As much funding as Magic Leap has secured, another round of funding will still catch headlines. However, the latest funding solidifies the company's strategy for succeeding in the consumer segment of AR.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

RIP Touch ID. Apple's fingerprint sensor on iPhone and iPad models with Home buttons is about to become phased out on Wednesday, Sept. 12. While Touch ID will remain an integral part of models from the iPhone 5S to the iPhone 8 Plus, as well as the iPad Air 2 through the sixth generation iPad, Face ID will completely take over as the default security method for unlocking future iOS devices.
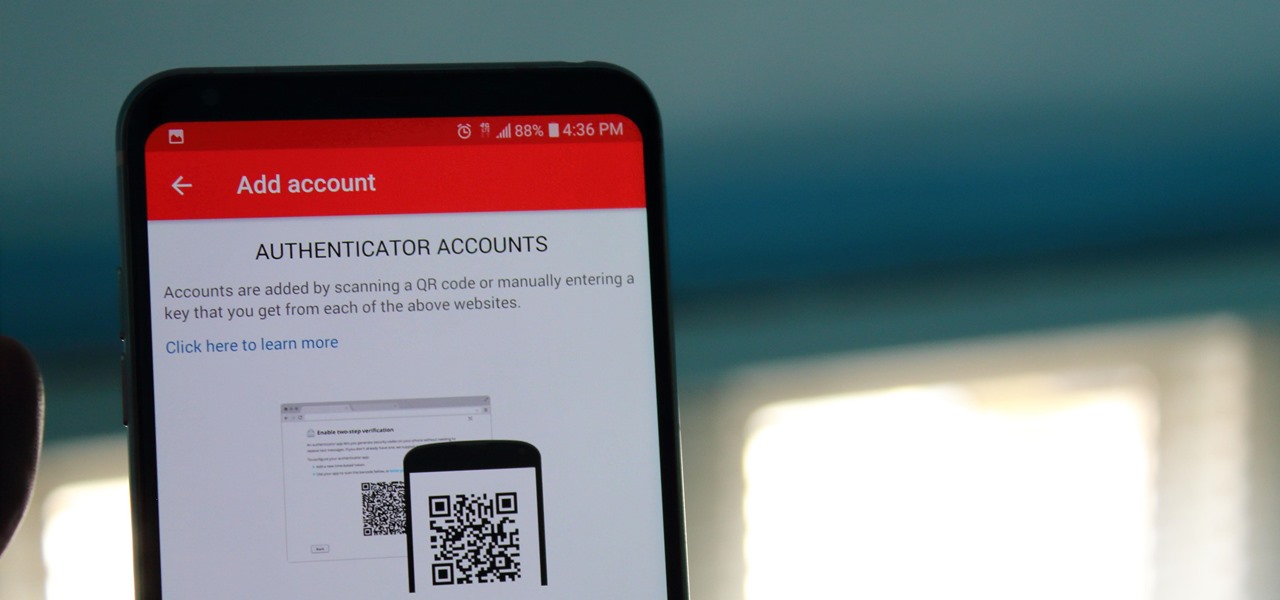
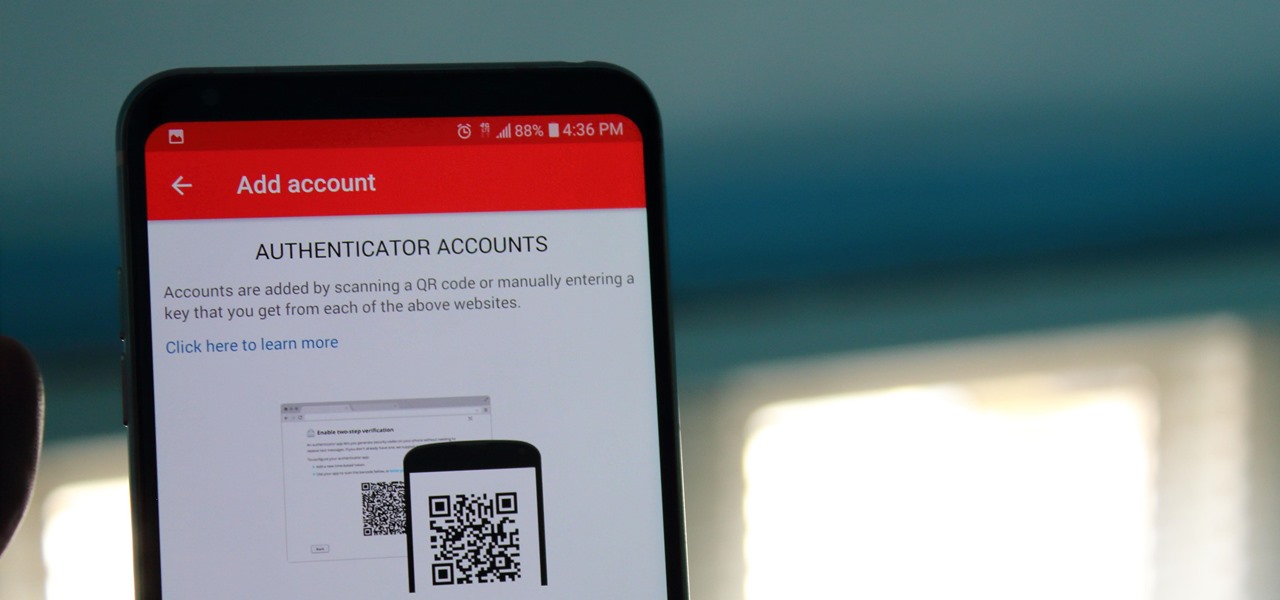
If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

