After 12 years Starcraft 2 is finally here to blow your mind. If you're looking for help with the game, you've come to the right place. We have tons of videos about how to do just about everything in the game. We have strategies for winning campaign and multiplayer games. We have guides to using the immensely powerful level editor. We'll even teach you how to build a Terran Barracks out of Legos. This video will show you how to you can make a mobile wall of supply depots on your Terran base's...

Unless you're an actual mermaid or a member of the Na'vi, this insane mermaid look probably won't get you any propositions on the street.

Purple cabbage is a natural indicator and this video teaches you how to easily prepare purple cabbage in the comfort of your own home to be used as an acid and base indicator. Take one leaf of your purple cabbage, tear it into smaller pieces and place all the pieces into a beaker or bowl of boiling water for an hour. Collect the liquid from your mixture into a bottle. You’ll notice that the liquid is now dark blue or purple at which point is neutral. It is ready to be used as an indicator. ...

A percent problem is one in which you are given a quantity and asked to compute the value of a percent of it. You may also be given the whole quantity and a part of it and asked to compute the percentage of the part in the whole. To do these kind of problems you need to use the rule which states that the ratio of the part to the base it equal to the ratio of the percent to hundred. That is part/base = percent/100. This comes from the definition of percentage which states that percentage is eq...

In this tutorial, you will learn exactly how to make a router-based inlay. And inlay is made up of small cut out sections of wood, and looks like a stencil or pattern when you are finished.

The ancient art of Japanese paper folding is broken down and explained clearly in this video. The video teaches how to create a beautiful bookmark of your own design from a simple single sheet of paper. The instructions use the square base as a jumping off point for showing you how to easily make a custom book mark. There are a few simple beginning steps, and after you complete those you will be able to fold and crease your way to a gorgeous custom origami book mark.

Ingredients for Hiyashi Chuka (serves 2)

The Hairy Bikers explain the best way to cook Noah's Pudding, a milk and rice based dessert. Delicious recipe idea from BBC foodshow 'Hairy Biker's Cook Book'.

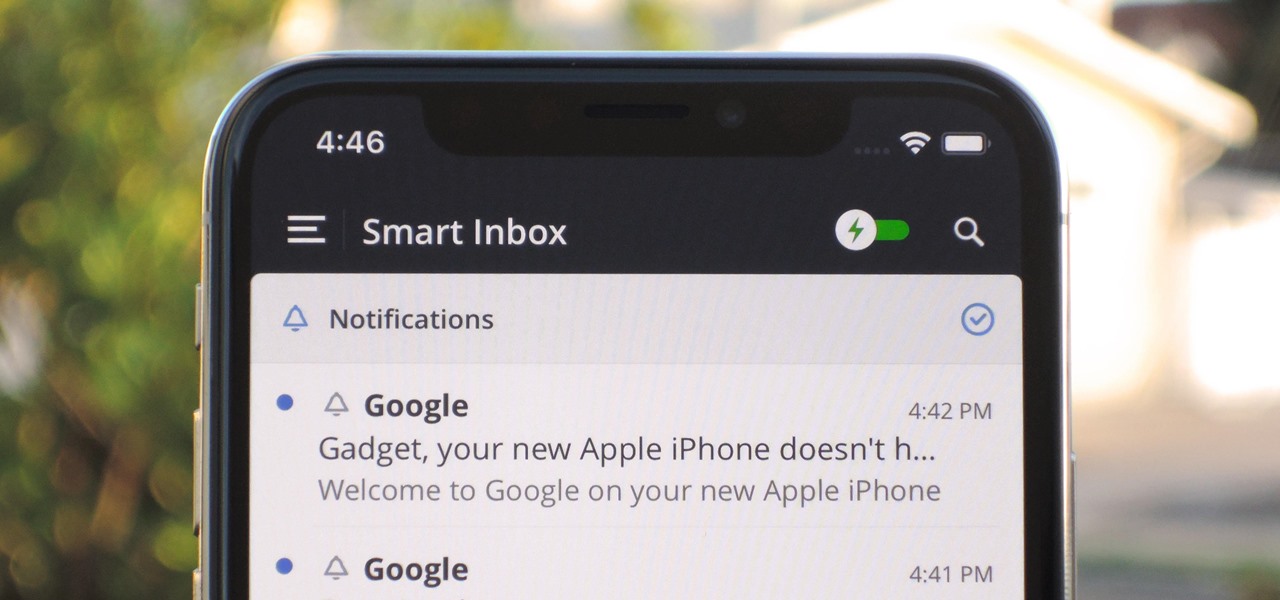
In the last decade, the number of people working remotely in the US has increased dramatically, and so has their need for technology and software to supplement that remote work. Whether you work from home or a coworking office space, the requirement for highly compatible and helpful productivity apps is a must if you want to get things done successfully.

