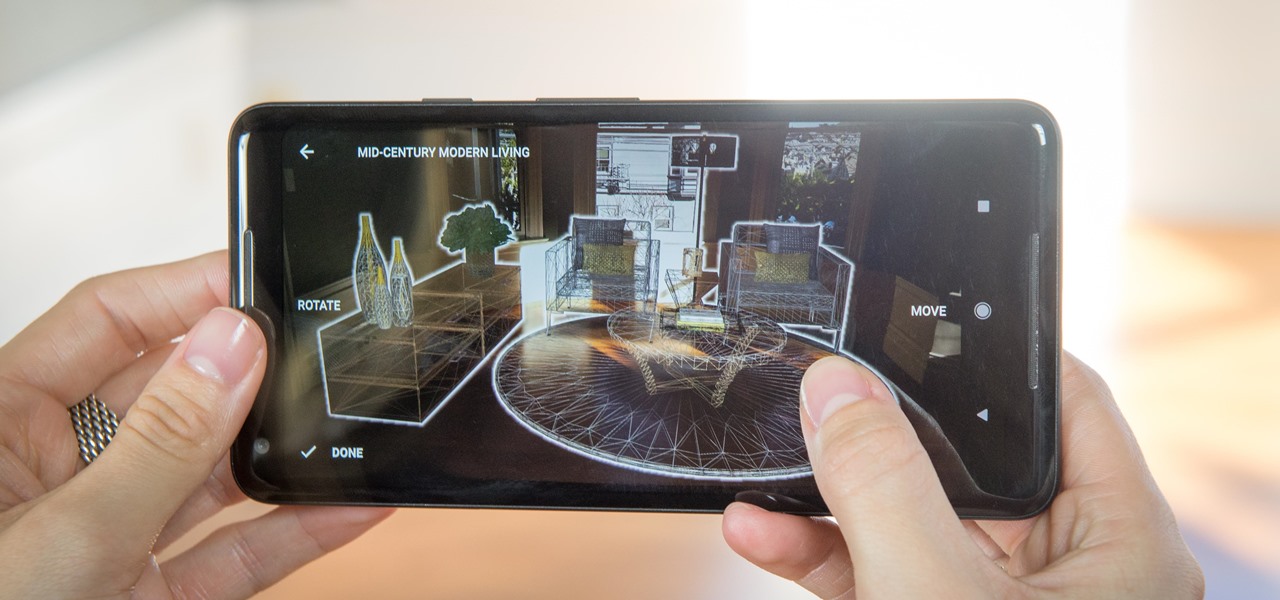
Just weeks after officially launching its mobile augmented reality toolkit, Google can now claim one of its first Android and ARCore app exclusives with the Curate app from Sotheby's International Realty.

The NCAA College Basketball Tournament, colloquially known as March Madness, is arguably the most exciting postseason format in US sports, and the team behind Thyng want to take advantage of the annual event with AR content.

Sure, you just got your Galaxy S8. But now, Samsung came out with their latest and greatest device — the Galaxy S9. While the S8 is still a great device, it's possible that the Galaxy S9 completely outclasses it, almost forcing you to pick it up. It is worth it though? That's a harder question to answer than you may think.

Unsurprisingly, Google wants to be the caretaker for augmented reality on the web, and its latest move in this endeavor is a 3D model viewer prototype called Article that's designed to work across all web browsers.

Just as the Transformers animated TV series of the '80s were basically half-hour commercials for toys, a new Transformers AR app for iOS similarly functions as a promotion for the latest installment in the film franchise.

Google just unveiled it's biggest search product in recent memory, except this time the search giant is looking to take over the world of virtual objects.

It's fitting that students at the University of Washington can catch a glimpse of the new, 135,000 square-foot computer science building in augmented reality before construction is completed.

The National Transportation Safety Board (NTSB) said it is still investigating the circumstances of a fatal Tesla crash last year to determine if the car or Tesla's Autopilot driverless system was at fault, but revealed more details about the circumstances of the crash.

