It's not listed as one of the features on the updated Nook e-reader, but there is a web browser hidden inside Barnes & Noble's newest device, you just need to know how to access it. The eBook Reader shows the clandestine web browser on the Simple Touch Reader in the video below, and it's fairly easy to access. Just open up the Nook's search function, type a URL into the search bar and hit the go button. It's that simple.
Even as we look forward to returning to work in person, the last year has changed how work can be done. That means there will always be a demand for good programmers and coders who can support the digital infrastructure of the online working world. The Backend Developer Bootcamp Bundle can give you the expertise you need to become a highly qualified programmer for only $29.99.
The "Zoombombing" trend is still strong on the Zoom video meetings service, despite security measures Zoom put in place to stop it. That's why it's up to you, as either a host or co-host, to be proactive about preventing Zoombomber harassment, as well as stopping it whenever it slips through the cracks.

Hacking web applications can sometimes be challenging due to the sheer amount of moving parts they possess. At the core of these apps are HTTP requests and parameters, but these things are often concealed from the user, due to security reasons, convenience, or both. However, a tool called Arjun can be used to discover hidden HTTP parameters in web apps.

Whether you were exposed to the COVID-19 virus or just taking precautionary measures, self-quarantining is a tremendous disruption for anyone. Still, we all have to eat, pandemic or not. But unless you like eating canned food for two weeks, you're going to want to explore other options. That's why food delivery apps are going to be so necessary during such a hectic and uncertain time.

Some of the oldest art on Earth was created 36,000 years ago on the walls of the Chauvet Cave in France. However, these days, physical access to the cave is restricted in order to preserve the site.

As demonstrated by holographic experiences for the Microsoft HoloLens and the Magic Leap One, volumetric video capture is a key component of enabling the more realistic augmented reality experiences of the future.

Automating port scanners, directory crawlers, and reconnaissance tools can be complicated for beginners just getting started with Kali Linux. Sparta solves this problem with an easy-to-use graphical interface designed to simplify a penetration tester's tasks.

Canary tokens are customizable tracking links useful for learning about who is clicking on a link and where it's being shared. Thanks to the way many apps fetch a URL preview for links shared in private chats, canary tokens can even phone home when someone checks a private chat without clicking the link. Canary tokens come in several useful types and can be used even through URL shorteners.

There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

Consumers are chomping at the bit for augmented reality smartglasses from Cupertino's finest, but one market analyst is saying not so fast, Apple fans. Meanwhile, automotive AR is gaining speed, with the latest milestone coming courtesy of a major investment in waveguides by Continental. And although mobile AR apps have already arrived, retailer Target is taking a different approach. So why is Target tinkering with web-based AR? Answers below...

It's fitting that students at the University of Washington can catch a glimpse of the new, 135,000 square-foot computer science building in augmented reality before construction is completed.

