
How To: Exchange Gift Cards for Facebook Credits
Plastic Jungle.com offers an awesome service in which you can sell your unused gift cards for cash, other gift cards, and even Facebook credits!


Plastic Jungle.com offers an awesome service in which you can sell your unused gift cards for cash, other gift cards, and even Facebook credits!

Have you ever gone on a long internet binge, researching and surfing mindless things, and thought to yourself: I wish I could make some money surfing the internet and sharing the (sometimes useless) information I had just acquired? Well, now you can!

Over the weekend, Google made several updates to the Google+ profile. Here's how to make the most out of old and new features to make your profile page shine.

In this video tutorial, viewers learn how to set and encrypt their Wi-Fi password using WPA in Apple Airport. Begin by opening the Airport Admin Utility application from the CD. Then locate your the name of your network and double-click it or press the Configure button at the bottom right of the screen. Now enter your password and click OK. The network should be opened now. Then click on the Airport tab and click on Wireless Security. In the pull-down menu, select WPA2 Personal. Then click on...

Did you know that you can use Gmail to make free phone calls to anywhere in North America? We're not talking computer to computer, but actual free phone calls to cell phones and home phones. All you need is a Gmail account, a microphone, and speakers plugged into your computer.
This tutorial will walk you through the steps required to install the Ubuntu 9.10 operating system (Karmic Koala) on your computer. I have a Suzuki Kuiper 1411 HKS notebook computer with 2.1 GHz Intel Dual Core processor, 4GB RAM and 320GB hard drive. It has a dedicated 256MB Nvdia GeForce 9300M GS graphics card and 1270++MB of VRAM in SLI mode.

Ever since kernel 2.6.xx in Linux, a lot of the internet kernel modules for wireless interfaces ended up becoming broken when trying to use monitor mode. What happens commonly (to myself included) is a forced channel that your card sits on. No good! For users of airodump and the aircrack-ng software suite, the software has become unusable.

Nintendo has already confirmed that the successor to the Wii will be on the market in 2012, but a lot is still unknown about Project Café, the codename given to the device. From all of the leaked information on the web, it seems like there's a significant design upgrade from the Wii, making it hard to imagine this gaming console being called or even referred to as the Wii 2.
Ever wonder what your brain looks like on video games? Below, Matt Richtel of the New York Times lies in a $3 million M.R.I. scanning tube while playing a simple driving game, as researchers sit by and observe the real-time images inside Richtel's brain.

About a decade ago, Deus Ex came out to rave reviews. Except this guy Tom Chick hated it. And said so, in a pretty blunt manner.

My father recently suffered a stroke. Now in Neuro Rehab at Cedars Sinai, he is enduring daily physical therapy, recreational therapy and occupational therapy sessions to help improve his balance, mobility and fine motor skills. I was initially worried about how I could incorporate his current PT regime in his daily life after he's discharged. That was until I saw the devices he used in the PT gym. Despite their "medical device" designations, the high tech stuff is remarkably similar to what ...

The medical field has known for some time now that negative pressure (re: suction) can drastically speed up wound recovery time. However, the machines that are currently available are quite expensive, and not an option for third world countries. Enter MIT student Danielle Zurovcik. The doctoral student has created a hand-powered suction-healing system that could completely revolutionize first aid in developing nations. Her device goes for only 3 bucks a pop.

When your bootloader is unlocked, your phone shows a screen that tells you the bootloader is indeed unlocked and how software integrity can't be verified. But if you're the one who unlocked the bootloader in the first place, all this message does is slow down the bootup process dramatically.

As you all know, the first Null Byte Technical Excellence Tutorial Contest ends this coming Monday, Feb. 15, 2016. If you are working on another great article or your first article, try to complete it and submit it before midnight Pacific Standard Time (PST) to be considered in this contest. The winner of this contest will not only receive a certificate verifying the technical excellence of their tutorial, but they will also receive a free copy of the Professional version of the Exploit Pack ...

In a move that seemingly surprised everyone—including Samsung—Korean carriers have released the Galaxy S5 a full two weeks early to avoid being caught up in an about-to-be-imposed ban.

