Do you play Gears of War 2 online? Have you ever wanted to execute someone in midair? Who hasn't? This video will show you how to do it using the dead body launcher glitch. Well, you won't see it, but the host will! Who doesn't like messing with the host of their game, especially if they use a lagswitch or engage in some other such uncool behavior?

In this Outdoor Recreation video tutorial you will learn how to perform a varial kickflip. Varial kickflip is a combination of pop shove-it and kickflip. The video initially explains the position of both the feet by hands and the movement of the board is also explained by moving it with hand. Place your front foot like in kickflip, the position may vary from person to person, and the back foot like in a normal pop shove-it. You pop first and flip forward so it’s concave, comes around, spins...

The Gardening Guru demonstrates how to prepare and lay pavers in a multi-level adjoining area. First, get a garden stake use it to measure the evenness of the terrain and to set the height. Put the leveling tool on top of the pavers to even out the dirt. Then, lift out the rails. Once the rails are removed, you can then set the pavers directly on the dirt. If you prepare your area correctly, you will save a lot of time when you execute the actual project. This technique is useful when dealing...

Two techniques to shuffling cards in sleeves are the brick shuffle and the sleeve shuffle. These are not shuffling methods that casinos use. To do a brick shuffle, put your deck of cards in one hand and use the other hand to quickly move stacks of cards into different places in the deck. The brick shuffling technique has the propensity to warp the cards. To execute a sleeve shuffle, divide the deck of cards into two stacks and then thread the two stacks into one another using gentle pressure....

In this how-to video, you will learn how to identify and control problems with Ash and Golden Rain Trees. If there are discolorations in the tree branch, there may be a few problems. If you see a severe orange color, this will damage the tree. You can paint the tree with a white paint to avoid this problem. Pruning cuts that have been executed poorly will also cause discoloration and rot. If the leaves have tip burn, this may mean that the air is dry and arid. If twigs on Junipers look dirty ...
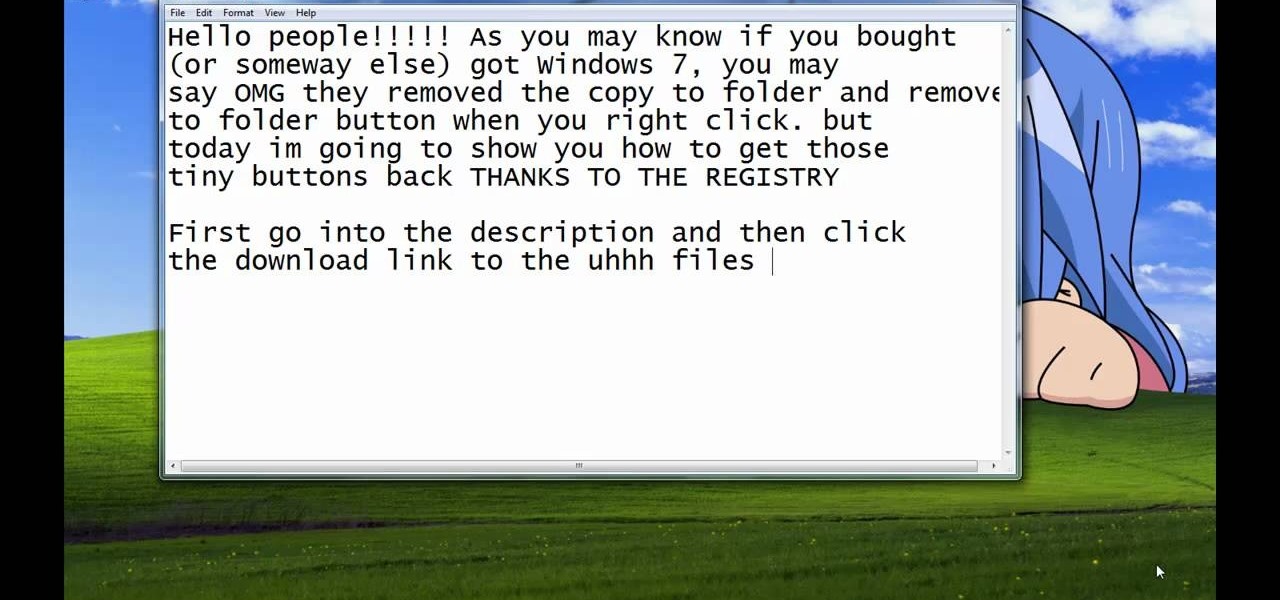
Steps taken to get the Copy to and Move to folder function in Windows 7 are:1. Go into the description and click the download link, to download the files2. After downloading the registry file you will see a zip file, which you need to extract using the software called Win Zip.3. After extracting the zip file, you will see two registry file (copy to and move to) execute both the registry file and give Yes, so that the file gets installed successfully.4. After successful installation, it is rec...