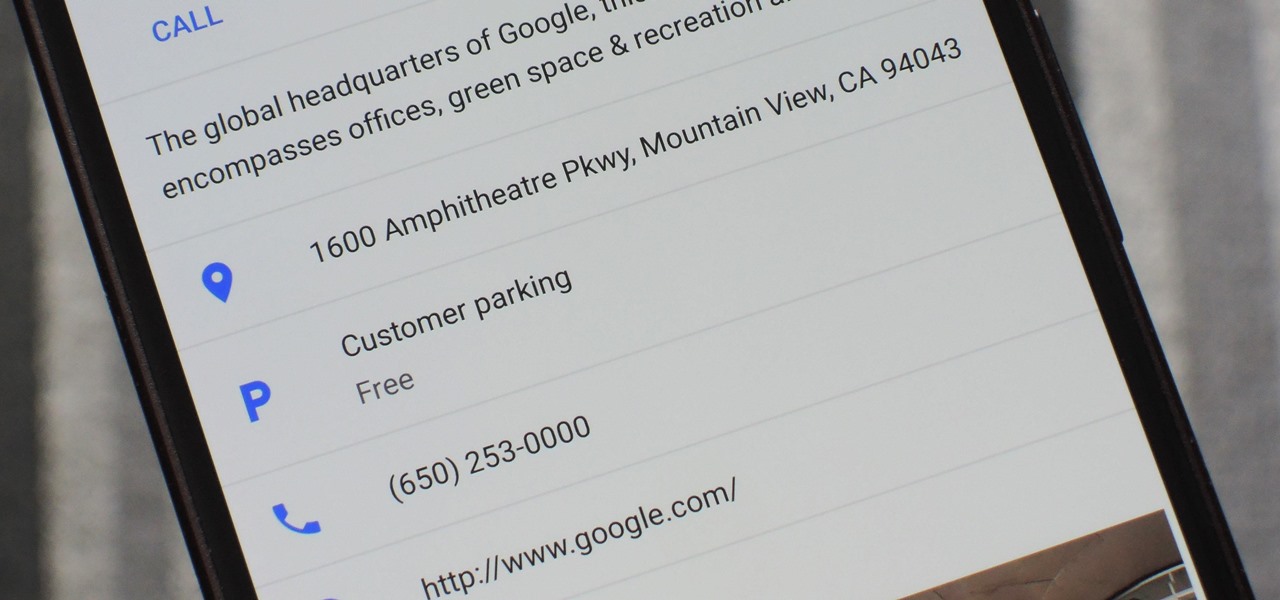
There's nothing worse than driving up to your destination only to discover that there isn't a parking spot in sight — but thankfully, Google Maps will soon have you covered.

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .

Welcome back, curious hackers! In today's tutorial, we will be diving deep into the manipulation of Google Operators, commonly referred to as "Google Dorks" in order to access Surveillance Cameras and other control panels.

Welcome back, my hacker novitiates! In an earlier Linux Basics tutorial, I had demonstrated the basics of the Apache web server. Since Apache is the world's most widely used web server on the Internet (as of July 2015, Apache was 38%, IIS was 26%, and Nginx is 15%), the more you know about it and understand it, the more success you are likely to have hacking it.

Copy and paste keyboard shortcuts are beautiful gifts from the gods, and any website that blocks such an offering can burn in hell. But really, Cmd+C and Cmd+V (Ctrl+C and Ctrl+V for Windows folks) are second nature to most of us, so it's very frustrating when sites like PayPal don't let us use them.

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

Most of us have some sort of malware scanner or antivirus program on our computers, but what about our smartphones? A lot of people don't realize that computers aren't the only devices that are susceptible to malicious software and apps—they can follow you on your smartphone or tablet, too.

Creative Commons is awesome—really. If an image, video, or audio file is tagged with a CC license, that means you can use it as long as you give appropriate credit to the owner. For bloggers with no money for pricey stock media, it's a godsend. When you license your own media under CC, you can choose how you want it to be used by others and whether or not it can be used commercially.

Check out this video for an introduction to the new Google+ app for iOS. You can use Google plus from any of your iDevices, including iPhone, iPod Touch and iPad. Make the most of Google's new social network with this app.

