Whether you want to build your own website for your business, start your new lucrative career in web development, or gain a wealth of projects to add to your portfolio, this course will help you do it. And right now, "The Complete Web Developer Course" is on sale for just $14.99 — a staggering 92% discount off the regular price of $199.
If you're a hacker, pentester, or any other type of Null Byte reader, and would like to create a website to showcase your services and skill set, you may not have the time or energy to do it the long way.

No website, service, or platform is immune to being abused or exploited by hackers, and Google Analytics is no exception. To better understand how Google Analytics can help deliver payloads and bypass security protocols, one might want to learn how to use Google Analytics from a user's perspective first.
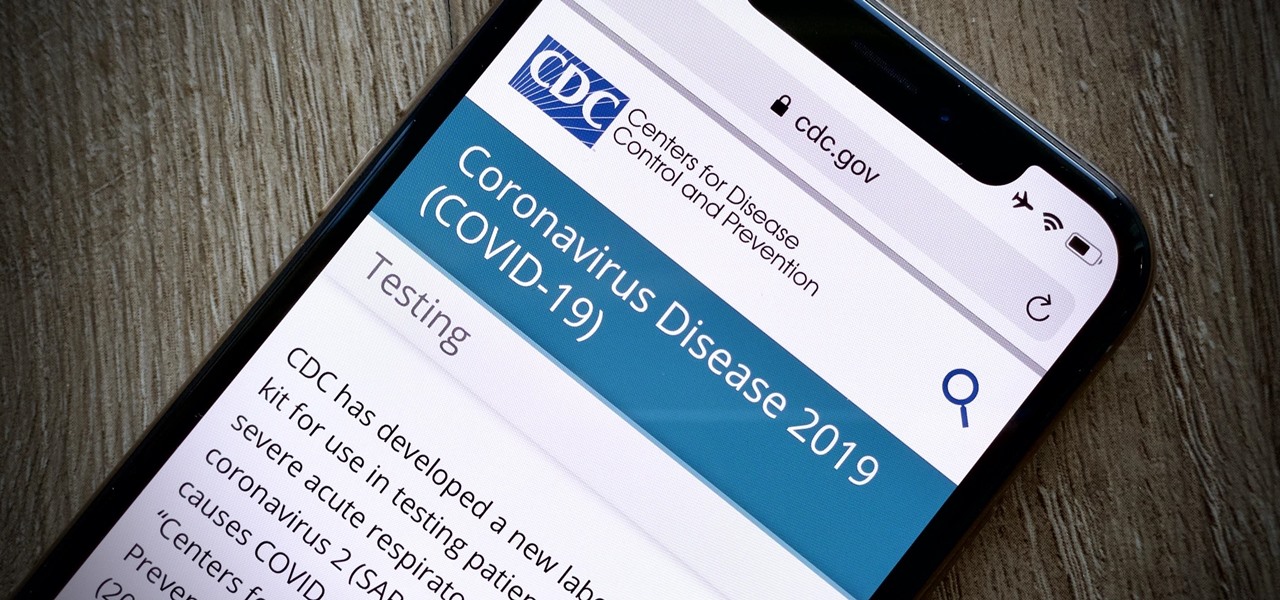
On March 13, President Trump announced during a briefing in the Rose Garden that Google was building a COVID-19 screening website to help Americans understand if they might have the new coronavirus. If likely infected, the site would also include the location of a local drive-through testing site to visit. So how can you access the screening website?

Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

While modern browsers are robust and provide a lot of functionality, they can be unlocked to do some pretty spectacular things with browser extensions. For hackers and OSINT researchers, these tools can be used to defeat online tracking, log in to SSH devices, and search the internet for clues during an investigation. These are a list of my top ten favorite browser extensions for hackers — and how to use them.

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

Before attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and found the right places to point their scope at, they'll use a web server scanning tool such as Nikto for hunting down vulnerabilities that could be potential attack vectors.

The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.

One of the headlining features in Samsung's One UI update is a new dark mode that turns stock apps and system menus black. But something you may have missed is what this theme does to the Samsung Internet app and all the websites you visit.