Been hacked once? Twice? Maybe more? You thought abc123 was the only password that is both 6 characters wide and easy to remember? I have some suggestions in store for you. Just read on...
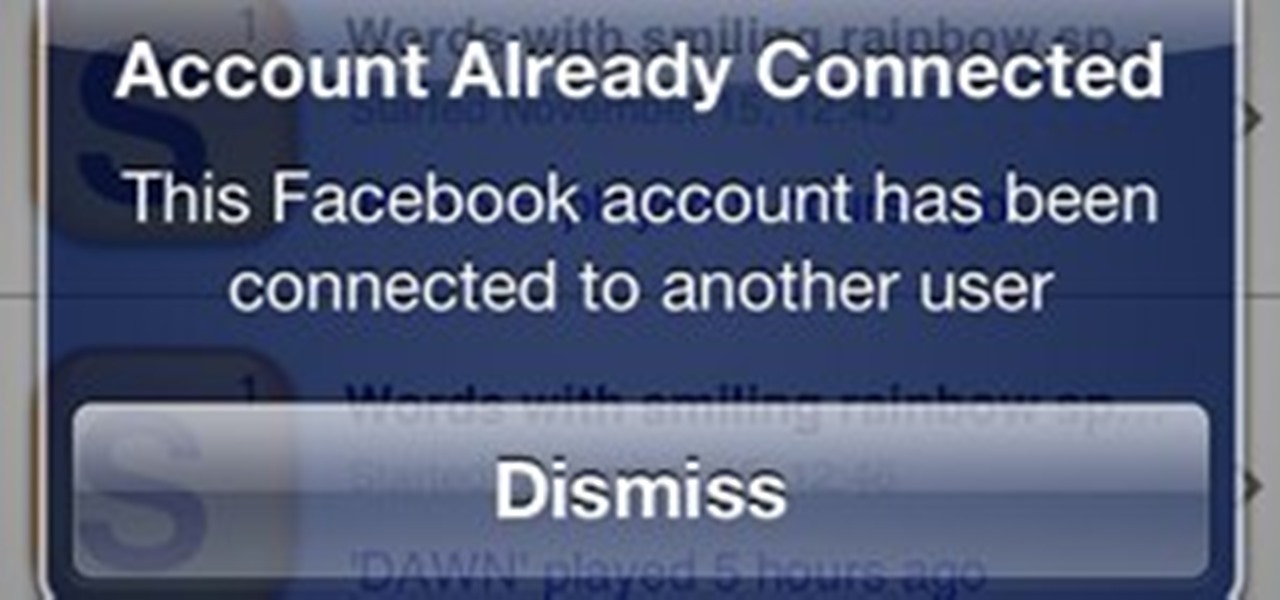
I can't say it's absolutely true, but when it comes to mobile word gaming, there's Scrabble people and then there's Words with Friends people. It feels segregational. Rarely does one play both. At least, that's what I see when it comes to my family and friends.

Call Your State's Nurse Aide Registries for School Inquiries

It's a question I've been pondering a lot lately. Technically, children under the age of 13 are not allowed to join Facebook. But according to a Consumer Reports in May, 7.5 million children 12 and younger are already on the site. Currently, federal law prohibits websites from collecting personal data from children without parental permission. The Children's Online Privacy Protection Act, or COPPA, as it is more commonly known, has been in effect since 1998, but has not been updated since.

Join the Pilot program and learn how to fly! But you're not going to be flying airplanes in this Pilot program, you'll be trying your hands at Google's first laptop computer.

Nothing on the web is ever private. If you thought you can control your privacy, you were wrong. Websites may give you security options to better hide your information from the world, but ultimately your privacy resides in the hands of the website itself. We've seen how websites let ad companies track our private usage. We've seen how Facebook mucked up their privacy controls. We even saw how websites like Gawker are prone to hackers stealing user information. And now, Etsy has made what was ...
1.) If you do not know something, keep our mouth shut.* No-one, I repeat no-one, is interested in your uneducated guesses about why something is the way it is, or why someone did something a certain way. At best, you will trick them into temporarily thinking you know what you’re talking about. At worst, you will convince them that you are speaking the truth and they will perpetuate your bullsh*t to others. Do not contribute to making the world a more foolish place just because you had to say ...

Here's a delicious Byte of information for you. A proof of concept program on Linux was coded to exploit a known bug in how the Linux Kernel (versions 2.6.39+) handles permissions for the

Skyrim is a time consuming game. I know I'm not alone in saying I constantly find myself looking for more time in the day. There is never enough time to read the books I want to read, or learn what I want to learn, or play the games that I want to play.