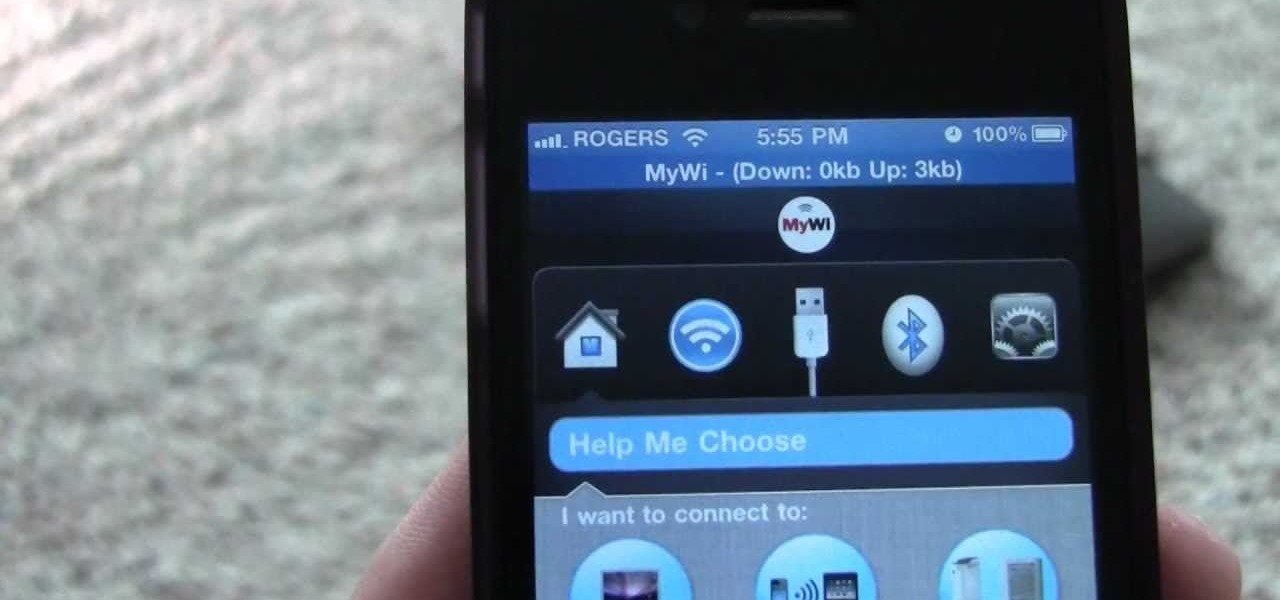
You can use your iPhone as a Wi-Fi hotspot to tether your Asus Transformer to it. Watch this video to learn how to set up wireless tethering on your jailbroken iPhone, and then surf the web with your Asus Transformer tablet.

So you know how to use a proxy server, but do you know how to set up a proxy chain? Proxy chains can be used to hide your tracks on the web. This video shows you how to use CGI and Tor to set up your own proxy chain.

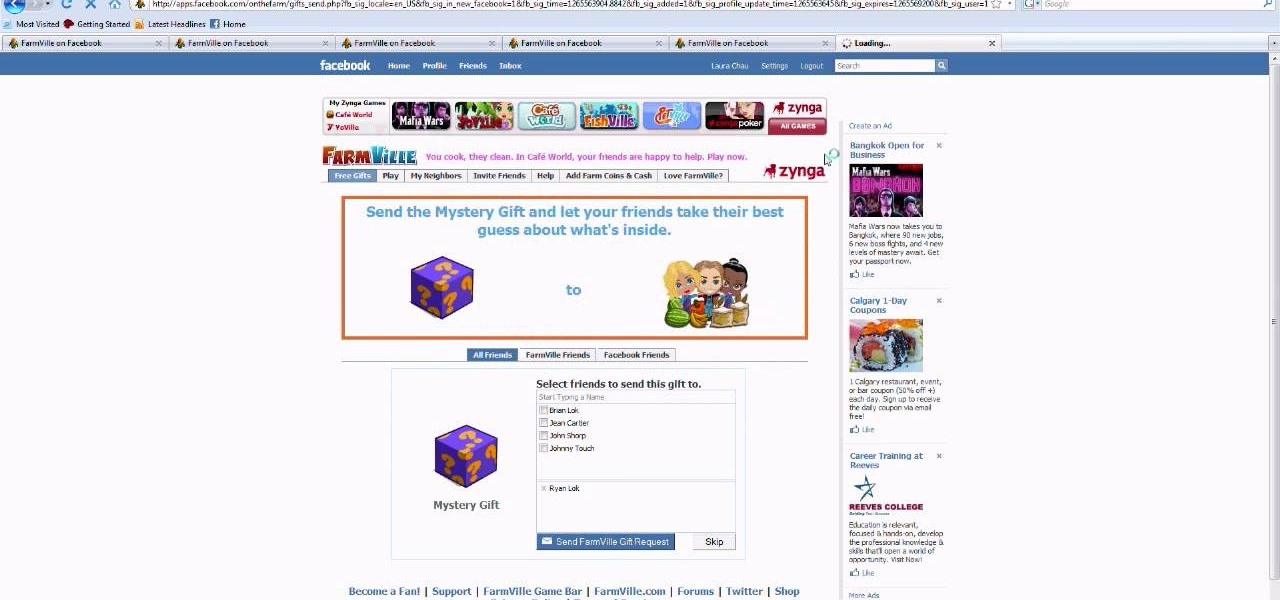
In Zynga's uber popular web game Farmville, you really do receive as much as you give out. Being a good neighbor to your cyber friends means you score lots of loot - via Farmville "gifts" - but you gotta send a few, too.