Time lapse is a great, transcendent storytelling device that can be used for transitions in narrative, documentary, and corporate work. Watch as this series of videos help you set up and execute a proper time lapse sequence.

In this Inteltus tutorial video, viewers are treated to a step-by-step guide to creating a Twilight inspired text effect in Adobe Photoshop CS4. Starting from scratch, the host goes through the actions in real time, explaining each step of the way. The viewer is free to make their own modifications to the file in order to integrate the effect into their own Photoshop work. While the video is aimed towards experienced Photoshop users, it is broken down enough that even a beginner will have no ...

Find out how to give yourself the perfect beard treatment as common misconceptions are unveiled. This video will not only show you how to execute the simple processes of shaving correctly, but also tell us what not to do, and why the barbers we have been going to have not strictly been doing their job right! For a good shave the hot towel should be applied before the lather is applied to the beard. This makes for a smoother and more effective shave, not to mention a more comfortable one. This...

In this video tutorial, viewers learn how to create a Pandora battery for the fat PSP. A Pandora battery allows the user the process of using exploits and hacks to execute unsigned code on the PSP. Before beginning, users are advised to completely drain the battery. Begin by taking out the battery and cut it open. Use a knife and gently pry it open. Do not damage the circuit board. You will need to break the pin under the number 4. Then put it back together and place it back into the PSP. Thi...

In this video tutorial, viewers learn how to play the song, Silent Night on the violin. Silent night is a popular Christmas Song that can be played on the violin very sweetly. The song is slower and this video will show you how to play the correct rhythm and notes. This video provides all the string movements and order that the notes are needed to be played, in order to execute the song. This video contains voice narration and a visual demonstration for viewers to easily understand and follow...

In this video tutorial, viewers learn how to play the classic Christmas carol "Silent Night" on the acoustic guitar. This video provides all the string movements and order that the notes are played in in order to execute the song. This video contains voice narration and a visual demonstration for viewers to easily understand and follow along. This video is at a slow pace and has step-by-step instructions. This video will benefit those viewers who play the acoustic guitar and would like to lea...