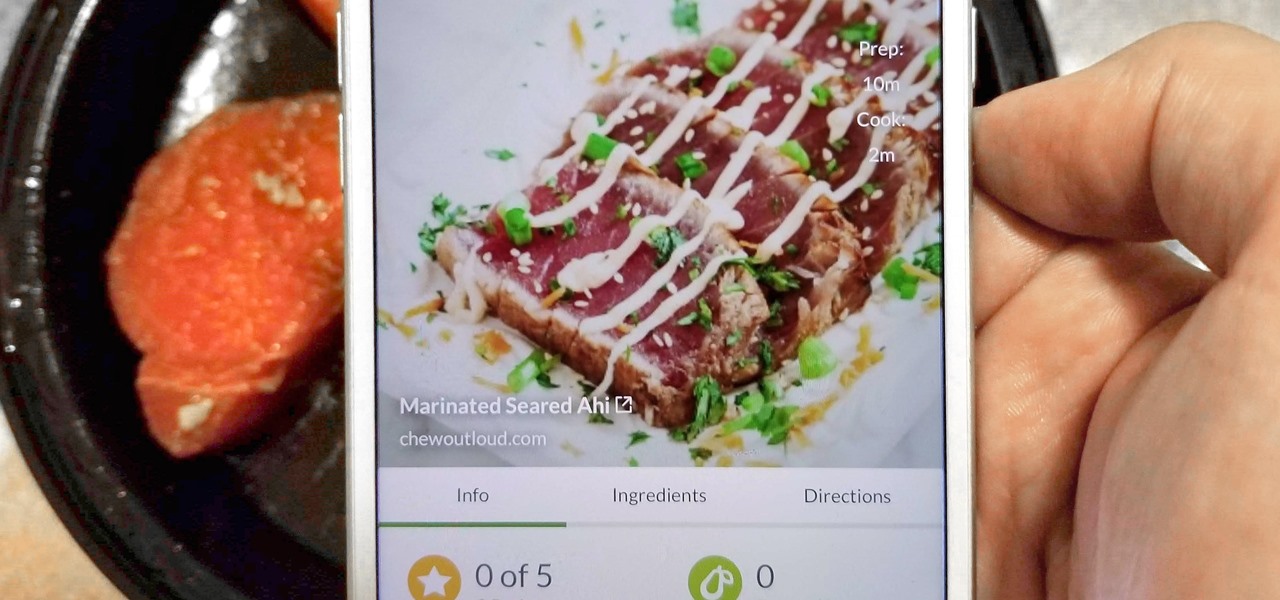
With Tasty dominating Facebook videos and online cooking flourishing, it can be cumbersome to keep track of all your recipes. Someone might send you something, and storing it in an app like Pocket is like jamming all your school papers in one folder — it just isn't practical. Fortunately, there's a better way to catalog your recipes so you can always have them on hand.

Two-factor authentication (2FA) is a great way to add another layer of security to sensitive third-party apps and websites like Venmo. However, before iOS 12, to log into a particular 2FA-secured app or site on your iPhone, you'd have to memorize or copy the SMS code from Messages, then jump back in a timely manner to log in. Apple's latest iOS version streamlines this process.

A convincing domain name is critical to the success of any phishing attack. With a single Python script, it's possible to find hundreds of available phishing domains and even identify phishing websites deployed by other hackers for purposes such as stealing user credentials.

A fairly hidden feature in iOS 10 let you turn websites and documents into PDFs, but thanks to the new Markup function in iOS 11, this process has become a lot more streamlined.

The biggest corporation we know today is called Google, I bet you've heard of it yeah? How Google Tracks You:
Have you ever used an open wifi, which after you connect displays a website to enter your credentials to get internet? That website is called captive portal and widely used in airports, hotels, universities etc. Have you ever wondered what would happen if someone would set up an open wifi with the same name displaying a very similar web page asking for credentials? Usually if there are multiple wifi networks with the same name and encryption, devices only display the one with the highest sign...

Though you can use the Social Engineering Toolkit to clone websites, this way is much more customisable.

Apple's new iOS 8 has a ton of new features, and so does their revamped Safari app, only some of the features aren't quite as obvious as others. In this guide, I'll show you my 5 favorite Safari secrets in iOS 8 for your iPad, iPhone, or iPod touch.

Welcome back, my greenhorn hackers! My preference for Linux as a hacking platform is well documented, and I have even created a series of tutorials to train new hackers. Without being proficient in Linux, you can't really call yourself a hacker.

I rarely receive spam mail, but every now and then I’ll get an email from Cat Fancy Magazine. I’ve never read an issue of Cat Fancy Magazine or been to their website. Actually, I’m allergic to cats. So how did they manage to get my information?