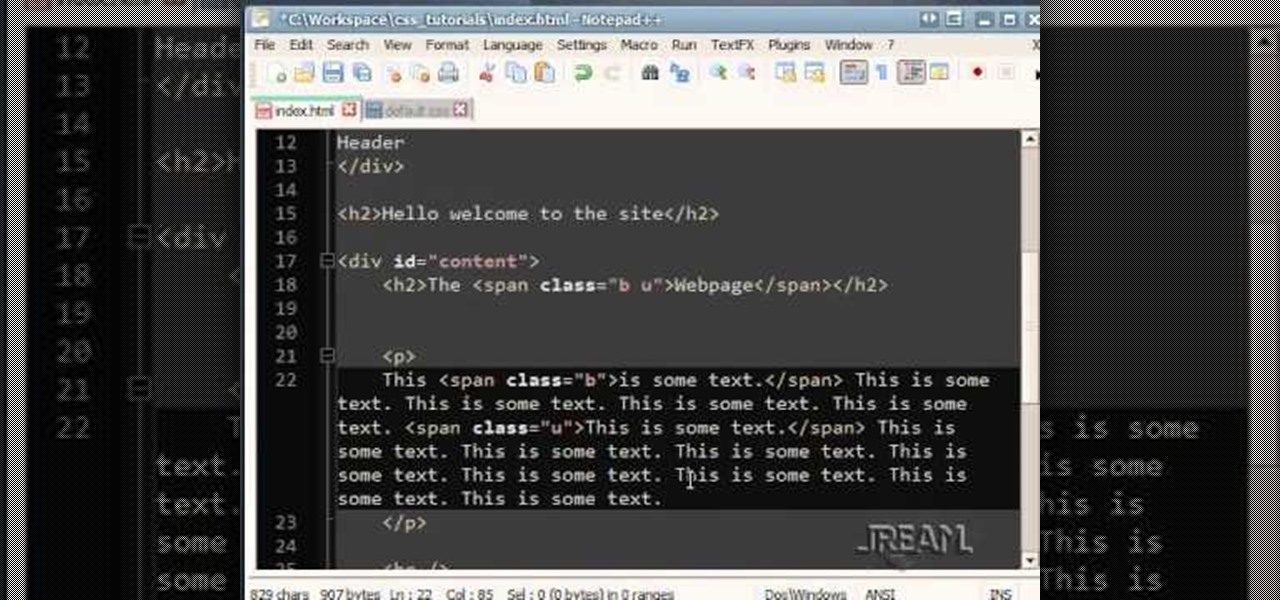
This tutorial gives a beginning web designer a few useful strategies for improving efficiency and productivity when working with HTML and CSS. Hierarchy is one of these concepts, and the video also covers grouping elements, overriding groups and Document Oject Model.

Amazon provides an inexpensive and useful data storage service that nearly any web admin can find useful. CloudFront is another valuable resource for admins, and this tutorial shows you how you can use both to increase the effectiveness of your own websites.

This tutorial shows you how to use some of the basic functions in Adobe Photoshop, including the ability to save an image in multiple file formats, to create a picture that you can easily use on your website or blog.