CyanogenMod, the popular custom ROM available for many Android devices, has a nice little feature that displays a music visualizer beneath your on-screen navigation keys while you're listening to your favorite songs. It's a subtle touch, but it makes for a more immersive experience when you're jamming out while using your phone or tablet.
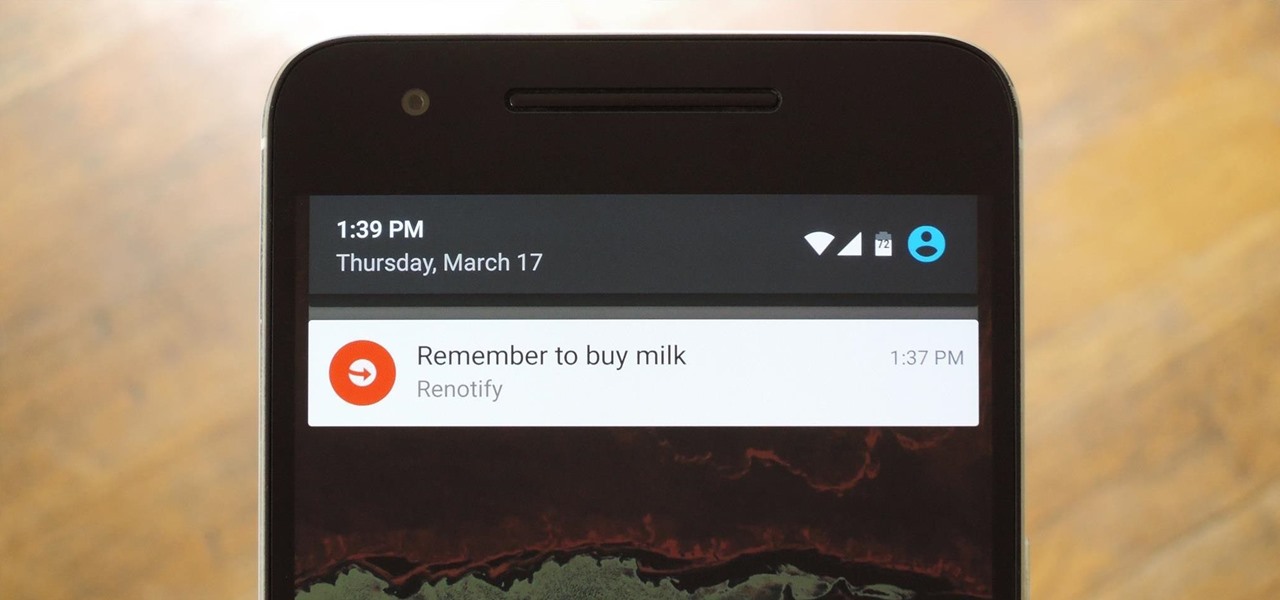
There are plenty of Android apps for creating reminders, to-do lists, and taking notes—but the vast majority of these are all-in-one apps that may actually have too many features. When a thought randomly crosses your mind and you'd like to remember it for later, the most important thing is to be able to jot it down quick, fast, and in a hurry.
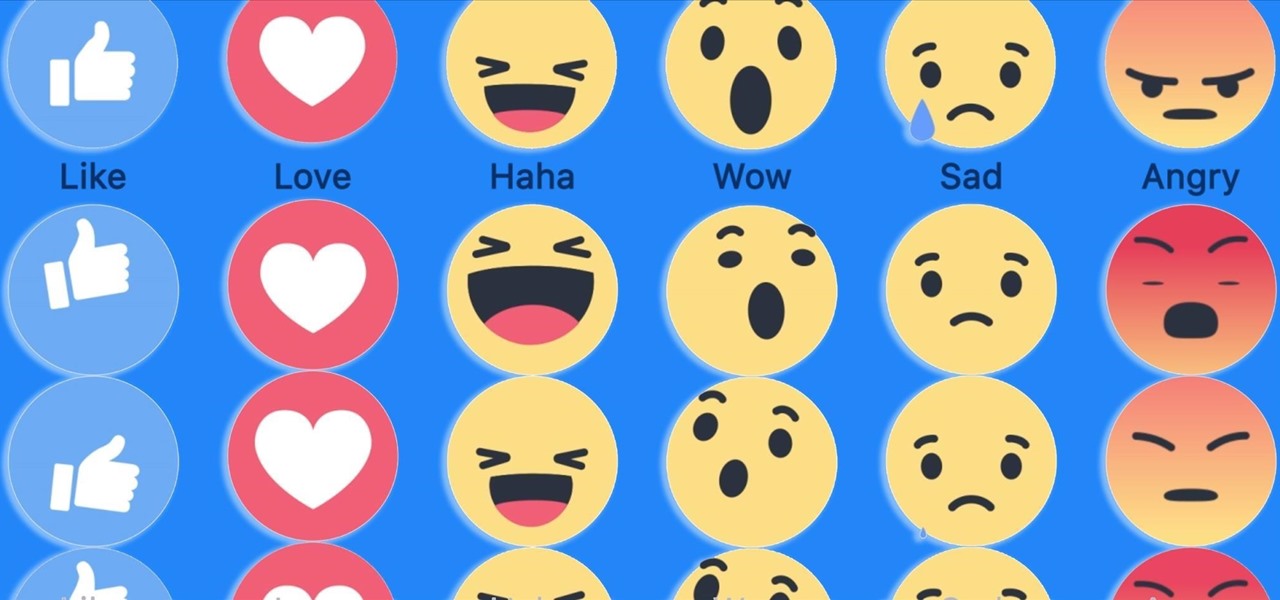
Have you ever run across a Facebook post that you don't necessarily want to "Like," but you're not really passionate enough about to bother stringing together a couple words for a comment? Well, you're in luck, as Facebook added five new "Reactions" that let you do more than just like a post, and they're now live for everyone.