As you may have already heard, the worst bug in OpenSSL history went public yesterday, dubbed Heartbleed. While we can go deeper into the technical details of it later, the short version is that OpenSSL, the library used to encrypt much of the web running on Linux and Apache has been vulnerable for up to two years.

Need to clear you cache? This guide details how on any web browser (Chrome, Internet Explorer, Firefox, Opera, Safari, Internet, and Dolphin) for any platform (Windows, Mac OS X, iOS, and Android). What Is the Cache Exactly?

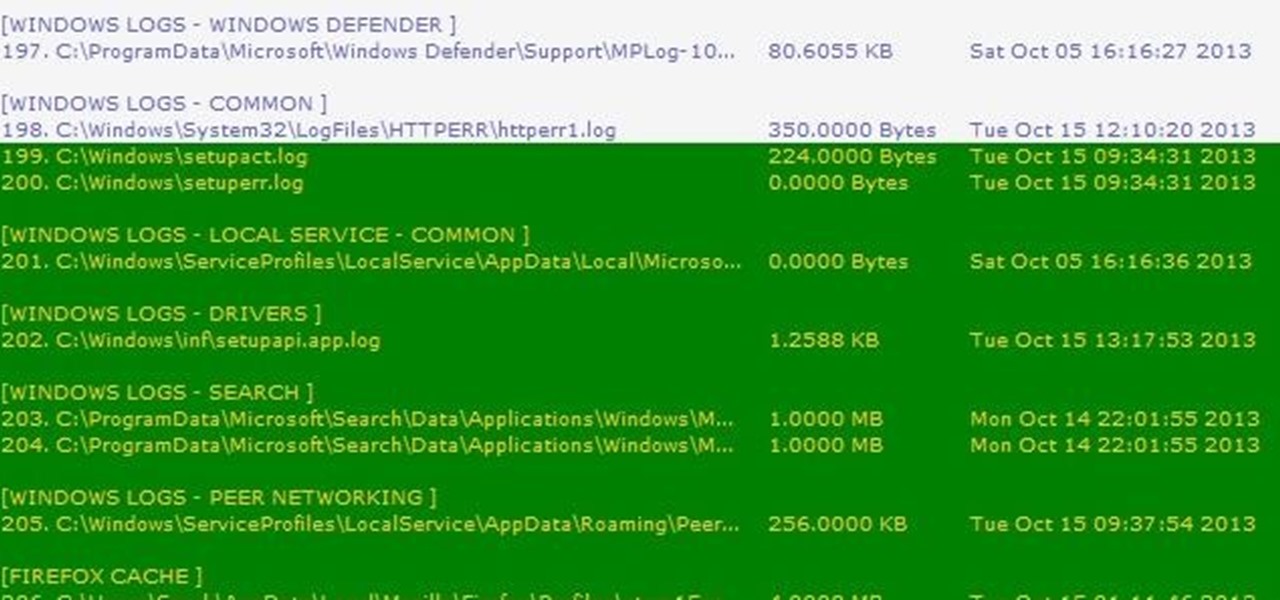
Thousands of history files, cookies, other unwanted files stored in your system as logs and other formats. To manually check each one is difficult. New computers are too fast by processor behavior, after some times of working it comes to slow performance.

We all know about PRISM. The Surveillance Program allowing the U.S Government to access private user information. Such as, Google Searches, Tweets, Facebook Posts, Private Images, and other private user data. "Hiding" yourself can be very difficult, but it is possible. I'm here to show you How to Become Anonymous & Browse the Internet Safely.

Every year, Black Friday gets a little more insane. People get up at ungodly hours, wait in lines forever, and get into some of the most ridiculous fights you've ever seen. All in the name of saving some cash. Everyone loves saving money, but without a game plan, you could end up missing all the good deals and going home with nothing. Luckily, the Internet is here to take some of the stress out of holiday shopping. With these sites and apps, you can find out about all the best deals before yo...

If you would like to use Google AdSense on your website, in order to make money from your site, you will need to get a Google account. Click "sign in" on the Google home page: www.Google.com. Next, scroll down to the bottom of the page and click on "create an account now. Fill it out. It will send you an email to verify your account. You'll need to open your email to confirm.

Tom of Videomaker teaches how to use the green screen to make a character appear in front of a set or to achieve the website spokesperson effect. Install a green screen in such a way that the fold at the corner of the wall and the ground is instead curved in order to create an even transition from the top to the bottom of the green screen. Build the base at the bottom part of the screen by weighing down the fabric at the corners and stretch it evenly. Light the green screen separately from th...