This tutorial takes a screencap of a popular website, and then shows you how you can use the tracing tool and use some of the principles of web design to create an effective layout for your own website using Adobe Photoshop.

Use all of your web apps on your T-Mobile G2! This clip will teach you how. Whether you're the proud owner of a a T-Mobile G2 Google Android smartphone or are merely toying with the idea of picking one up in the near future, you're sure to be well served by this official video guide from the folks at T-Mobile.

Ustream is a free web function you can use to broadcast not only streaming video, but live video as well. This tutorial shows you how you can set up your own Ustream feed and then embed it into your blog or website.

If you want to print web pages but don't want all sorts of aimless clutter then check out this video and learn how to edit those pages before you send them to the printer. With a little Firefox extension called Print Edit!, you can remove unwanted elements from the page and then just print what you need.

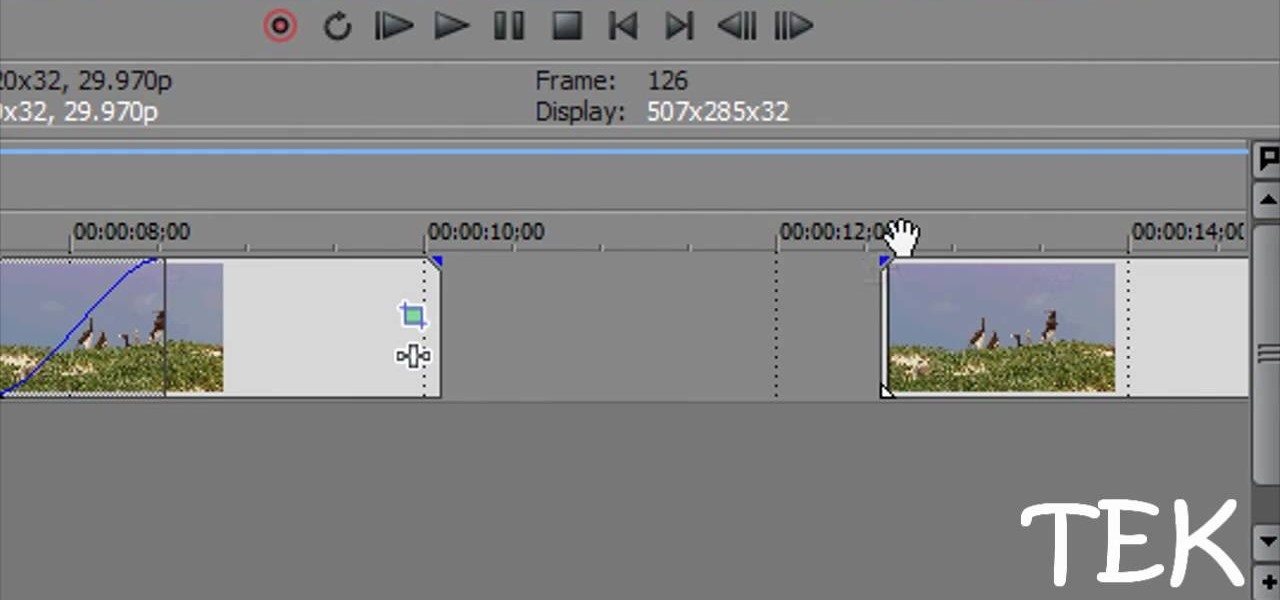
This tutorial shows you several different types of fades you can use when working with Sony Vegas. Fades can add a little something extra to your web clips, slideshows and other media, and Sony Vegas offers several ways to customize your own.