The dock in Mac OS X is intuitive, customizable, and aesthetically pleasing, which is a stark difference from its clunky Windows alternative. In fact, in Windows, it takes both the Start menu and taskbar to accomplish what Apple's dock does—but it doesn't have to be like that. Below, I'll show you how to add an OS X-inspired dock on any PC running Windows XP or higher. Step 1: Install Aqua Dock

The 2015 LA Auto Show showcases the best of the auto industry—well, at least according to car companies. Increases in horsepower, better fuel economy, and most importantly—the latest tech—is all on display during the 10-day event in Southern California. Once of my first missions at the show was to figure out who is putting the most care and thought into in-cabin electronics, mainly the ones that guide us around and play our music, affectionately known as "infotainment."
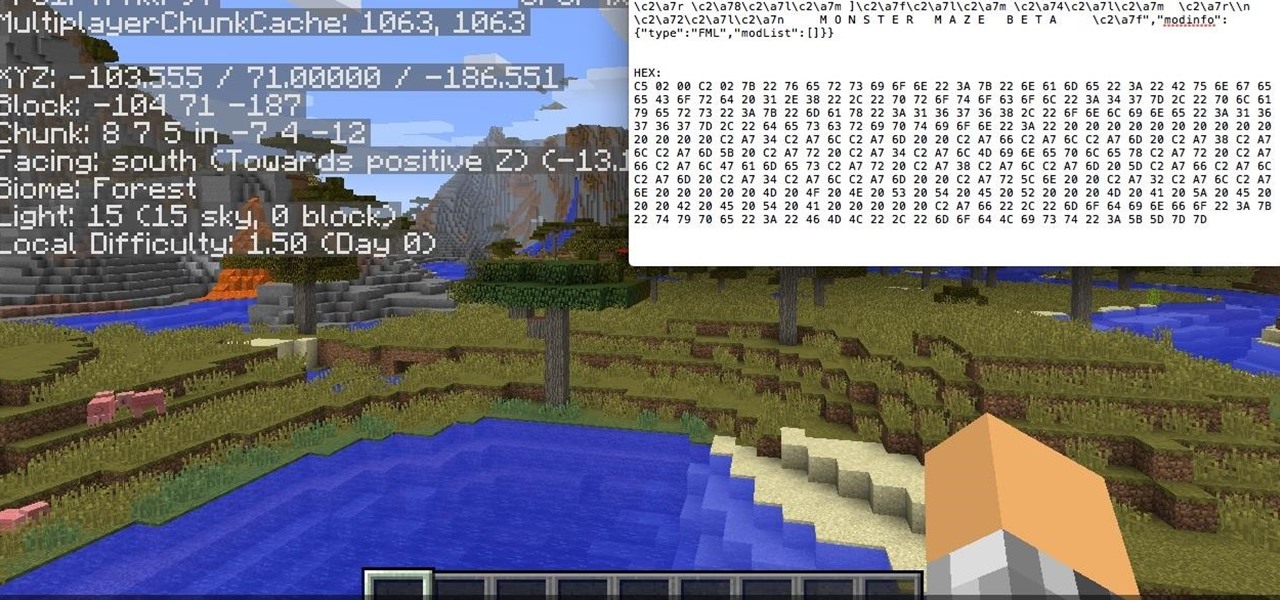
Hello, fellow hackers. I'm sure we've all seen it somewhere: the undying question of "How do I hack the game so-and-so?" And the answer usually is, "Come back when you actually know how to hack!" But how does one even go about "hacking" a game? What could that even mean?