We may or may not see Apple's long-awaited take on AR smartglasses this year, but the company is more than getting its practice swings in with its current wearables business, which hit record revenue in 2019 according to financial results released this week.

Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

A relay is an electrical component that works like a light switch, where it's turned on or off with an electrical signal. By connecting a relay to a Wi-Fi connected microcontroller like an ESP8266, you can build a connected switch that can be controlled from the web browser of any device connected to the same Wi-Fi network — all for just a couple of dollars.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

For some of us, mornings are difficult. But if you can manage to start your morning right, you can trigger a chain reaction that leads to a more productive day. Fortunately, our phones have the tools to help us get off to a good start.

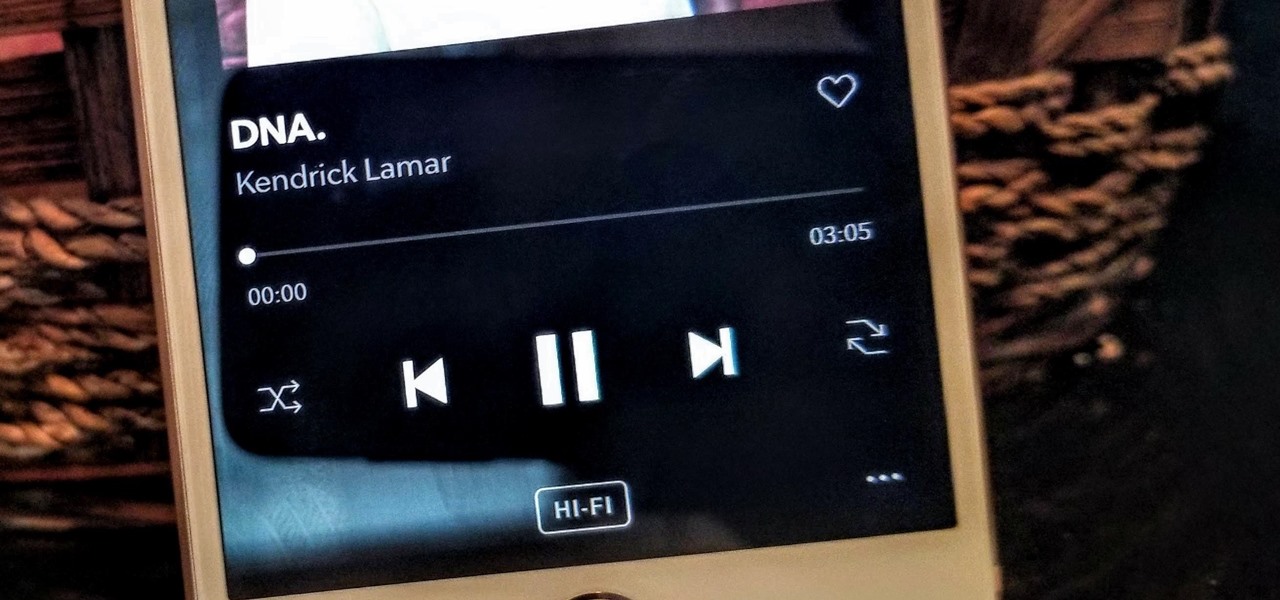
Thanks to their partnership with Tidal, over 30 million Sprint customers can access Hi-Fi audio on the go. And the Jay-Z-owned music service isn't limited to just Sprint customers — for $19.99/month, anyone can listen to lossless audio from their favorite artists. But streaming uncompressed audio files uses a lot more data than standard quality, so how do you use Tidal without hitting your data cap?