Want to forget about always pulling out your credit card to purchase something on your BlackBerry? There's a little application that can do it all for you? But how? Best Buy has answers. The Best Buy Mobile team explains how to use the BlackBerry Wallet application. This application can store personal information such as credit card information and shipping addresses on a secure website for easy access when shopping online.

1. Type in WWW.sendthisfile.com in the web toolbar and press enter 2. Click on Register found on the top right side

First of all create a website. Go to 'file' and then click 'new'. Choose it as ‘general’ and then as 'empty'. Name this as 'practice site'. Click 'ok'. Now create your first webpage. Click on 'general', 'html' and then 'ok'. Now click on the 'file ' and then choose 'ccs' to create an external style website. This is basically a text file given a '.css' extension. Now click 'ok'. Now go back to your 'html' page and then 'save' it. Now you have to type in 'index' to replace 'default', and th...

Ownspy is powerful program which can be used to backup your iPhone remotely. This program can be used in both good and bad ways. If you have children you can keep track of them by installing this program on the phone. This regularly uploads the content from the phone to the website. So in this way you can know in what way the phone is being used. Also this can be used by a jealous boy friend to spy on his girl friend. This programs tracks your location, backs up your messages, pictures. It al...

Whatever your reasons for doing it, if you are trying to hack passwords, it helps to have the right software for getting the job done. With the Cain and Abel program, you will be well on your way to hacking even the toughest personal passwords.

This video describes how to insert keywords and SEO with the fusion essentials in the website. He asks you to first go to the site mode and then click on the home page and from there you can get in to the property box. There you can find three choices or tabs. He explains that the first one can be used to change the page name and page title and also can adjust the master border. The second tab is used to mention the page status, if it is done and can be displayed to the viewers or if it shoul...

In this video from PCRescueRepair we learn how to record streaming audio from any website using audacity. To get audacity just go to google, type in audacity, click on the link for audacity, and download audacity to install this on your computer. Also you need the LAME mp3 encoder which is on the audacity website. Now he takes you through the steps to do this task. Go into audacity and from the drop down change to stereo mix from microphone. On output adjust to max. and on input adjust the vo...

In this video the author gives an HTML Website Design tutorial showing how to make a side menu bar. He goes on to show how to write the HTML page, explaining about the different HTML tags like <html>, <head>, <title>, <table> etc., He shows how to set page color and add styling to the page. He shows how to align the page elements and does the font settings. He goes on and makes a HTML table. Next he shows how to make a menu bar using the table element and shows how to do the various settings ...

Orianna is a unique champion that focuses her abilities on the use of a ball she carries with her. The ball allows you to pull off some pretty cool tricks, including slowing your opponents in an AOE around it and harassing with it during the laning phase.

The League of Legends champion Kayle, or Judicator, received a rework a while back and now plays slightly differently because of that. Take a look at this champion spotlight guide by Riot Games on how to build Kayle as a hybrid support champion using the right runes and masteries. Be sure to take advantage of her ult so that you can save someone at the right time with invincibility!

Having cool photos as your desktop can make your computer a welcome sight, but having to find a fresh one every so often can get pretty stale fast. Thankfully, freeware utility Flickr Wallpaper Rotator for Windows PC's can import images for your desktop from Flickr automatically at intervals you set. You can even set it to use photos from a Flickr search or show favorites from a specific user.