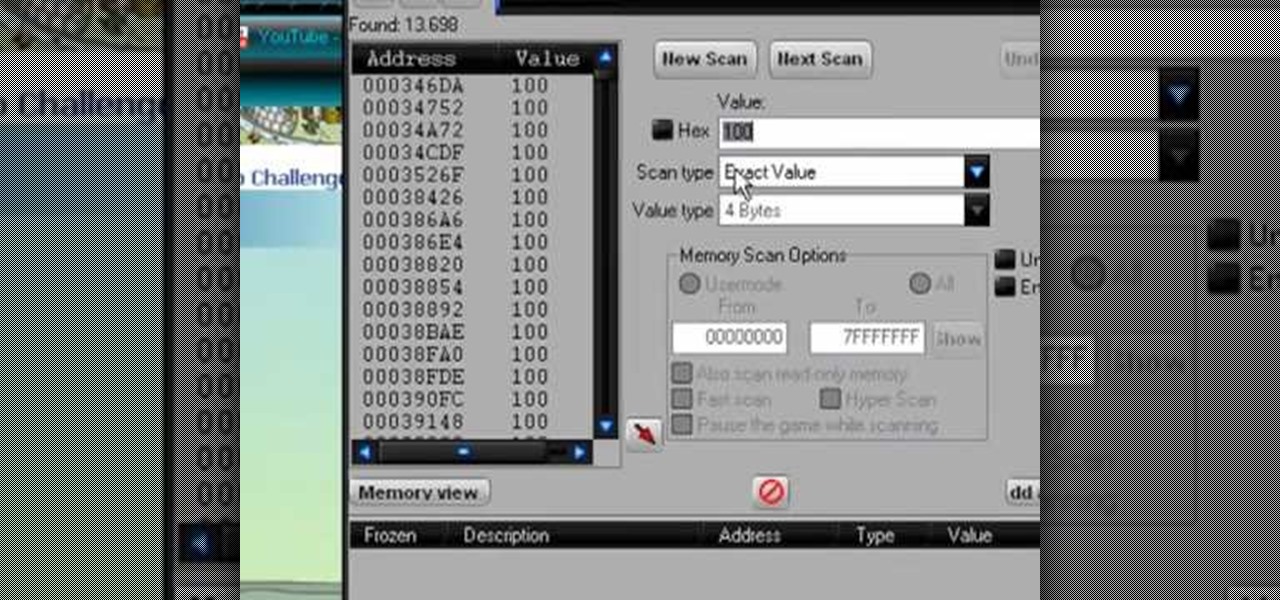
Want to give yourself an extra edge when going for the high score in the popular Facebook game Tower Stack? All you need is Cheat Engine and the Firefox web browser! This tutorial shows you how to do the rest.

We've all been there, where we're trying to find that one thing in our cache but it's just eluding us. There's an easy and free solution to this pressing issue. Just use this Firefox add-on CacheViewer to manage and navigate your cache.

He's all eyes and face, and shows up in some of the more bizarre Flash animations on the web. He's Shoop Da Woop, and this tutorial shows you how you can use the emblem editor in Call of Duty: Black Ops to turn him into your own personal mascot.

In this clip, we learn how to use voice commands to make calls, search the web and open apps on a Windows Phone 7. Whether you're the proud owner of a Microsoft Windows Phone 7 smartphone or are merely considering picking one up, you're sure to be well served by this video tutorial. For more information, including detailed instructions, take a look!