Transferring hundreds of screenshots, webcam recordings, keystroke logs, and audio recordings between your VPS and a local Kali machine can be tricky. Services like Dropbox don't always have the best privacy policies and suffer data breaches just like any other website. To mitigate these risks, we'll use a secure, open source, and decentralized alternative.

We know Android 9.0 will have the formal designation of Pie, following Google's age-old tradition of naming their OS after items you'd normally find on a dessert menu. And thanks to a slew of new features that centers around your overall security, P could also stand for Privacy.

Apple has introduced a special edition iPhone 8 and 8 Plus to bring attention to the ongoing worldwide battle against AIDS. As the second iPhones to carry the (PRODUCT)RED name, these rare iPhones may quickly sell out when preorders open up on Tuesday, April 10, at 5:30 a.m. (PDT), so we'll go over some tips to help you secure a red iPhone before it's gone.

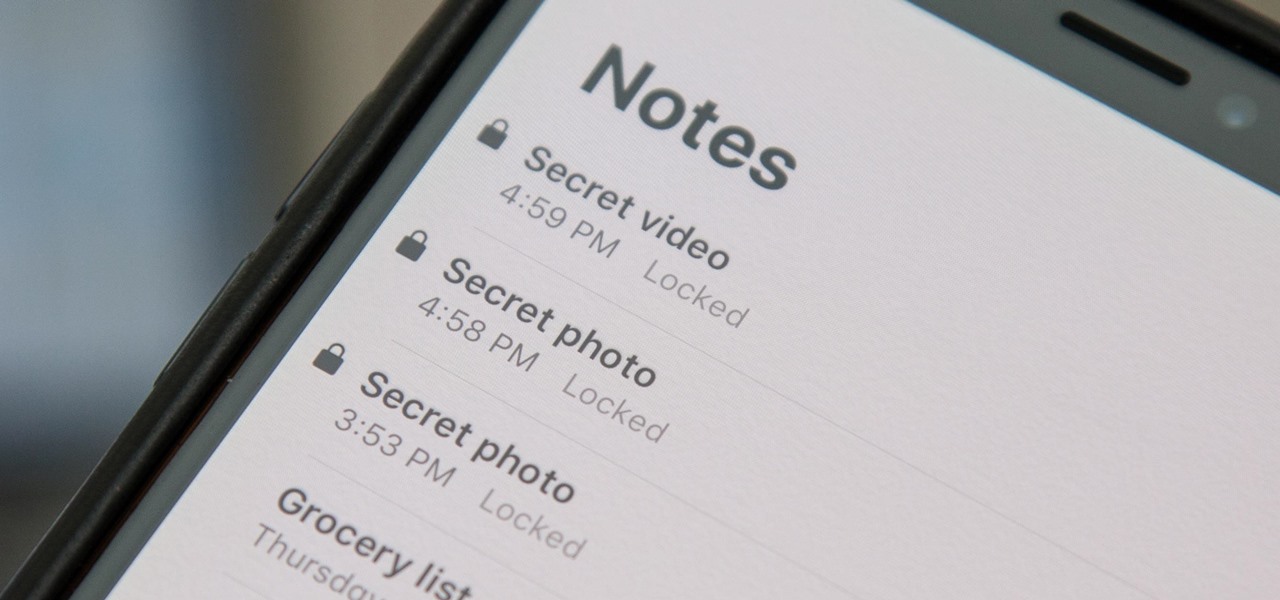
When a photo or video is just too sensitive to leave laying around in your Photos app, you'll want to either delete it for good or hide it away in safe, secure location on your iPhone. As for the latter, Apple actually has a few tools available to make photos and videos hidden — even password-protected — on your iPhone.