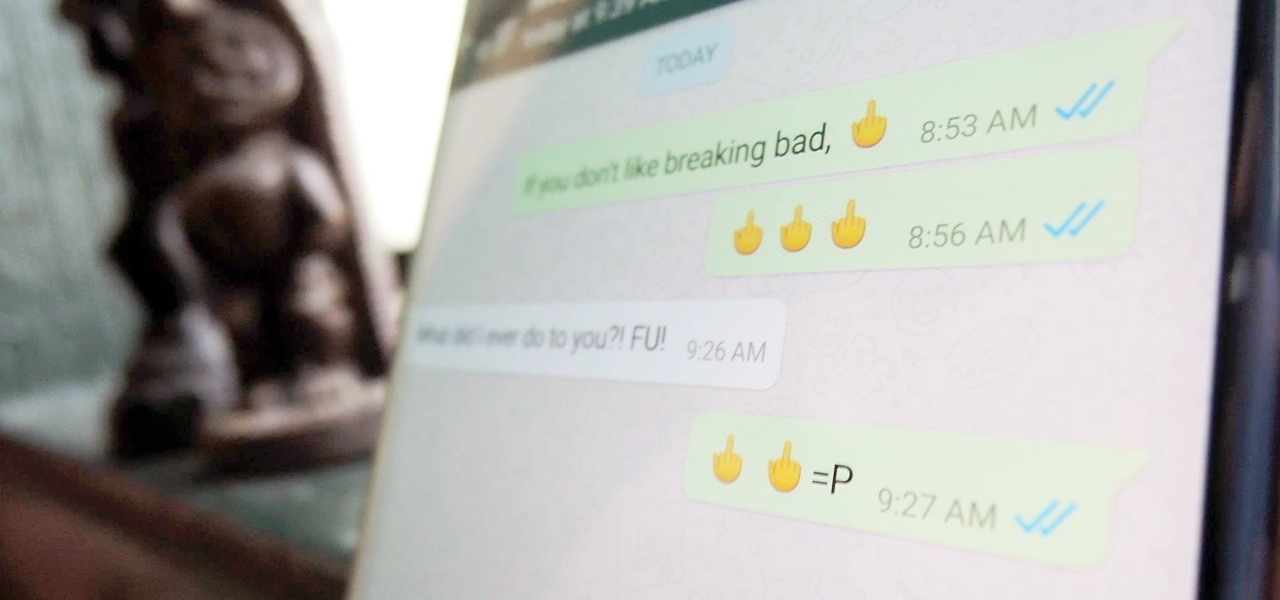
Hidden deep in WhatsApp's emoji database is a middle finger emoji, and there's a really easy way to use it. Much like Spock's "live long and proper" Vulcan salute, this one can be used simply by copying and pasting the emoji from our tweet. Note that the emoji, for now, does not display properly on iOS devices, but it can still be sent. So if you're in a conversation with an Android or computer user, they'll see it just fine.
For all of the flak that it catches, Wikipedia is still a great source of information. Contributors take their work very seriously, so the vast majority of information is cited, and the site serves very well as a starting point to learn about a new topic.
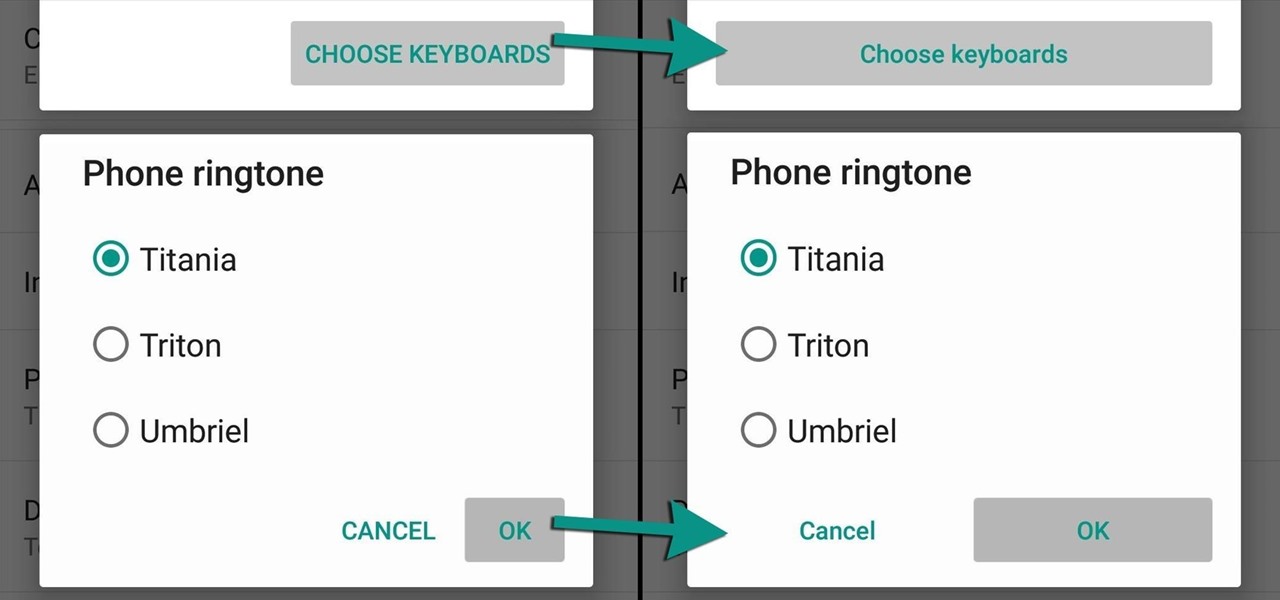
Lollipop brought a complete visual overhaul to Android, and while the vast majority of changes have been met with praise, some UI tweaks missed their mark.