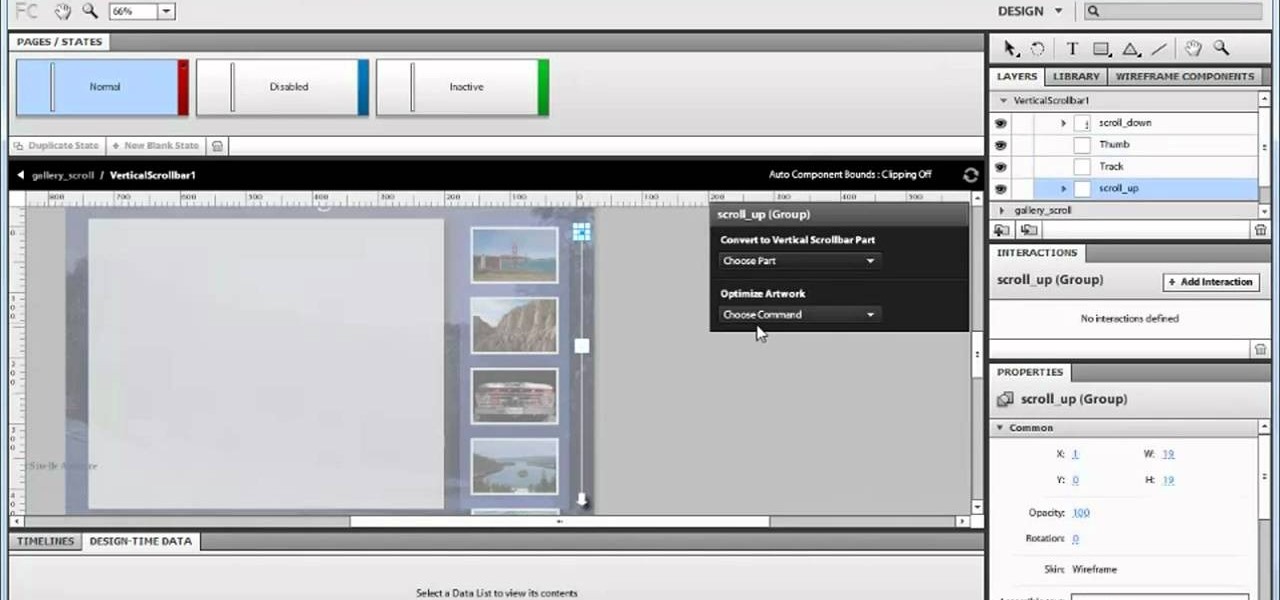
In this video tutorial, we learn how to create scroll panels within Fireworks CS5. Whether you're new to Adobe's popular bitmap and vector graphics editor (formerly known as Macromedia Fireworks) or are a seasoned web design professional simply looking to become better acquainted with the application, you're sure to benefit from this free video software tutorial. For more information, including detailed step-by-step instructions, take look.

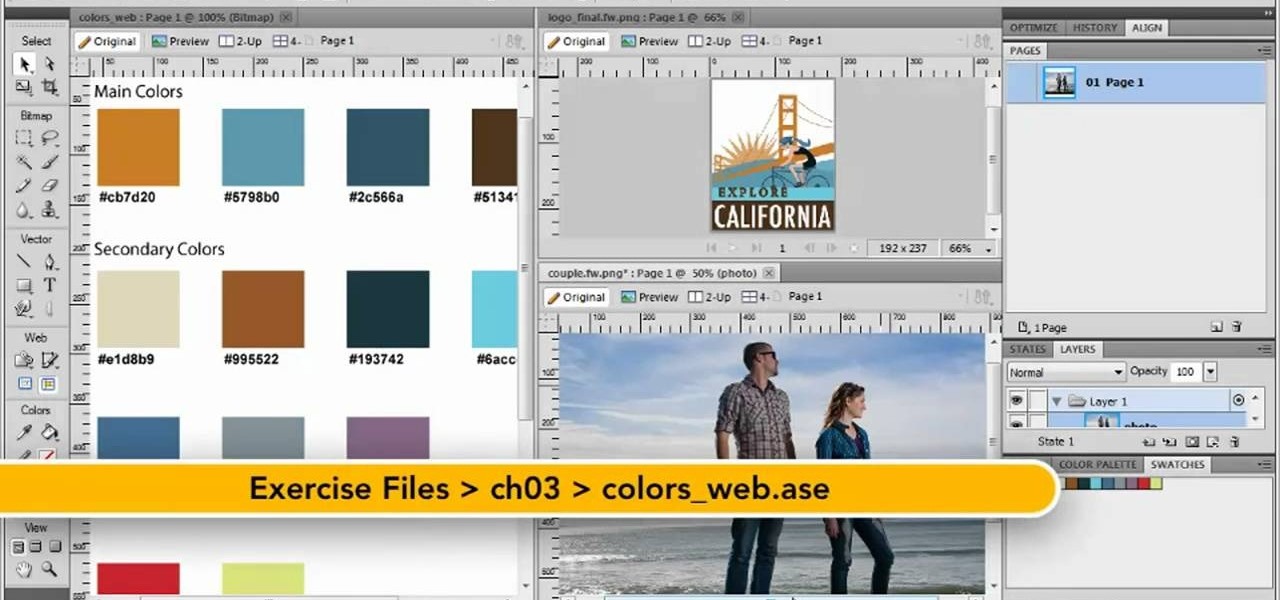
In this video tutorial, we learn how to import ASE files in Fireworks CS5 when doing prototyping work. Whether you're new to Adobe's popular bitmap and vector graphics editor (formerly known as Macromedia Fireworks) or are a seasoned web design professional simply looking to become better acquainted with the application, you're sure to benefit from this free video software tutorial. For more information, including detailed step-by-step instructions, take look.