One unique feature of Firefox Mobile is extensions. Extensions allow users to add in features that didn't originally come with the browser. These add-ons provide an array of features, including improvement to privacy and security.

As of 2016, there are approximately 1.85 billion Android smartphones worldwide. This growing popularity has led to an increasing number hacks and cyber attacks against the OS. Unfortunately, Android users need more protection than what is offered by Google. The good thing is that there are a number of options available.

BlackBerry's focus on secure software and their new partnership with manufacturer TCL are two of the biggest factors in their recent resurgence. Last year, the company announced two new devices — the KEYone and the BlackBerry Motion. The KEYone has been available for a while, but after months of waiting, BlackBerry announced the Motion will hit US shores in a few days.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

This tutorial was written with Windows 7 in mind, but the principle applies to all versions starting from 7.

to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?

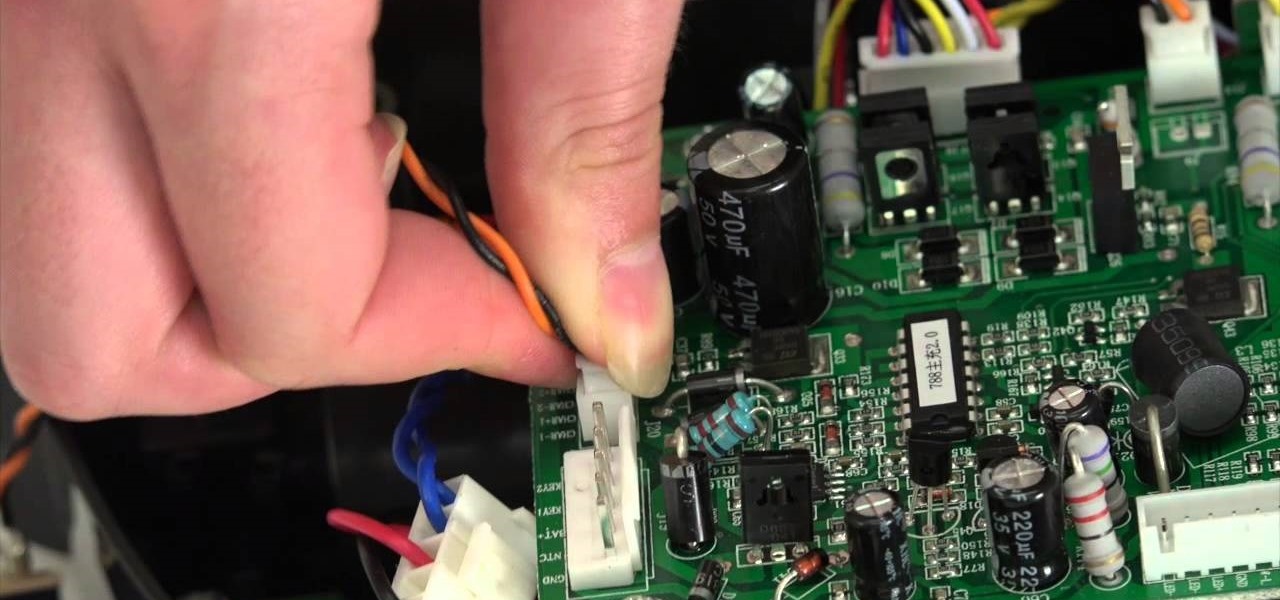
The guide will walk you through a power switch replacement on a bObsweep Standard or Pethair. It includes:

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

The internet is forever. When you put something out there, it can easily be re-shared, floating from server to server indefinitely with no way of taking it back. It's a scary thought when you consider that a young adult's grandchildren will one day have access to their drunken party pics.

