To create an elegant WordPress blog or website from scratch without being noticed that you're a complete beginner, you need that drive and pairs of eyes and ears. It may seem difficult at first but it can truly be fun and exciting.

In this tutorial you will learn how to create glossy web icons in Illustrator CS2. Very often you will be able to download royalty-free icons from the Internet, but the problem is they are not customized to fit in with your existing web site's design. So creating your own icons is always a good way if you have the time to do it. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Create glos...

Technology: The Less You Know the Better?

A press release should be about news. It should have a sense of urgency about it and grab the reader’s attention from the outset. A good press release must quickly answer the journalist’s immediate questions:

You want to put out a live web server, but you don't want to be owned in the process. An expert eye for security is not needed if you take a few basic steps in locking down the hatches. Most successful attacks today are not the complex, time-consuming tasks you might think, but simple lapses in policy that a hacker can take advantage of to compromise your server.

Remember that scene in The Matrix when Trinity uses a realistic Nmap port scan, followed by an actual SSH exploit (long since patched) to break into a power company? Well, believe it or not, but that scene is not far fetched at all. If you want to exploit vulnerabilities and root boxes, you'll need to learn how to perform the necessary reconnaissance first. In fact, you will spend far more time researching your target then you will exploiting it. In this article, I am going to show you the fi...

In the first part of this series, we learned about darknets, as well as how they came about. But these patches of forgotten Internet are not the oasis of free information you might think. Despite being hidden—or just harder to come across—these networks are no more safe then anywhere else on the 'clear' Internet. The nature of networking and routing means your location is always known in server logs. It only takes one phone call to your ISP with your IP address to obtain both your physical ad...

G+Me is one of our favorite Chrome extensions here at Google+ Insider's Guide. We love it because it's one of the most comprehensive extensions out there. It attempts to address the "noisy streams" issue, with list mode, and collapsible posts and comments. The creator, +Huy Zing, is very responsive to feedback, and he's been quick to address any issues that arise, including privacy concerns. He's even created a G+Me (Paranoid Edition) extension, for the extra careful Google+ user. And if you ...

This step by step tutorial teaches you how to apply gothic spider web eye makeup. This is a cool look for Halloween or a costume party. Watch this makeup how to video and you will be able to create a gothic spiderweb eye look. Apply gothic spider web eye makeup for Halloween.

This video will show you how to bypass those pesky home or school web filters Bypass school or home web filters.

This video will show you how to create a simple and quick web photo gallery in Adobe Photoshop. Create a web photo gallery using Photoshop CS3.

In a recent arbitrage tip, we showed you the secret to making money fast by buying and selling the same thing over and over again on eBay. But there's one thing you need to know about the buying part—get the lowest price possible! This article aims to show you some of the best methods to making sure you're paying the lowest prices on eBay, so you're the best arbitrageur out there, with your profits higher than ever!

Does your network begin to crawl right around the time your sinister-looking next-door neighbors get home from work? Do you harbor suspicions that one or more of them may be stealing your Wi-Fi? It's easy to find out. And equally easy to give freeloaders the boot. In the guide below, we'll show you how to secure your wireless connection in three easy steps.

Google's much anticipated eBook Store has finally opened. As of today, the digital bookselling enterprise is awaiting your needs, with over 3 million eBooks to read directly on the web or on other platforms, like Android, iPhone, iPad, Sony and Nook devices.

A recently closed Worth1000 contest, Senior Rebellion, showcases "old folks that won't make you get off their lawn". Good ol' Photoshop magic at work.

How to surf the net anonymously with a proxy. Download and use a proxy for anonymous web surfing.

In this Adobe Premiere Pro video tutorial you will learn to create a custom sized document for a video web banner. Learn how to change to the values for Timebase, video frame, and audio rate. Their values will determine the quality and delivery speed of your video banner. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Create a video web banner in Premiere.