With the release of the Mirai source code, botnets are back in a big way. In the early days of botnets, zombies (infected hosts) would report to IRC (Internet Relay Chat) channels for CNC (command and control) instructions. Modern botnets have evolved, but they continue to use the same concepts as their predecessors.

While Magic Leap and ILMxLABs blew the internet's collective mind with a mixed reality Star Wars game demo last week, it'll likely be awhile before we see either the game or the hardware that'll run it. In the meantime, you can get one of the most famous Star Wars holographic messages on the HoloLens: Princess Leia's message to Obi-Wan Kenobi.

Do you ever thought that you can't control an Internet disconnected system? I saw a funny video in Chema Alonso's youtube channel (A well-known hacker of my country and creator of Fingerprinting Organizations with Collected Archives among other security tools), and decided to post something similar.

With each day that dawns, there is a new, major hack that makes the news headlines. If you are paying attention, there are usually numerous hacks each day and far more that never make the news or are kept private by the victims. Every so often, a hack is so important that I feel compelled to comment on it here to help us learn something about the nature of hacking and IT security. This is one of those cases. Last week, the U.S. Office of Personnel Management (OPM) revealed that they had been ...

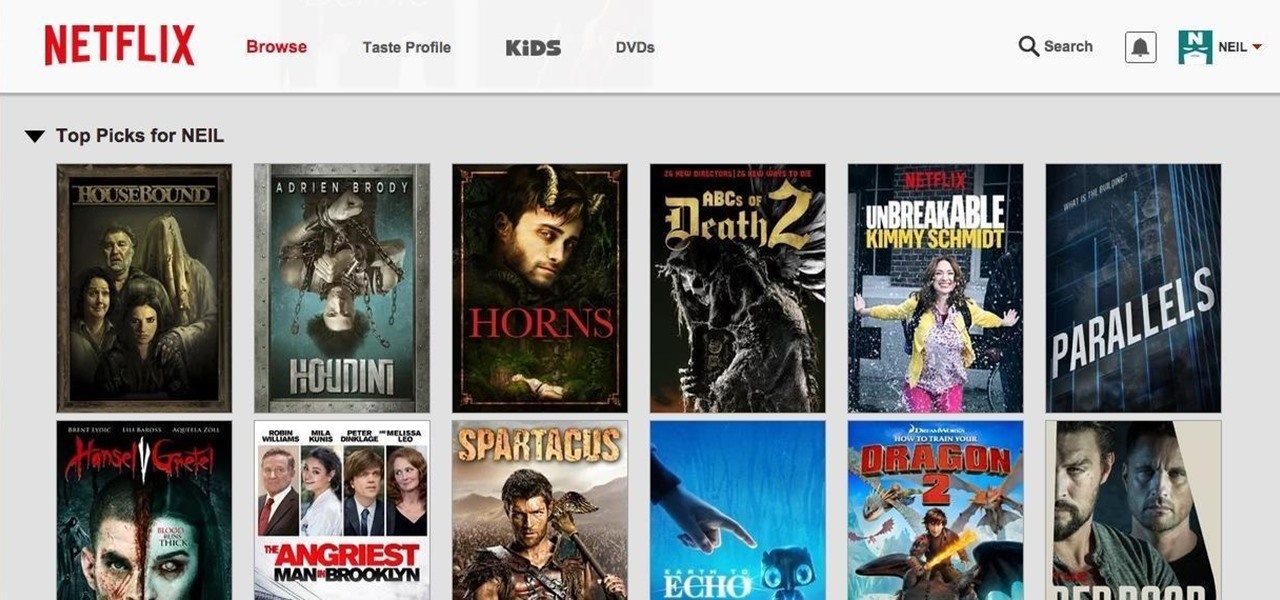
Netflix was my proverbial gateway drug to cord-cutting, as I'm sure it was for many others. Yet as much as I truly love Netflix and its service, there are some annoyances I have with the interface of the desktop web version.