This is the Windows OS counterpart to my tutorial on how to burn the new XDG3 formatted games on Xbox 360. Microsoft invented a new disc format system to trump piracy, it's called XDG3. XDG3's standard is to burn a whole extra gigabyte of data to the disc, to allow more content, but more importantly for stopping piracy. This extra gigabyte of data makes it impossible to burn or rip a game the traditional way. So how on earth can we burn our fully-legal back-ups that we should rightfully be ab...

Many companies were disappointed when Google+ rolled out and banned the creation of accounts specifically for businesses and brands. Fortunately, today, Google began rolling out Google+ pages, for them to start connecting with customers and followers. For an example of what a Google+ Page looks like, check out the one for the +The Muppets:

There is a near-infinite amount of ways a computer can be broken into. But that does not mean that there isn't a reason to secure our computers as best as we possibly can. It's like the principles of a secure house. Which are the most secure houses? The ones with locks and advanced alarms, obviously, but not for the reasons people normally think.

Children under the age of 13 possess insight that can blow the minds of their elders, but not the wherewithal to make important life choices for themselves. This is exactly why there are strict rules against marketing cigarettes to them. In 2000, a law went into effect called the Children's Online Privacy Protection Act that institutes similar consumer protections for our youth's online identities, prohibiting companies from soliciting personal information from children under 13 years of age ...

Mozilla is scheduled to release their updated Firefox browser on Tuesday, bringing the popular web browser up to version 6. Lately, the Mozilla team has been releasing newer versions of Firefox without a slew of new features, focusing on fixing bugs and getting the improved product out as quickly as possible, in order to compete more rapidly with other browsers like Google Chrome.

Google started culling Google+ accounts. There are two main targets: businesses and those who are using pseudonyms. For businesses, Google is promising to provide their own version of Facebook Pages, which will be released later this year. For those who use pseudonyms, they aren't so lucky. According to Google+'s community standards, users must "use the name your friends, family, or co-workers usually call you". The purpose of this rule is ostensibly to discourage spammers and people from set...

ARGs have taken the concept of video games to some odd and wonderful real-world places. Socks, Inc. might not be the first ARG, and LittleBigPlanet might have defined the sock-puppet-based game archetype, but it is the first game to combine ARG and sock puppet elements into one package.

In Google definitions a macro is defined as "a single computer instruction that results in a series of instructions in machine language". Basically a macro is a programming script that tells the computer what to do. You can tell a computer (via a macro) to move a mouse, click, type or do any task that a computer can do with automation. There are also many (primitive) computer viruses that are coded entirely in a macro script. There are many ways to create a macro script but I will only go ove...
Tomorrow is another day of election (PSG). I have to wake up early to set up the computers on both computer rooms. The election process is computerized, making the counting of votes the responsibility of the computer. What makes this year's election special is that for the first time in 3 years (correct me if I'm wrong), there are competing parties. The result is something to look forward to especially for me who contributed in the creation of the system.

One of the most important marketing tools we should always be developing to help reinforce our brand is our references. Just like many companies use their client list and client references to build credibility and confidence for their products and services, we should also leverage our references to build credibility and confidence in our capabilities and brand. Sometimes reference checks are just a formality, but in most cases potential employers (i.e., potential clients) use reference checks...

Have you ever gone on a long internet binge, researching and surfing mindless things, and thought to yourself: I wish I could make some money surfing the internet and sharing the (sometimes useless) information I had just acquired? Well, now you can!

Have you ever noticed that whenever you setup your voicemail account after getting a new cell phone number, it asks you to create a security pin to access your voicemail from other phone lines?

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Lost the product key for your game? If you have to reinstall the game and don't have that key anymore, you're out of luck, especially if you didn't "buy" the game. But never be in fear of losing product keys again with today's Null Byte, where we'll be practicing a little bit of mind-kung fu.

I'm sure we've all heard about MSN and Yahoo! Messenger, right? They can be useful, but the setup can be quite time consuming for those who need to use it just once or twice—and the privacy statements are a real bother. For example, we must provide our real details. You could use Fake Name Generator, but if you get caught, you will have your account suspended. I don't have a law degree, but to my understanding the United States recently passed legislation that gives the authorities the power ...

If you've ever heard software piracy terminology being discussed, I'm sure the term KeyGens came up. KeyGens is short for key generator, which is a program that exploits algorithmic faults in software by generating software license keys that appear to be genuine. Normally used as a technique to protect the source code software and prevent piracy, a key generator exploits the key algorithm to effectively nullify the need for any software licenses. For example, we must try to find patterns in t...