The executable file association virus deletes the "Regkey" that associates ".exe" files with the proper Windows execution. The virus can be contracted while browsing the web, from an infected file, or even from pictures and documents. Once the damage is done, Windows will show a window similar to the one below, and will ask you for the correct program with which to open the file.

Have you ever browsed the web, watched a video, then wanted to download it? Well, there's a fabulous program that does just that, simply and easily. It's called VideoCacheView by NirSoft. The program basically extracts the FLV video directly from your browser's temporary folders. It's very user-friendly, and great for downloading virtually any online video.

Before, eReaders were only used to read eBooks. Not anymore. As tablet computers become more and more advanced, eReaders like Amazon's Kindle, Sony's Reader and Barnes & Noble's Nook are forced to expand their capabilities beyond the basic bibliophilic needs. And the first to make significant headway is B&N's Nook Color.

In this tutorial, Geoff Blake uses the slice tool in Photoshop to divide up a header image and then takes it into Dreamweaver to display it on a web page. For more information, including detailed, step-by-step instructions, watch this free video software tutorial.

Interested in creating your own dynamic, web-based applications using Microsoft Visual C#? How about an RSS reader application? This lesson shows the design and planning of the RSS reader application. For more information, as well as tips for being a more effective user of Microsoft Visual C#, take a look at all five videos.

There is an option in Flash that allows users to capture the data coming from a web cam attached to the computer and broadcast it using Flash.

Some of you might be using Tor to host hidden services, and some of you might not even know what hidden services are. If the latter's you, do not miss this article. Why? Because you can host your websites and services on the I2P darknet. It's safe and secure—it's anonymous.

Pull up outside any construction site and you'll see tools scattered about—hammers, jigsaws, nail guns, hydraulic pipe benders—these are the tools of the trade. You would be hard-pressed to build a home or office building with just your hands! On that same page, security professionals also have their own go-to tools that they use on the job site, only their job site is your server.

This is Part II in the Lockdown: The InfoSecurity Guide To Securing Your Computer series. Before beginning, check out Part I. This article will cover using alternate software to increase your security and will provide you with some information about websites and programs that test a computer's security. It will also guide you to software you can install or follow so you know what programs need to be updated on the computer. Lastly, I will talk about some features that should be disabled when ...

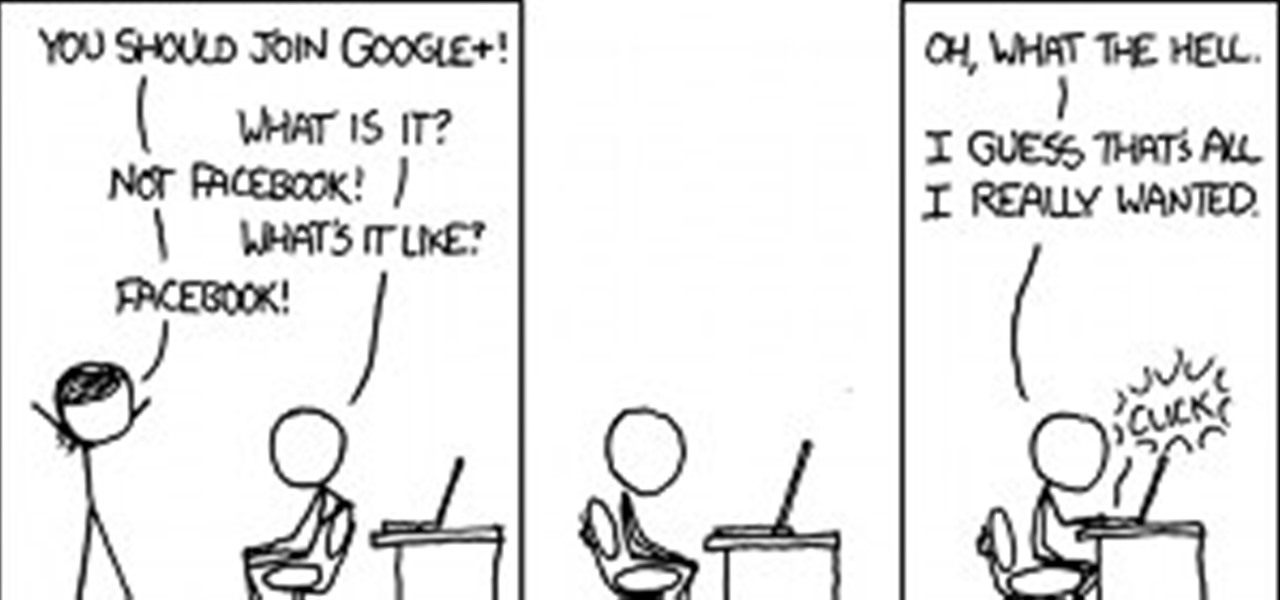
Antimatter15, author of the popular Surplus Chrome extension, was suspended from Google+ for using a pseudonym instead of a name that fits Google's community standards. As such, he's no longer supporting the extension, and if you're using it, now might be a good time to find a replacement. It's a reminder that nothing on the web is guaranteed to work forever. Luckily, there's no shortage of innovative coders whipping up creative and useful Google Chrome extensions.