These last few months have been a Lollipop lovefest, and I'm not talking about the candy. Android's latest OS has been exalted for its embrace of Material Design, and we've certainly given Lollipop its fair share of coverage as well; check out all its new features and ways to make older devices get some of the new look and feel of Android 5.0.

There's been a lot of discussion lately about the practical uses of Google Glass. Sure, you can use them for translating text instantly or further engraining yourself in social media, but how about saving someone's life? That's precisely what Dr. Steven Horng of Beth Israel Deaconess Medical Center has says happened with a recent patient of his. After launching a Google Glass pilot program late last year, the device was seen as a critical factor in saving the life of a patient in January.

The old "my battery is dead" excuse for not calling your mother may soon be a thing of the past. A team from the Korea Advanced Institute of Science and Technology (KAIST), led by Professor Jo Byeong-jin, has developed a "wearable thermo-element" that can be built into clothing to power your electronic devices. The science behind the innovation converts body heat (thermal energy) into usable electric energy. Made with lightweight glass fiber, this small thermo-element strip can produce about ...
When we take pictures with our smartphones, it’s safe to assume we’re taking more than one. We're either trying to capture the right light, look, or expression… or maybe a slight nod to the right to show off your good side.

One of the main reasons why the Samsung Galaxy S III has dethroned Apple's iPhone 4S as the best-selling smartphone in the world is due to Android's open-source operating system. The vast spectrum of customization that comes with Android has become one of its focal points, allowing n00bs and programmers alike to build and destroy. The open-source OS has allowed rooting and modified ROMs to flourish within Android community. The only problem with this is that rooting and installing your own RO...

Directory traversal, or path traversal, is an HTTP attack which allows attackers to access restricted directories by using the ../ characters to backtrack into files or directories outside the root folder. If a web app is vulnerable to this, an attacker can potentially access restricted files that contain info about all registered users on the system, their permissions, and encrypted passwords.

Okay, so this doesn't exactly teach you how to audit as a Scientologist... but I think it is the closest to an explanation we are going to get. So, listen up & try to learn.

Amazon Web Services (AWS) is the premier on-demand cloud computing platform. Offering a wide range of APIs to companies, governments, and individuals on a pay-as-you-go basis, this Amazon subsidiary pulled in over $35 billion in revenue in 2019 alone.
It wasn't too long ago that the power menu for stock Android didn't offer much beyond turning the device off, but Google has steadily added more functions, like capturing screenshots and provisioning access to emergency information.

While some widely praised immersive computing initiatives at Google are shutting down, over at Epic Games things are just ramping up, and it involves quite a bit of cash available to indie augmented reality developers and startups alike.

Move over, cosmetics companies. The athletic footwear industry wants to be able to give their customers the opportunity to try on products in augmented reality as well.

