How To: Add 3D objects to your videos
Software needed: Voodoo motion tracker, virtual dub and blender

Software needed: Voodoo motion tracker, virtual dub and blender
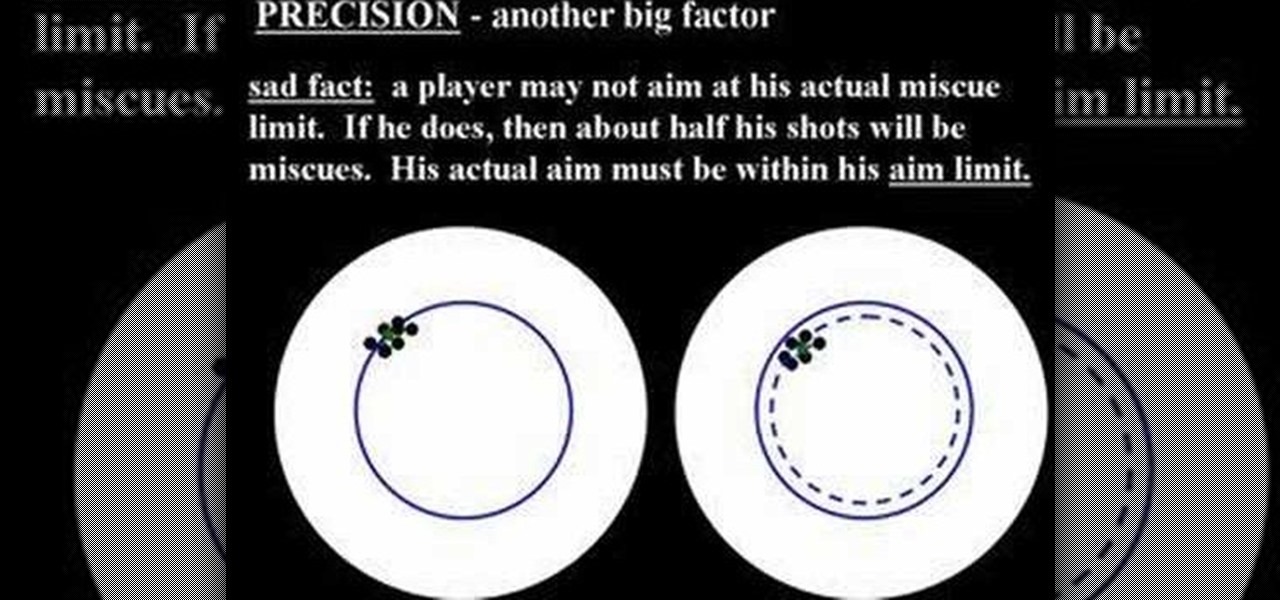
Cue ball draw refers to the way a cue ball strikes a rack of balls. In particular, if the cue ball is hit low on the ball, when it strikes a rack of balls, for the break, it will have enough backspin to wind its way back to the shooter.

Almost 125 million people worldwide suffer from what is known as psoriasis, the skin disease that's marked by red, itchy, and scaly patches that are hurtful, if not visually god-awful. There can be a little hope though for psoriasis sufferers. Though you can treat and control psoriasis, characterized by dry scaly patches of skin, the progress is often erratic and cyclical, so be patient and consistent in executing these steps.

Levi Meeuwenberg demonstrates how to do a parkour roll. First, practice the takeoff leap. Use forward momentum to jump out. Enter the landing leaning forward with the weight in front of your feat so you fall into the roll. Be physically and mentally tense and prepared when coming into the landing. Land with your feet parallel and square in the direction where you're heading. Keep your feet a bit less than shoulder width apart. Use a bend at the hips to complete the shoulder roll. Push against...