As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.

With all of the personal data that's stored on our smartphones, it's of vital importance that we have some sort of lock screen security enabled. One of the Galaxy S5's killer features is obviously the fingerprint scanner. It makes the process of dealing with a secure lock screen a bit easier than typing in a password or PIN.

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

Quickly turn a profit during a combat mission by ratting - killing NPC enemies who spawn in asteroid belts. The difficulty of rats depends on how secure your system is - the lower security, the harder the rats are to kill. This tutorial shows you the best way, as a new player, to earn money by ratting.

In order to install Warmups Underfloor heating system, you will need the following: a Warmup Thermostat, a Warmup Kit, RCD, a multimeter, a permanent marker, measuring tape, tape, and scissors.

In this tutorial, we learn how to do braided hairstyles step by step. To begin, make a small section an inch wide and then section it into three parts. Cross them over like a braid, and as you go along, pick up pieces from each side and work it into each braid. Keep gathering hair until you get all the way down, then clip into place when you are finished. You can then use this piece of hair to pin back off of the face. Do this on the other side of the hair to create an equal look. Finish the ...

In this tutorial, we learn how to change the engine oil in a Chevy truck. To start, you will want to place your car up on a secure jack so you can get underneath it with ease. Next, find the oil can and drain plug underneath the truck and use a wrench to remove the bolts around them. Now, place an oil pan underneath the drain plug and let the oil leak out into this until there is no more left. Next, clean off the bolt that is used for the drain plug and remove the filter from the underneath o...

Paula Dean shows us how to make Filet Mignon for a romantic dinner for two in this video. Marinate your steak meat in the refrigerator using a plain Italian salad dressing. You can use a bottled dressing or make your own, if you prefer. Marinate for about 4 hours, 2 hours on each side.

First of all you need a handkerchief or a cloth napkin. Make sure that it is clean for use. Now start by folding the two opposite corners together. This shall make a triangle. Now you have top fold the two middle bits so that they overlap at the center. Now start rolling them together upwards. It is very important that you are rolling them very tightly. This shall make the body of the mouse solid otherwise it may fall apart. When you have made a solid roll then fold the two ends upwards as sh...

This video by repairs universe shows viewers how to replace the battery in the 2nd Generation iPod Touch. The tools you will need for this project include safe-open pry tools and a small phillips head screwdriver. To begin, remove the screen by releasing several clips that hold it to the frame using the safe-open pry tool. Run the tool between the case and the glass along all edges. Gently pull glass off and pry off the digitizer. Next, remove the small screw in the upper corner, lift up the ...

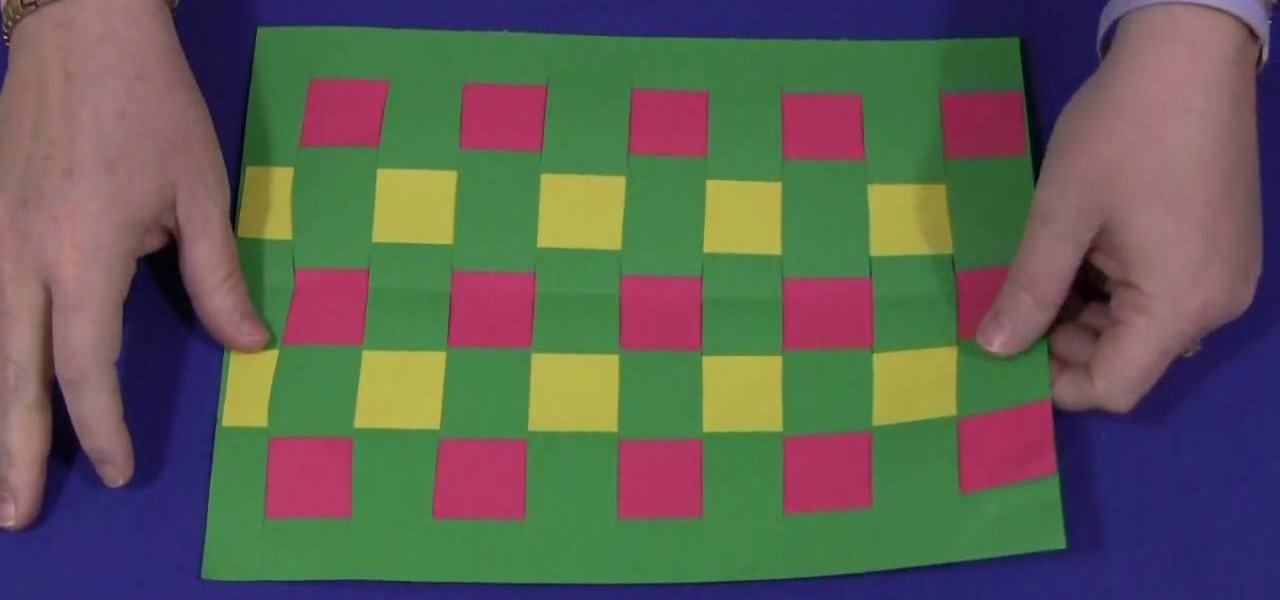
This is a project to keep your kids entertained. It is also a great way to practice hand eye coordination and motor skills. The materials that you are going to need are; construction paper and something to cut the paper with.Depending on the age of the child you can use 3 colors or more for older children and 2 colors for the younger children. Color choice is left up to what the child wants.To get started take a full size sheet of construction paper. Fold this paper in half length-wise. Take ...