In the wake of the NSA scandal and celebrity-photo hacks, lots of people scrambled to find more-secure ways to send text messages, share emails, and surf the internet. Known for their incredibly secure data networks, Germany's email services saw a remarkable increase in new users from across the world. Last year, we covered Sicher, a German app that lets you send and receive encrypted self-destructing messages on your smartphone.

In a long-awaited move, the popular messaging platform WhatsApp has finally made its official web debut. Desktop and laptop owners will be happy to know that they can now message their favorite contacts directly from their computers, without the need to install additional apps.

Anytime you surf the web on your iPad or iPhone, Safari saves which webpages you visit, the information you enter into them, and other types of data. This not only make your internet experience quicker, but it'll also keep track of everything you're doing.

The Play Store is loaded with just about any app you can imagine. While many are free or have a "lite" version of a paid app for download, often enough, these freebies have intrusive ads cluttering up your screen.

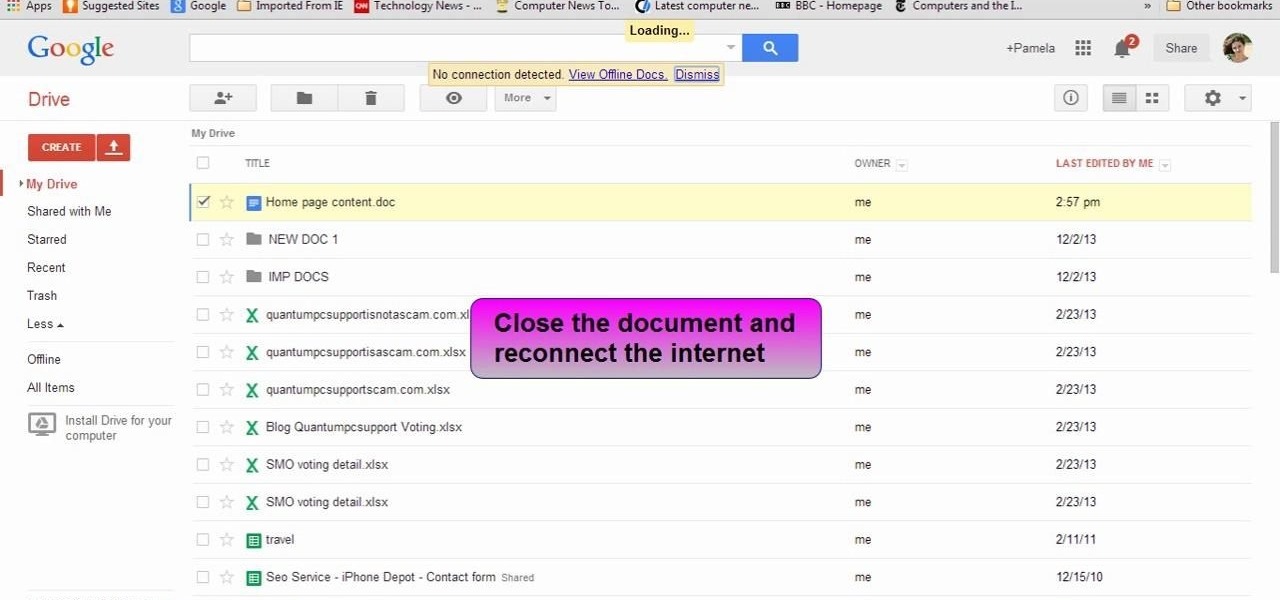
This video will show you how to view and edit Google drive documents offline. You could do this only in Google Chrome browser. If you are editing or viewing a Google drive file and suddenly internet connection is gone, you can still view and edit. You should only download an app for it. It will save your changes offline and will automatically update when you will reconnect with internet. Follow the video and do it in your Google Chrome browser.