ClariTrans is a requester on MTurk (www.mturk.com) they pay very well for transcribing short snippets of audio. Here is how you can transcribe their audio snippets properly to ensure your text will be approved and you will be paid:

Have you ever noticed that whenever you setup your voicemail account after getting a new cell phone number, it asks you to create a security pin to access your voicemail from other phone lines?

My girlfriend was going away for a few weeks, but where she was going, there was no easily accessible Internet. She works mostly on the web, so it was imperative that she have a decent Internet connection during her travels. So, tethering her phone was the only real possibility.

Download Cheat Engine You can get Cheat Engine here. After downloading, install it on your computer.

The visual beauty of images on Google+ means that it's not just a great place for photographers to shine, but also serves as a befitting promotional space for web comic artists. Below, 7 talented individuals who have utilized the Google+ platform.

We all want a faster, more efficient web browsing experience. Some immediately flocked to Google Chrome as soon as it was released, because of its super fast speeds. Others restrained themselves and continued to wait for Microsoft and Mozilla to play catchup. And the time is almost here for all Internet junkies to improve their game.

The figure of eight is commonly used to attach a rope to a climbing harness. Being able to tie a figure of eight knot properly is an essential climbing skill. If the climbing rope is attached incorrectly to the harness, the consequences could be fatal.

New to eBay? Don't worry, setting up an account and buying and selling doesn't take that much effort at all. Everyone who has an Internet connection has at one point come across eBay, to find the perfect gift for their loved ones, to find the cheapest deals on plasma televisions and computers, or to get rid of their dusty, old record album collection in their web store.

New to eBay? Don't worry, setting up an account and buying and selling doesn't take that much effort at all. Everyone who has an Internet connection has at one point come across eBay, to find the perfect gift for their loved ones, to find the cheapest deals on plasma televisions and computers, or to get rid of their dusty, old record album collection in their web store.

If you've read my darknet series, you've probably got a pretty good idea of what I2P actually is and is capable of. One of the features of I2P is that it's designed with P2P file sharing in mind. Using a built-in service called I2PSnark, you can host and seed torrents quickly and easily!

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Eventually, we plan on doing some root the box competitions here at Null Byte, but we're still looking for a server to play on. Anyone want to donate one? You won't regret it. Root the box is like 'king of the hill', except you have to hack a server and maintain access. Each server will have numerous known security holes, but until then, let's get back to the regular weekly coding sessions and realistic hacking missions on HackThisSite.

Here's something fun for the Null Byte community to do—a coding competition! This week, I wanted to get everyone involved by offering you all a nice library of possible program types to choose from and try to code. At the end of this competition, all of the submitted programs will be reviewed by the community and myself. The coder that receives the most votes will be dubbed THE BEST.