This video describes how to prepare for and execute painting your home. To begin, you should power wash your house to remove any dirt, dust, cobwebs, etc. These would prevent the paint from setting properly, unless it was new wood. If it is new wood, you should put on a beige coat first. However you begin, you should let either method dry before moving to the next step. After it dries, you should apply a weatherproof and paint-over caulk to the cracks to keep out moisture and insects. After t...
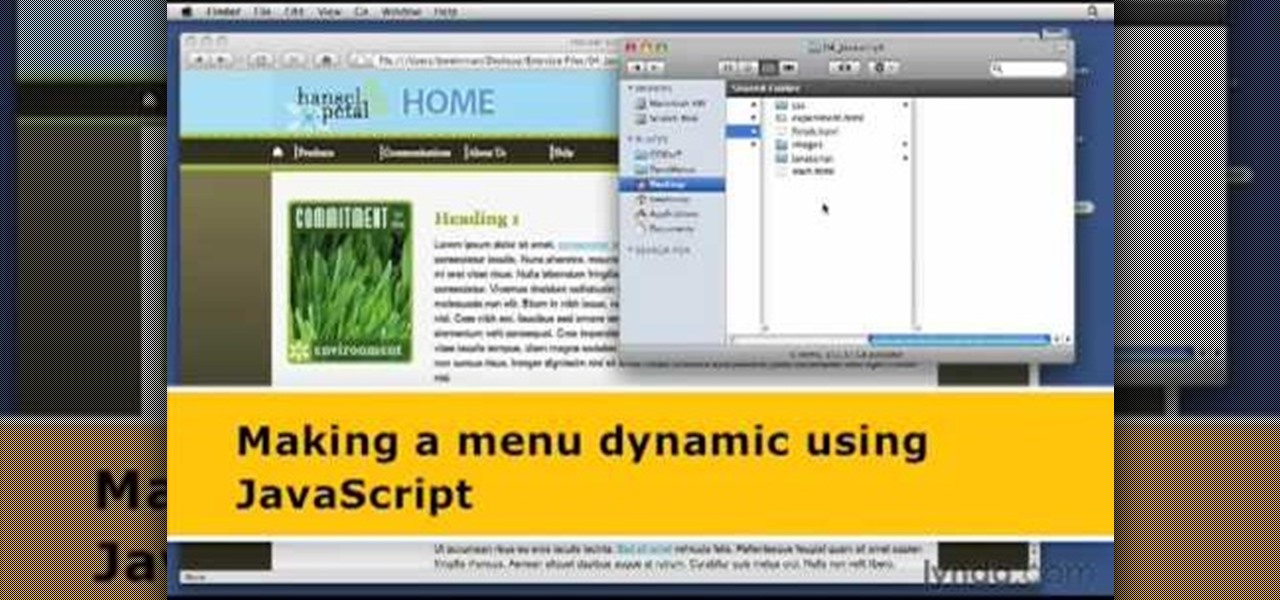
1. The following steps describes how to Create dynamic menus with html and Javascript. 2. Open the html file in Illustrator. 3. Enter the Menu.js file with <Script> Tag. 4. Create a Bulleted List of the Menus and Its Sub Menus inside a DIV Tag. 5. For Each UI List Create a Mouse over and mouse out Event for Header Menus. 6. For Mouse over Event call a Function named set Menu with MenuSubOne id as parameters 7. For Mouse out Event call a Function named named clearMenu with MenuSubOne id as par...

Show off your magic skills with a little preparation and an easy trick to execute. You Will Need

How to hack Pet Society! Pet Society cheats, tricks, hacks. Watch this video tutorial to learn how to hack gold in Pet Society (09/29/09).

This game goes by a bunch of names: "fast and loose," "pricking the garter," "the endless chain," "the strap..." The object is simple: a chain is laid in a figure-eight configuration. One of the holes is the true center of the chain and will hold "fast," while the other will not hold, and is instead "loose". Follow along with this how-to video and learn how to perform the bar trick.

It's Magic 101. Can you mimic the master? This magic how-to video will show you the trick. Effect: Taking two matches from different matchbooks (one black, one brown), you cause them to visibly switch places...right under their eyes. It's demonic; it's the Quicksilver Matches.

Learn in this video how to use XMLSpy to create and edit XQuery documents, debug them and profile execution speed and bottlenecks, and execute them against local XML data or XML stored on a database server. XML editing can't get easier then this.

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

If you have a great idea for a TikTok, you probably need to take your time to execute it perfectly. But what if something crazy and unexpected is happening in front of you, perfect for an impromptu video? You don't want to miss the action, but getting all the way to TikTok's camera might take too long — that is, if you don't know this trick.
Alright, since I notcied this article was too advanced for some users, ive decided to revision this!

Congratulations to Brian Brushwood and Scam School for winning the 2008 WonderHowTo Magic Award! We're huge fans of the Scam School and with the votes, clearly you are too. Scam School and the Superhero Trick are the brainchild of spiky-haired magician Brian Brushwood. Brian is the only WonderHowTo Award winner with a self-produced action figure!

This video is very clever, if a bit Rube Goldberg. It is the kind of thing that would be entirely charming if executed by an 8 year old boy.

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

An attacker can repurpose public MyBB forums to act as command-and-control servers. It only takes a few lines of code to configure a MacBook to fetch commands and send responses to any website the attacker desires.

Selling alt-coins like Stellar (XLM) or Ripple (XRP) in exchange for more widespread coins like Ethereum (ETH) or Bitcoin (BTC) can be a daunting task if you're new to cryptocurrency. Though you'll still need to do your research to avoid potential disasters, Binance takes the hassle out of trading digital currencies on your smartphone.