It's time to enjoy one of America's longest lasting favorite pastimes. No, not baseball—pranking our friends! With the internet currently overrun with countless pictures and memes of cats, there's no way for your feline-hating friends to surf the web without coming across a kitten or two. But things can get worse for them. Way worse...

When browsing the web, you may not be quite as anonymous as you think, especially if you are using public WiFi. The easiest way to stay as anonymous and safe as you are going to get, is to use a VPN (there are a number of great free ones). In this tutorial, we will show you how to set up a VPN on Android, and how this protects you.

Welcome back, my tenderfoot hackers! Not too long ago, I showed how to find various online devices using Shodan. As you remember, Shodan is a different type of search engine. Instead of indexing the content of websites, it pulls the banner of web servers on all types of online devices and then indexes the content of those banners.

You may not always be connected to the internet, but if you're anything like me, your thirst for web content is insatiable. Whether you're on an airplane or stuck in an area with no reception, having some offline content stored on your Nexus can definitely save the day.

For over 20 years, a tiny but mighty tool has been used by hackers for a wide range of activities. Although well known in hacking circles, Netcat is virtually unknown outside. It's so simple, powerful, and useful that many people within the IT community refer to it as the "Swiss Army knife of hacking tools." We'll look at the capabilities of Netcat and how the aspiring hacker can use it.

Google Reader is soon to be no more. Yesterday, the company announced that the service will be shutting down as of July 1, 2013, as part of Google's second "Spring Cleaning."

Clearing the cache on your computer is (usually) a quick and easy way to help speed it up. Deleting those temporary files frees up space, helping you computer run smoother, especially if you have not cleared the cache for a extended period. However, finding the different caches in Windows 8 is a little trickier than in previous Windows systems.

» Homeland Security Report Lists ‘Liberty Lovers’ As Terrorists. A new study funded by the Department of Homeland Security characterizes Americans who are “suspicious of centralized federal authority,” and “reverent of individual liberty” as “extreme right-wing” terrorists. » British police get battlefield weapons.

If you’ve never heard of the term search engine optimization or SEO, then your website probably isn’t optimized for search engines and it’s hindering your site’s ability to get all of the traffic that it should. Read on for an explanation of what this entails and how it can help your website.

Have an HTC smartphone? Chances are that some of your stored personal data has been hijacked by malicious apps on your device. Android apps that have permission to access the Internet, which is pretty much every ad-supported app out there, can snag valuable information such as email addresses, location history, phone logs, text messages, and more.

Security awareness seems to be a hot topic these days on the web, with developers making apps and devices that can hack networks and machines with just a few clicks. But these applications aren't only exploiting security flaws in systems and networks, they're being used by amateur and wannabe hackers who want to have a little fun, but don't want to learn how to actually "hack" anything.

It's been about five months since Google first unveiled their prototype future computers running Chrome OS, and the time is nearly here for the Chromebooks to be unleashed on the public. But there are a lot of qualms over the release of Chromebooks, with most criticism coming from their lack of traditional laptop-based features such as an optical drive, storage space and the ability to run comprehensive software programs like Adobe Photoshop.

Rovio's highly successful Angry Birds game has generated a slew of wannabe Angry Clones and dominated nearly every device and platform known to man—iPhone, Android, PSP, Xbox 360, Windows—and now, for the first time it's available for play directly on the web (for free). It was specifically designed for Google's Chrome OS and their new Chromebook line of laptop computers, but can play on any device in almost any web browser (like Firefox).
So precisely what is an affiliate marketer? Essentially, an affiliate marketer has an online site and also refers guests to some other sites, called 'merchants'. When these site visitors buy things, the other websites pay the particular online affiliate marketer a payment, which depends upon online monitoring softwares which monitors web customers purchases.

The New York Times magazine posts a fascinating feature on a Chinese cultural phenomenon known as human flesh search engines. Out of China has borne cyberposses, internet vigilantes, who target everybody from twisted individuals violating social norms to government corruption.