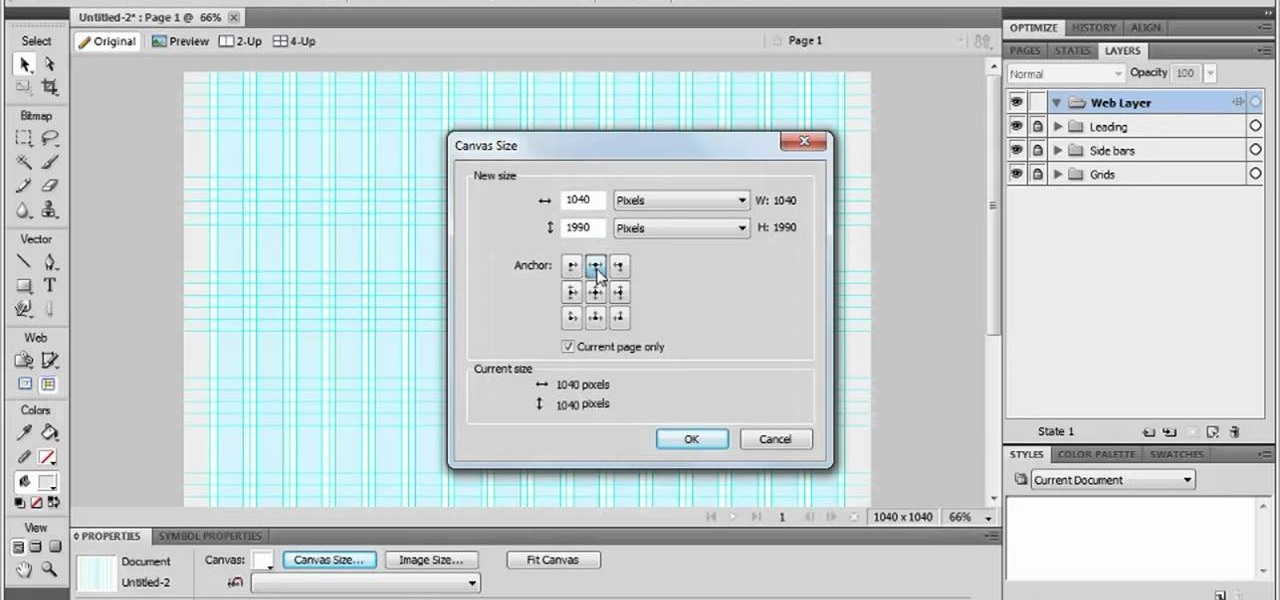
In this video tutorial, we learn how to create wireframes using doc templates in Adobe Fireworks CS5. Whether you're new to Adobe's popular bitmap and vector graphics editor (formerly known as Macromedia Fireworks) or are a seasoned web design professional simply looking to become better acquainted with the application, you're sure to benefit from this free video software tutorial. For more information, including detailed step-by-step instructions, take look.