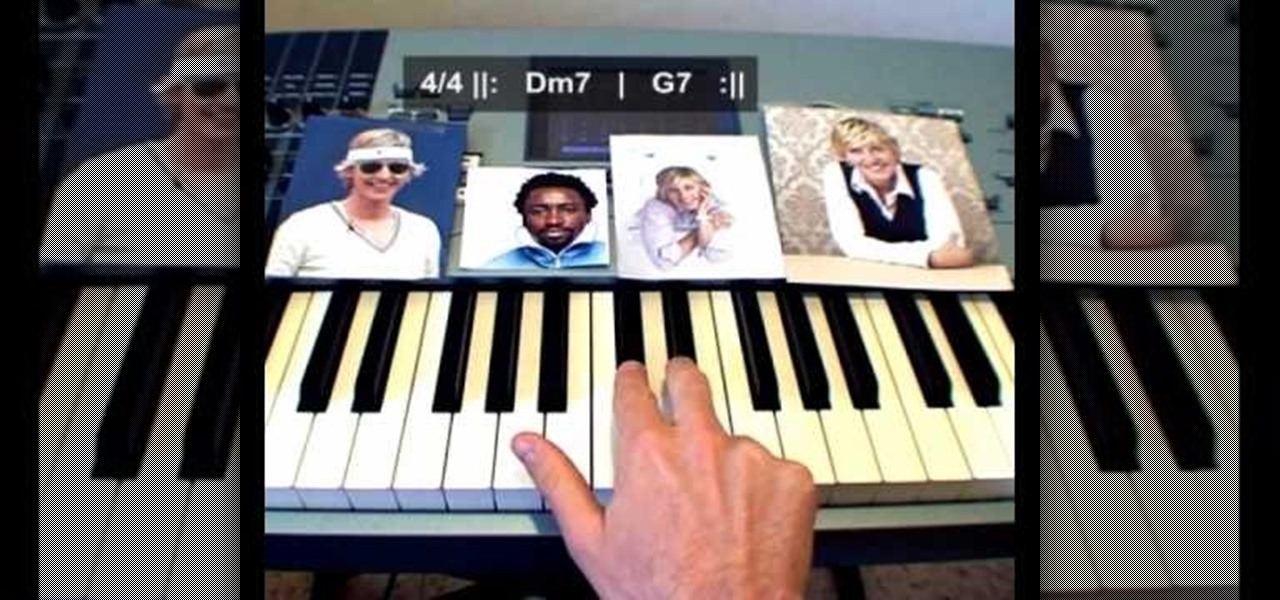
In this video tutorial, viewers learn how to play the theme song from the Ellen DeGeneres Show on the piano. This video provides the order that the keys are needed to be played, in order to execute the song. This video provides voice narration and a visual demonstration for viewers to easily understand and follow along. It is at a step-by-step slow pace for viewers to easily stay connected with the video and keep up. In the video description, it also contains piano tab for this tutorial if vi...

In this video tutorial, viewers learn how to play the song "Octopus' Garden" by the Beatles on the acoustic guitar. This video reveals all the string movements and the order that the notes are need to be played, in order to execute the song. This video provides voice narration and a visual demonstration for viewers to easily understand and follow along. This video will benefit those viewers who enjoy playing the guitar and want to learn how play a new song.

In this video, viewers learn how to play the song "But I Do Love You" by Leann Rimes on the acoustic guitar. This video reveals the string movements and the order in which the notes must be played to execute the song. The video provides step-by-step narration and a visual demonstration for viewers to easily understand and follow along. This video will benefit those viewers who are interested in playing the guitar and want to learn how to play a new song.

In this video tutorial, viewers learn how to play the song "In This River" by Black Label Society on the acoustic guitar. This video reveals all the string movements and the order that the notes are needed to be played, in order to execute the song. The video provides step-by-step narration and a visual demonstration for viewers to easily understand and follow along. This video will benefit those viewers who are interest in playing the guitar and want to learn how to play a new song.

In this video tutorial, viewers learn how to play the song "Imagine" by John Lennon on the acoustic guitar. The video reveals the string movements and the order that the notes are needed to be played, in order to execute the song. The video provides step-by-step narration and a visual demonstration for viewers to easily understand and follow along. This video will benefit those viewers who are interested in guitar and want to learn how to play a new song.

Walt Ribeiro shows you how beats per minute work along with time signatures. This video takes you through the steps with a detailed explanation of how they work together and is executed using a drum along with a handy saying to help you keep your time signatures going steady to the beats per minute. Walt explains this using an electronic tempo clock while changing up the time signature. If you have ever had a music question with how these two things relate to each other then video is for you.

Do you want to know what's the secret to a great looking lawn ? Then you have to watch this video in which Lowe's home improvement expert Mike Kraft explains how to sharpen or replace a Lawn Mower blade. Mike will share with you all the tips and the secrets of this simple and yet crucial operation. From the tools required to the safety measures, everything will be explained to you in this video with all the steps actually executed and filmed right in front of you.

Learn how to do a roundoff whip full combo with tis how-to video. In order to accomplish this combination you must first be comfortable with doing a roundoff, roundoff back tuck, and back layout.

Take a look at this instructional video and learn how to perform the impressive looking butterfly twist. You may have seen this move performed in various martial arts movies. This acrobatic technique is simple to perform. The first dip is crucial. After you dip, your head will be facing the other direction and as you jump, you essentially hug yourself and spin in the air before landing on your feet. Sounds complex? Check this tutorial out.

The line dance is a dance with repeated sequence of steps in which a group of people dance in one or more lines, all facing the same direction, and executing the steps at the same time. Line dancing's popularity grew out of the 1970's, when the country-western dance continued to explore and develop this form of dancing.

The line dance is a dance with repeated sequence of steps in which a group of people dance in one or more lines, all facing the same direction, and executing the steps at the same time. Line dancing's popularity grew out of the 1970's, when the country-western dance continued to explore and develop this form of dancing.

The line dance is a dance with repeated sequence of steps in which a group of people dance in one or more lines, all facing the same direction, and executing the steps at the same time. Line dancing's popularity grew out of the 1970's, when the country-western dance continued to explore and develop this form of dancing.

In this video tutorial, Chris Pels will show how to include JavaScript to an ASP.NET page for use on the client page to provide a richer and more robust user experience. First, see how to include JavaScript directly within an ASP.NET page and reference the script from within HTML page elements. Next, see how to abstract the JavaScript to an external JavaScript file which offers the advantage of being cached by the browser and can be used by multiple pages. Lastly, learn how to add JavaScript ...

"The Christmas Song" is the Christmas song of all songs, but many know this holiday favorite under a different name— "Chestnuts Roasting on an Open Fire". It may not be as old as other Christmastime favorites, like "Jingle Bells" or "Rudolph the Red-Nosed Reindeer", but thanks to Mel Tormé and Bob Wells, it's now a quintessential Xmas song, even for ukulele players.

A stager is a small piece of software that's typically used by malware to hide what's happening in the early stages of infection and to download a larger payload later.

Video may have killed the radio star, but will volumetric capture and augmented reality kill the video star?

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

With a simple social engineering trick, sudo passwords can be captured in seconds without the target's knowledge. The passwords can then be saved to a file or exfiltrated to another computer on the network.

One of the best ways to improve your skills as a hacker is to learn to combine different avenues of attack to achieve success. What if it were possible to get a victim to connect to our machine and execute a chosen payload on our behalf? This is indeed possible with the almighty Metasploit and the aid of a technique known as command injection.

In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.

While hackers have taken advantage of numerous vulnerabilities in Adobe's products to deliver payloads to Windows users via PDF files, a malicious PDF file can also wreak havoc on a Mac that's using the default Preview app. So think twice before double-clicking a PDF open on your MacBook — it might just be a Trojan with a rootkit inside.

Hello Friends … My name is Suresh Senarathna and this is my first “How-To” post,

Welcome back! Sorry for the dry spell, but I've been rather busy setting up some side projects! If you remember back to a few training sessions ago, we covered basic file I/O. This is a very important step in making our scripts applicable in a real life scenario, and today we're going to further these concepts.

Welcome back, everybody. In the previous article, we covered the ideas and concepts of well-known ports and trust exploitation in order to evade a firewall. Today, we'll be building the shell, the part that receives commands, executes them, and sends the output back to the attacker.

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

Hello all, this is my first submission to null byte! I noticed something a little strange, particularly that whenever Meterpreter is discussed, it is virtually always in the context of Windows. Granted, the Windows Meterpreter is more powerful than the version that can run on OS X (it has several more commands/options), but I think it is still worth noting how to do it. I've even seen some people mistakenly say that Meterpreter can only be run on Windows, which is not true. Meterpreter can ea...

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.

If you pre-ordered your Samsung Galaxy S4, it might very well be possible that you're reading this on your brand spanking new Android device. As is commonplace with the release of popular smartphones, rooting instructions are usually released simultaneously. I mean, what's the point of paying so much for an expensive phone if you can't have a little fun? Android developer Dan Rosenberg (aka djrbliss) recently announced that you can root your Samsung Galaxy S4 using the root exploit he origina...