In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.
The arrival of Magic Leap One is tantalizingly close and, although the company has been saving the last details for launch day, a few of the more important details were found this week hiding deep in the code on Magic Leap's website.

On Wednesday, the tech world woke up to fairly shocking news with the announcement that AT&T would be the exclusive wireless carrier for the forthcoming Magic Leap One, as well as an investor in Magic Leap.
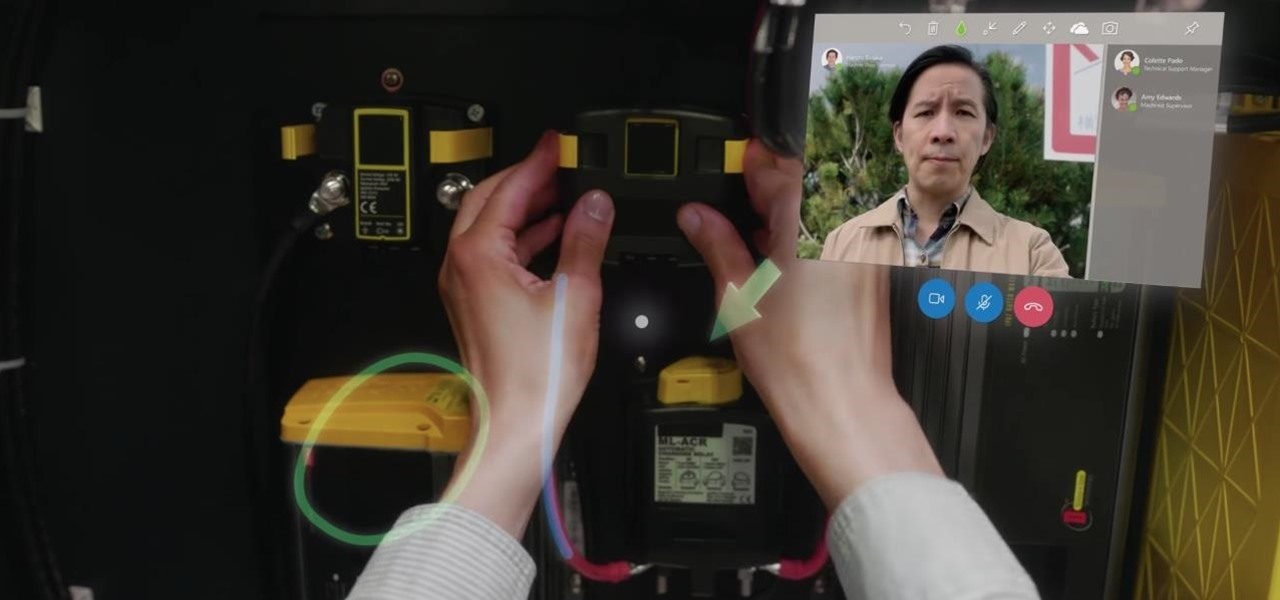
On Monday, at its annual Build developer conference, Microsoft revealed two new apps for the HoloLens apps.

Not content to just be a provider of rugged smartglasses for enterprise users, DAQRI has made the jump into the AR software side of the industry with its new Worksense productivity suite.

How would you feel if the stethoscope used by your doctor to listen to your heart and lungs was teeming with potentially unfriendly bacteria?

The automotive industry is traditionally very conservative, so when a carmaker says it will launch a particular model or feature by a certain date, it means a lot.

A pair of organizations recognized companies working in augmented reality for their innovative technologies over the past week. Meanwhile, another company used augmented reality for a sector that is overdue for a technology makeover, while another company has developed new camera modules that could usher in the next evolution of mobile AR.

Microsoft Build 2017, the first of Microsoft's big developer conferences for the year, is just a few weeks away. This very popular conference, which has been going on since 2011, is known to sell out fast. In 2015, it sold out in under an hour, and in 2016, in less than 5 minutes. This year was no different, according to VentureBeat; While not quite as fast as last year with so many rumors of HoloLens on the horizon at the time, this year's Build was sold out in 8 hours. And for this year's B...

Rooting a phone lets us install custom operating systems, known as ROMs, which replace the device's preinstalled OS. Most custom ROMs are based on code from the Android Open Source Project (AOSP), which gives them a look and feel similar to Google's version of stock Android. But every now and then, you'll see a ROM that isn't based on Android, though these are few and far between — at least, until now.