The Mac OS's Disc Utility allows for the encryption of files. To open Disc Utility click on the magnifying glass (spot light) up in the top right hand corner, and search for Disc Utility. Click on the first result in the list. Once Disc Utility is open, click on "create a new image" in the top tool bar. A new window will drop down, where you choose what you want to save the new image as. Give it a name, and choose the size you want it to be. Moving down, choose the encryption you want to use ...

This video shows you how to create a continuous, daisy-chain necklace. The materials used include: size 11 rock eyes in yellow, red and purple, a toggle clasp , 9mm thread and a size 10 beading needle. Start by sewing on one half of the clasp, tying a knot to hold it in place. Be sure to leave the tail ends long enough to be able to re-thread it later with a needle to sew the tail ends. The video then shows the precise order in which the various beads are threaded through to produce a chain i...

Cute Girl Hairstyles shows you how to create a French braid hairstyle for your hairstyle. Firstly, divide the long hair into two parts with a zig-zag parting on the top of the head. Keep one half of the hair in a ponytail to keep it out of the way. Wet the hair down, and take a small section of the hair. Section that part into three and repeat. Cross the first piece with the second piece, and then cross the third piece over (braiding). Pick up hair and add it to the left lock and repeat. You ...

The Trilene knot is a multi-purpose knot that can be used in fishing to attach hooks, swivels and lures. This is a great knot because it resists slips and failures.

This video describes how to solder a wire. The first thing you have to remember is that the wires should be cleaned, shiny, and bright. Then trim about 1/2-inch of the insulation of the wires and then make a secure mechanical connection. Next, put some soldering pencil clean and shiny 60/40 rosin core solder. Do not use 50/50 core solder. Start by making sure that the soldering iron is tint. Put the soldering iron underneath the joint. Heat tends to rise and then touch the solder to the joint...

Clean out the empty bottle that you are going to use. You can use a white dish-washing soap bottle or a cleaning agent bottle. Just make sure it is empty and clean. Use the pen to draw a wide rectangle that measures 3 inches long by 1/4 inch wide onto the bottle. The teeth you are making are going to stretch from either side of your canine teeth above and over your two front teeth. This will help them be more secure. Draw this onto a part of the bottle where it is curved. Draw two vampire tee...

See how to make a very tall, simple, yet elegant centerpiece for weddings and other events. You first need a tube and a base that it will fit into. Placing the tube in the base, use a hot glue gun to secure the tube into the base. You can then fill up the balloons with air using an air pump and tie pairs of balloons together. Twisting together four balloons, place the cluster of balloons around the base of the tube. Repeat with an additional 8 balloons and place this cluster at the top of the...

This video shows you how to remove and replace a sink basket. It's real quick and very efficient if you have a new sink and an old basket. Here are the steps on doing this.

Learn how to make a sword out of cardboard with this video. Materials: