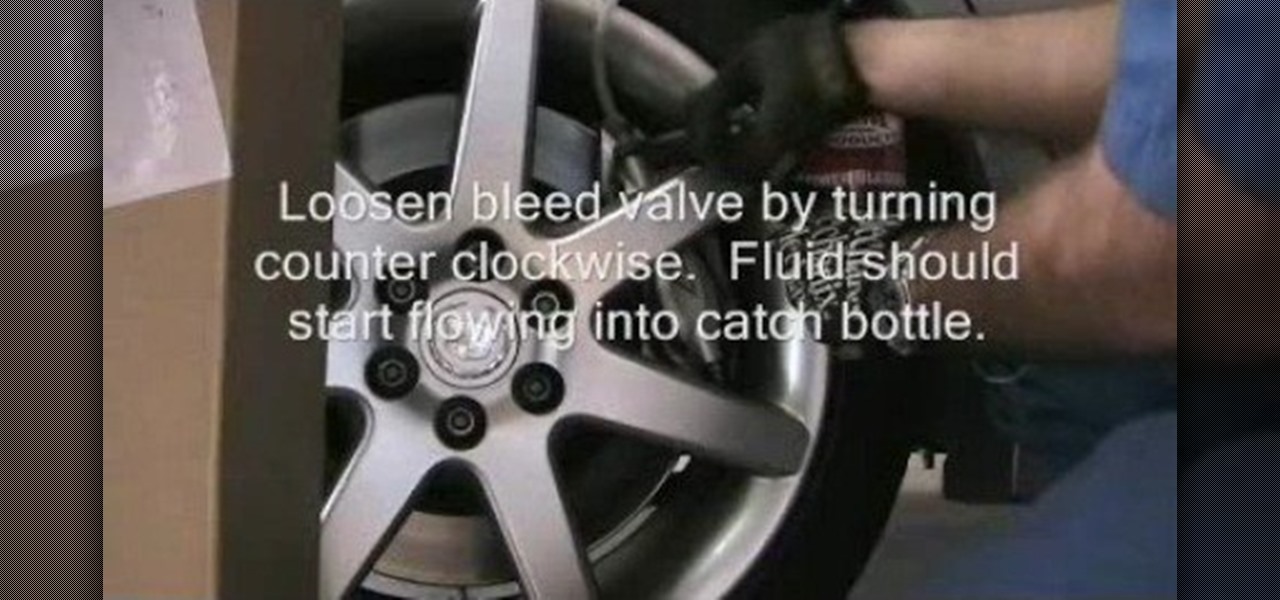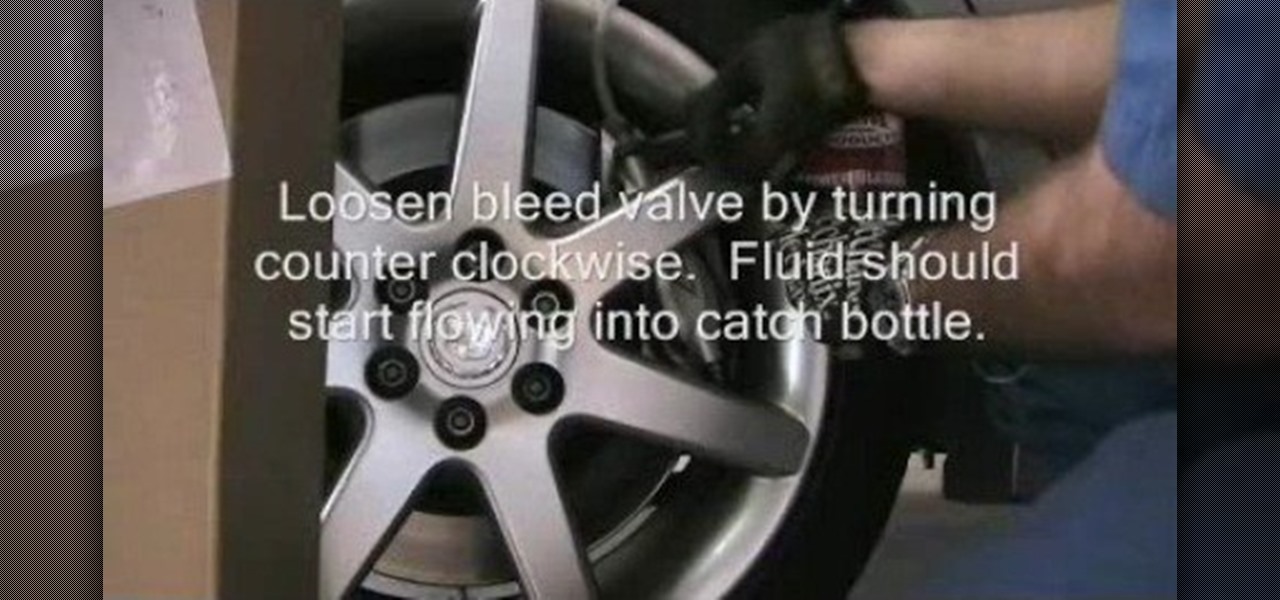
In this tutorial, we learn how to powerbleed your brakes. First, test for any leaks and then release the pressure so you can fill the bleeder tank with fluid. After this, you will screw the pump on and then start to pump pressure to approximately 15 psi or check your service manual for recommended pressure. As the pressure builds, you will see fluid traveling through the tube to the brake reservoir. Use a bottle to catch the fluid that is bleeding through the system. When you bleed your brake...

If you're working on a LLV postal truck, this video will show you how to determine if you've got a bad fuel pump or not. It's a quick diagnosis trick to determining if there's an electrical problem with the fuel pump, and first you need to take out the ECMB fuse, plug a jumper wire where it was, use a multimeter and labscope to see what's going on. The United States Postal Service (USPS) uses these trucks for all their postal deliveries, and if you're the mechanic working on it, this and the ...

The control arm on a Grumman Long Life Vehicle, or LLV, postal truck (used by the United States Postal Service (USPS)) is exactly the same as the control arm on the Chevrolet S-10 pickup truck, so the replacement procedure is almost identical. This video will show you that procedure, but it's important that you get the right part for the side you're replacing. The LLV is right-side steering, so the driver's side is the passenger's side on the S-10. It's a little confusing, so be careful.

The truck in this video was having a misfire problem during routine service. This video for mechanics will show how to find the problem of this misfire. The first thing to look at is the lab scope. After that, comes time for the smoke machine test to identify a possible cylinder compression leak. Watch and learn. This is very similar for a lot of different automobiles.
YouTube is a great video service because it's free and has invaded the world… meaning, practically everybody has been on YouTube at one point or another. Another great aspect of YouTube is the ability to embed content on your website or blog… like your WordPress blog. You can also embed full YouTube playlists. This video will show you the steps to embedding YouTube playlists on your WordPress blog, and the principles can be applied for other sites as well.

It is never a good sign when the 'check engine' light comes up on your dashboard. In this tutorial, learn how to reset the light if it is not functioning properly. If you have already fixed the engine issue and wish to reset the warning light on your Saturn S-Series, this video will show you how quick and easy it is to do so.

This video tutorial from iWalous shows how to install Bossprefs on your jailbroken iPhone from Cydia.

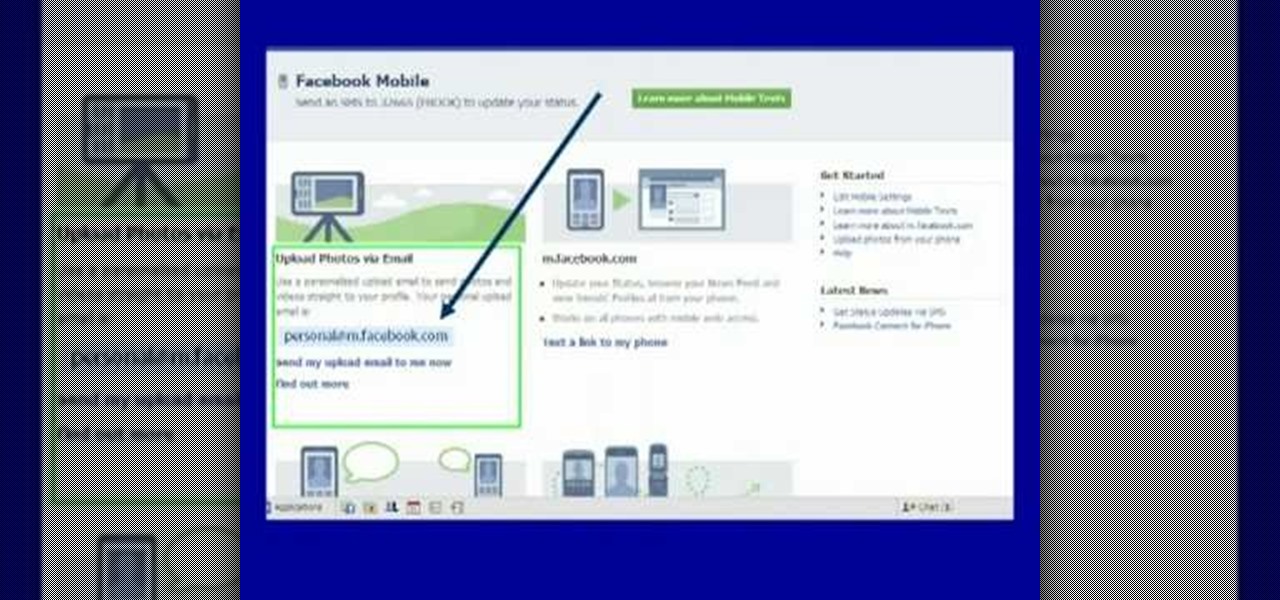
Moniquewade will show you how to upload photos and videos to Facebook by using email. The user has seven steps for you to follow in order to upload photos and videos to Facebook using email services very fast and easy. The first step starts out by telling you to go to Facebook.com. By following each of the seven steps that are provided, you should be able to send different types of photos and videos to your Facebook account just by using email.

In this video tutorial, you'll learn how to change a damaged belt or brushbar on the Vax V-026 Rapide Deluxe carpet washer.

In this video tutorial, you'll learn how to change a damaged belt/brushbar on the V-006 Turboforce vacuum cleaner

If you are interested in spa facial services, learn how an oxygen facial can make your skin softer and remove impurities with this free skin care video series.

In this first clip, Chef John shows the basic restaurant technique for poaching eggs. Due to the high-volume of a brunch service, it is almost impossible to poach eggs “to order.” They are poached ahead of time and held in cold water until final plating, when they are re-heated in simmering water for a few minutes. This method also works great at home for smaller batches as you’ll see. Once you’ve poached your eggs and have them in cold water you are free to set up the rest of the plate

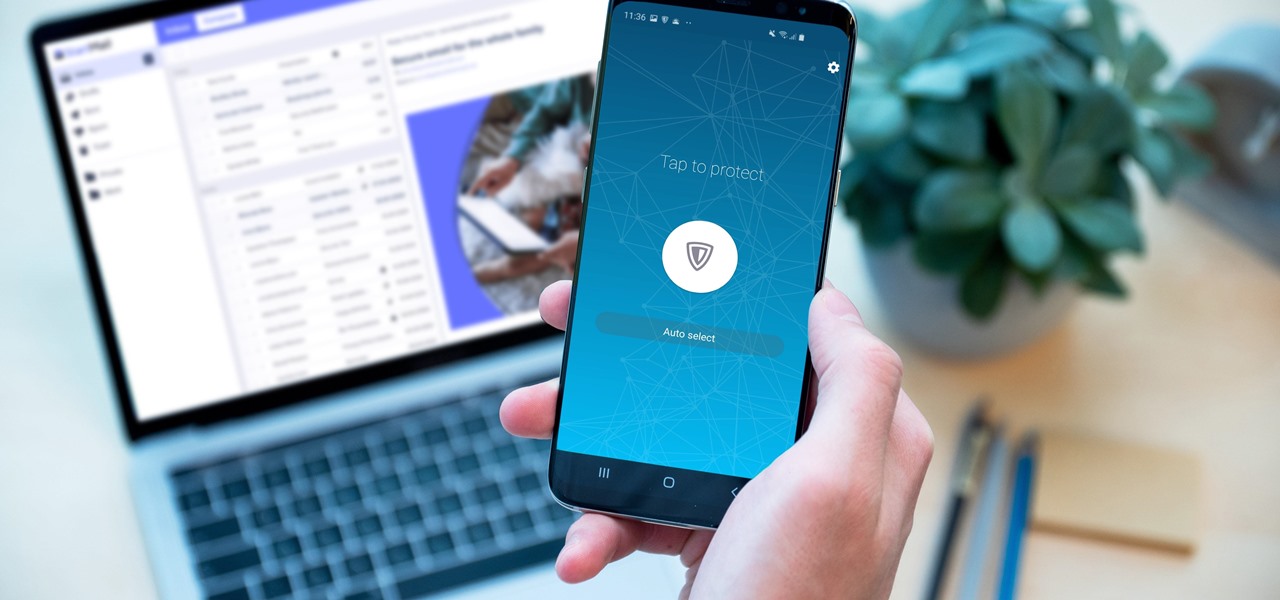
Your sensitive personal data should be strongly protected, and it's never more vulnerable than when you are online. The internet connection is a prime avenue of exposure, and email is one of the least secure forms of communication. Fortunately, there is an easy solution to both of those problems.

Twelve years ago Google launched its Cloud Platform, and the world has never been the same. This suite of cloud computing services has changed how modern businesses operate. Whether you use it for data storage, management tools, computing, or machine learning, the Google Cloud Platform is essential.

It's not hard to let the new SARS-CoV-2 strain of coronavirus put pressure on our minds. Fear of catching COVID-19 is never far from the topic of conversation. But it doesn't have to be that way. If you're struggling with anxiety, stress, depression, or any negative emotions due to the virus's effect on our lives right now, you might find some solace in meditation.

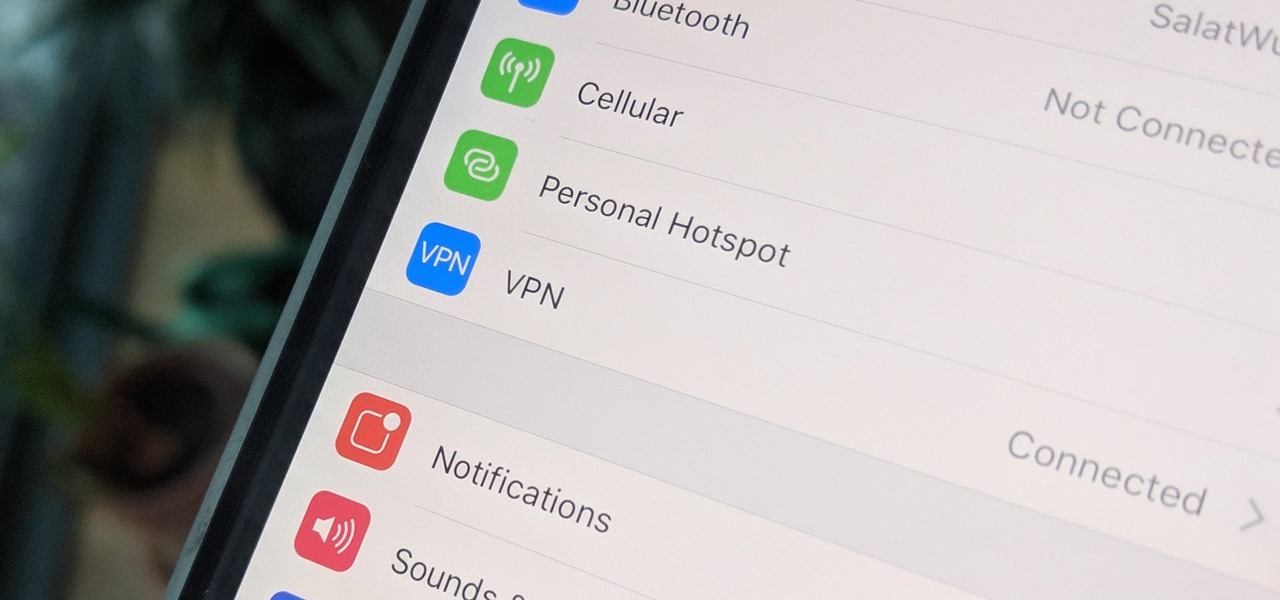
A virtual private network is a necessary part of your arsenal if you're insistent on surfing the web privately and securely on your iPhone. The App Store is littered with hundreds of different VPN services that encrypt traffic and mask your IP address, but what they all have in common are connectivity issues.

Google's push for your safety gained some much-needed attention when it released the Pixel 4 smartphone. It has an app called "Personal Safety," which uses the array of built-in sensors on your phone to detect if you've been in a car crash. The futuristic safety feature was exclusive to the Pixel 4 initially but is now available to all Pixel owners as well.

In November 2016, the RCS Universal Profile (Rich Communications Services) was introduced. The technology takes text messaging to the 21st century, emulating many of the features found in IM apps like WhatsApp and iMessage, but working through your phone number like regular SMS or MMS. The only thing is, your carrier needs to support RCS-UP to use the feature. Thankfully, the list is growing.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

There once was a time before smartphones when you had to actually remember where you parked your vehicle. This really sucked when visiting a location with a large parking lot — they even made a whole Seinfeld episode about it. But now you can just tap a button to solve this problem. Who says we're not living in the future?

After reviewing the international plans for major US wireless carriers, it became obvious they're all pretty bad. Your data is heavily restricted, requiring a daily fee which can cost an extra $100+ on a seven-day vacation. That's when I learned about Google Fi, and how for most travelers, it's the best option.

There have been concerns with how much personal information Google tracks and all the things they know about us. Of course, that's what makes Google services so useful, they can use that information to cater to each of us individually. So yes, it serves a purpose, but it's not great for personal data security.

Whether it's for health reasons or just to look better, many of us want to get in shape. It's a long process that starts with nutrition, and dieting is never easy. Fortunately, there are some great food-tracking apps that will make it a lot easier to become a healthier version of yourself.

On Monday, with just days left before Christmas, Lowe's dropped a surprise augmented reality treat in everyone's lap: a brand new Magic Leap One app.

When you can't reach your iPhone or don't have it on you, how do you get help from emergency services? Unless you have one of those life-alert mobile triggers, someone nearby, or some amazing telepathy skills, hope might be the only answer — unless you wear an Apple Watch, that is.

Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

When you don't want somebody you're calling to know the real phone number associated with your iPhone, whether it's for privacy reasons, to avoid being called back, or to prevent being ignored, there are multiple things you can do to block it on their caller ID.

With the Super Bowl just days away, it seems appropriate to draw parallels between football and the professional sport of technology business, or, more specifically, the augmented reality segment.

Nmap is possibly the most widely used security scanner of its kind, in part because of its appearances in films such as The Matrix Reloaded and Live Free or Die Hard. Still, most of Nmap's best features are under-appreciated by hackers and pentesters, one of which will improve one's abilities to quickly identify exploits and vulnerabilities when scanning servers.

Threats to your privacy and security are everywhere, so protecting your data should be the highest priority for anyone with a smartphone. However, one threat many people overlook is the company who supplies the operating system your Android phone runs — Google.

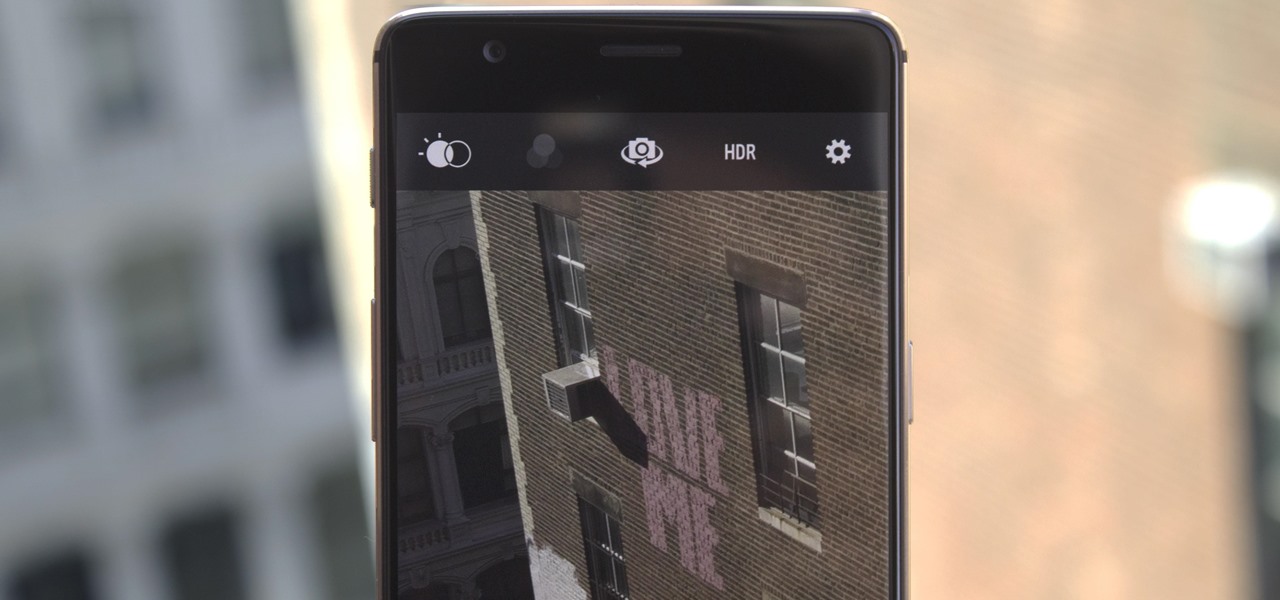
Despite packing some really nice camera specs, the OnePlus 3 and 3T don't take the best pictures. That's because, these days, great software is just as important as great hardware when it comes to image quality.

Uber's year is going from bad to worse, and they may be subject to a potential criminal probe in the ongoing Waymo legal battle.

Google is on a mission to bring a better messaging experience to Android users. We've seen them try and fail over the years with various messenger apps, but this time, they're taking a different approach by working with industry leaders to create a new messaging standard. The result is RCS Universal Profile, or simply Chat, and it's finally catching on.

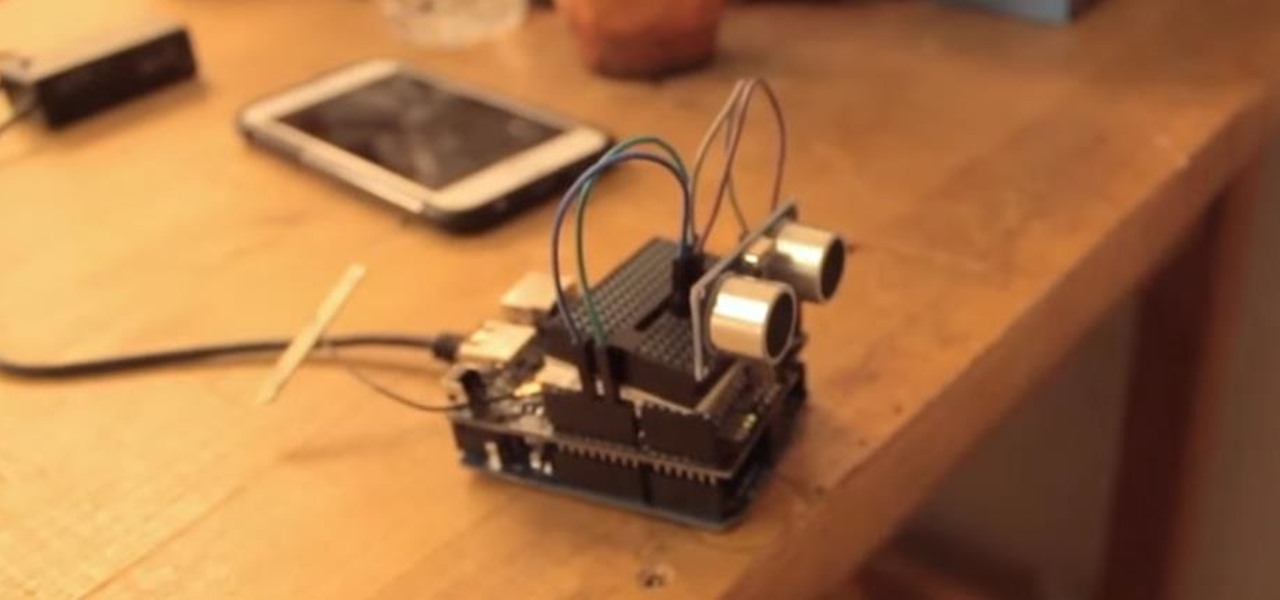
This tutorial shows you how to create an intruder alarm that sends you text message alerts when motion is detected. This may sound complicated but I am pretty confident any beginner with electronics should be able to do this just fine. The range sensor senses motion and tells your Arduino board to send the text (SMS). So you can leave the intruder detector at home, connected to your network, and still receive the SMS alerts, no matter where you are, as long as you have cell phone service.

Hello World ! Well, welcome in my post. This will be in series, and this is first part. Throughout the series, I will share my research and findings with you. And that will be on topic, Encryption Is Not Enough. We will see, how Encryption is broken & what countermeasures should be implemented to secure it. Let's begin, Why do we encrypt ?

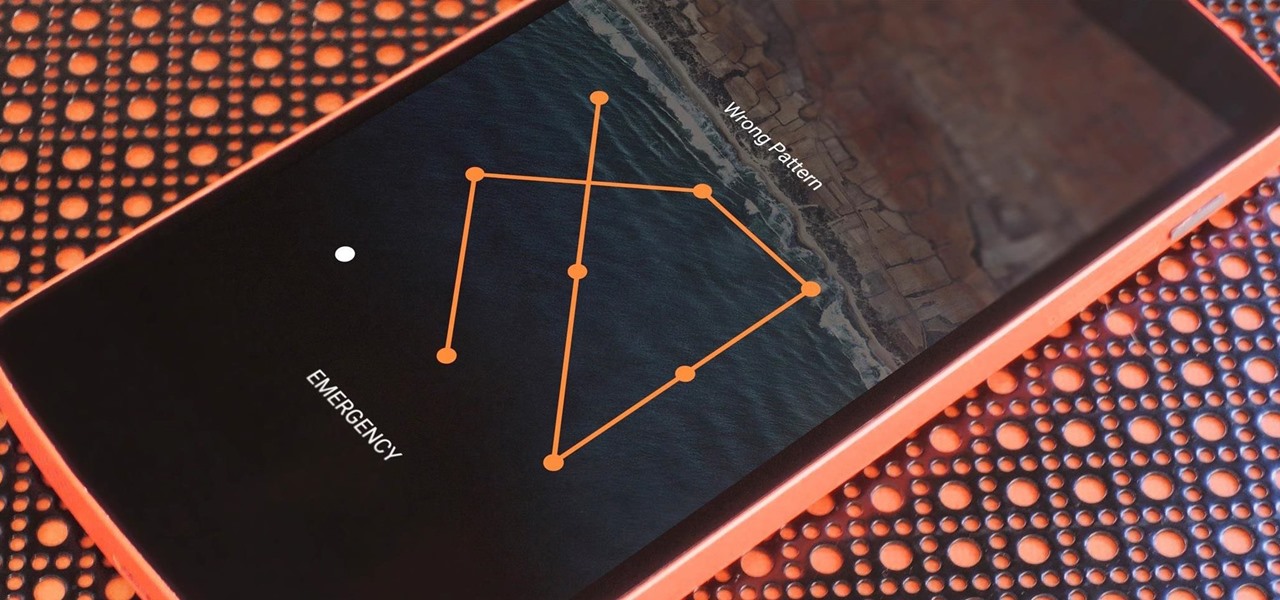
If you somehow forgot the pattern, PIN, or password that locks your Android device, you might think you're out of luck and are destined to be locked out forever. These security methods are hard to crack by design, but in many cases, it's not entirely impossible to break into a locked device.

If Netflix's $9.99/month has deterred you from signing up for its streaming service, you're probably looking for cheaper alternatives to stream movies and TV shows, like Crackle (free with ads) or Hulu ($7.99/month with some ads). And now there's a new option for you when it comes to movies—Paramount Vault.
Welcome back Hackers\Newbies!

Welcome learners, lets us proceed further with the information we already have. In this post we will explore more about finding hacked accounts online. We will look into how to find juicy info in pastes which are deleted on Pastebin.

So you finally decided to make the switch from iOS to Android, huh? Well first off: welcome to the world of tomorrow. And secondly: good call, mate.