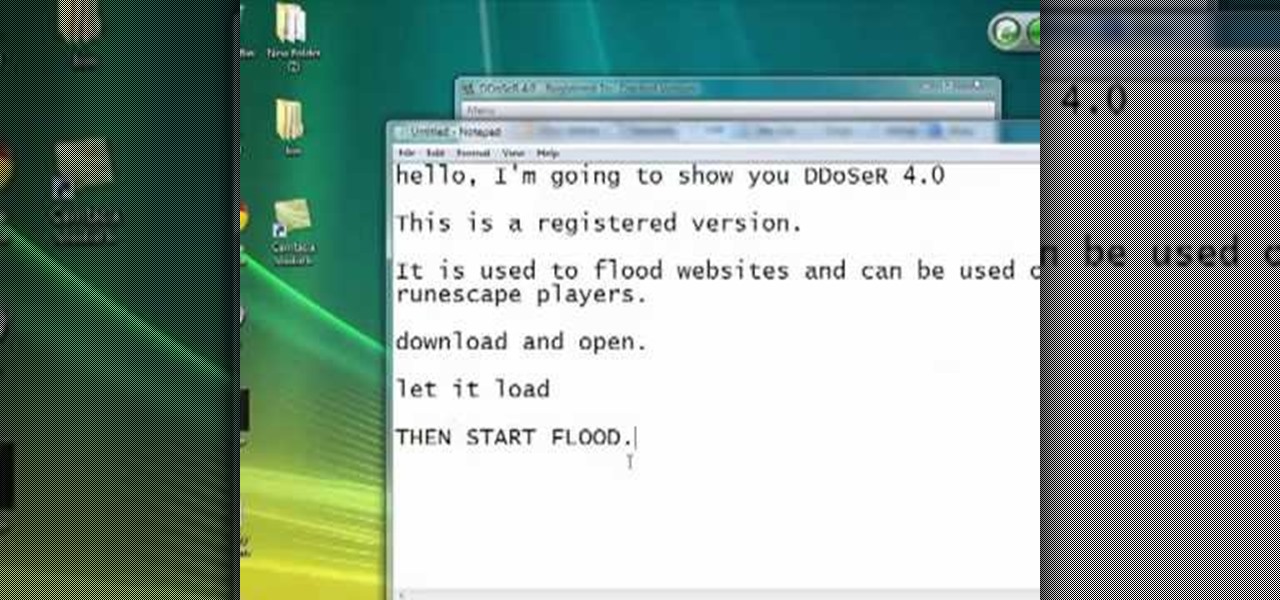
Interested in flooding a Runescape player's website? Watch this video to learn how to download, install, and use DDoseR. Flood any Runescape player with this ddos. Using DDoSeR on your Runescape opponent will freeze them, giving you a huge advantage.

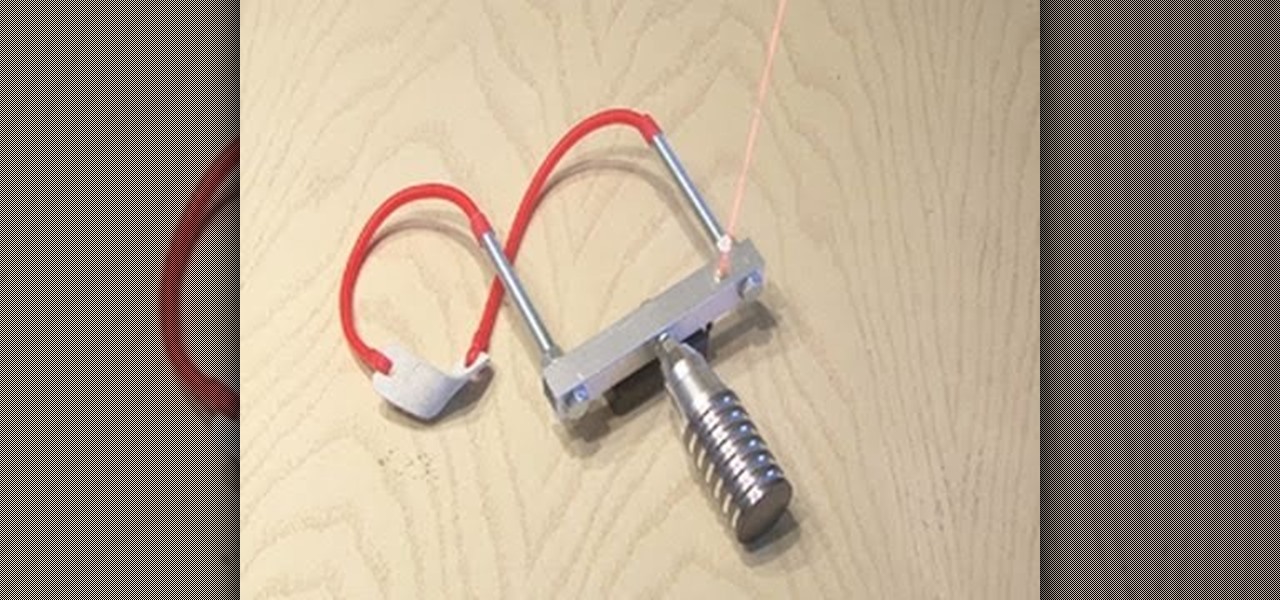
In today's day of mobile devices and improved technology, anything of yesterday can be considered retro— even a freakin' slingshot! Yes, that's right— forget fallen down tree branches. A rubber band and tree limb ain't going to cut it anymore. These days, kids need accuracy, and Kipkay has the knowhow.