Using Bitcoin (BTC) or Ethereum (ETH) to buy alt-coins like TRON (TRX), Stellar (XLM), or Ripple (XRP) can seem intimidating if you're new to cryptocurrency. Though you'll still need to do your research to avoid potential disasters, Binance takes the hassle out of trading digital currencies on your smartphone.

Recently, I ran across SecGen, a project which allows a user to create random vulnerable machines. I absolutely love vulnerable machines, since a vulnerable VM is a safe and legal way to practice hacking tactics, test out new tools, and exercise your puzzle-solving skills.

PowerShell Empire is a post-exploitation framework for computers and servers running Microsoft Windows, Windows Server operating systems, or both. In these tutorials, we will be exploring everything from how to install Powershell Empire to how to snoop around a target's computer without the antivirus software knowing about it. If we are lucky, we might even be able to obtain domain administrator credentials and own the whole network.

INTRODUCTION Hello dear null_byters here we go again with our third part of this serie.

Hello all! In this tutorial, I'd like to show you one way of getting root on OS X. Check out this GitHub page for a recent privilege escalation exploit that was recently discovered. I've tested it and it works on both OS X 10.9 Mavericks and OS X 10.10 Yosemite, but appears to have been patched with OS X 10.11 El Capitan. If you check out the file main.m you can see where most of the magic is happening. This source code can very easily be changed to make it do more than just the system("/bin/...

Steampunk is a tremendously interesting phenomenon because of its reliance on science fiction, and fiction in general. Steampunk can arguably be broken down into two categories: the fiction, and the aesthetic. Sometimes these categories cross over, but they're often more distinct than most people suspect; that said, the aesthetic is firmly based in works of fiction.

At first, it seemed like a clever art installation housed on the web, but now we're not so sure... the Newstweek hack may indeed be legit.

While Toyota ranks as the leading automotive brand in the world, the company is a follower when it comes to augmented reality.

Locating and abusing files containing unsafe permissions is an easy and surefire way to elevate shell privileges on a backdoored macOS device. This time around, we'll be more aggressive and attempt to phish a user's login password by prompting a convincing popup message merely asking the target for their password.

It's tough to keep pace with Apple lately. As expected, only one day after the public release of iOS 11.2.5, the company released iOS 11.3 to developers. A day after that, Apple pushed it out to public beta testers, too. With new Animoji, more transparent battery information, Apple Music receiving music videos, and more, this update is the one to watch out for.

The one thing that separates a script kiddy from a legitimate hacker or security professional is the ability to program. Script kiddies use other people's tools, while hackers and security pros write their own tools. To that end, we're going to see how a stack overflow vulnerability allows us to flood a variable with enough input to overwrite the instruction pointer with our own commands.

Zently — the mobile app for renters — is taking on Venmo with its newest feature. Traditionally used to automate rent payments, deliver rent checks for free, and communicate with your landlord, it now allows you to connect to your bank account and split bills with housemates. Following the addition of Zelle to several major banks apps — to allow users to transfer money to their contacts — the battle of the mobile payment apps is getting increasingly fierce. With this new update, Zently is als...
After 6 years of development, the big banks seem to be ready to combat Venmo on the money sending frontier, but now it might be too late.

Metasploit is an extremely popular pentesting tool capable of enumeration, exploitation, and injecting shell code, and is a part of almost every hacking toolkit. So there's no way I could leave this out of our series on getting your Mac set up for hacking.

Traditional root ad-blockers like AdAway and AdBlock Plus have no effect on YouTube anymore. Until now, if you wanted to get rid of the commercials that play before your favorite videos, there have only been two ways—either by paying for a YouTube Red subscription, or by using an Xposed module to modify the YouTube app itself and force it into not showing ads.

This is my first article on here, it's based off of a project that I'm working on at school which is on three ways to bypass windows user password's. If all goes as planned and you all would like I'll work on part two and part three and post them as soon as I can. I do have to give credit to Puppy Monkey Baby and The Defalt, both of whom are my classmates at college and have helped me with writing this article.

Although there has been much speculation about how much damage could be done if hackers were to take control of a country's SCADA systems, there have been few examples - until a few months ago, with the power outage in Ukraine caused by hackers.

Hey everyone, this guide will show the process of stealing your victims Facebook credentials. This is a followup to my previous post.

Welcome to my very first tutorial ever. Today I will be teaching you how you can use Arachni to scan vulnerabilities of web applications. I welcome all criticism good or bad as a teaching method for myself.

How's it goin'? In this tutorial, we will learn about the security issues of the popen and system functions. I've seen a few people attempting to run command line utilities or whatever it is they require with calls to these two functions but may not know the security implications which come along with it. I will show you using an example from the wargame IO Smash The Stack.

First of all, Merry Christmas and Happy New Year to all Null-Byters that learn and teach in this wonderful site. In this article we will explore the basics of the meterpreter's IRB (Interactive Ruby Shell).