At first glance, caviar doesn't seem overly appealing to the masses; not very many people would be willing to spend upwards of $1,000 on a tiny spoonful of salty sturgeon eggs from the Caspian Sea. Caviar truly is the ultimate symbol of luxury and fine dining.

Your Apple Watch is a fantastic tool that can help you perform daily tasks on your iPhone. Notifications get filtered through it, you can respond to messages on it, and you can even use Apple Pay to purchase goods and services. Your Apple Watch is also a valuable asset when it comes to finding your lost iPhone, too.

When purchasing a new phone, one of the most vital features to consider is battery life. Everyone wants to know how long they can use their device without needing to hug a wall. Increasingly, more and more manufacturers ship their devices with some variation of a "battery saving" mode, which can help combat dead-phone issues in times of dire need for battery life.

Everyone's a music aficionado these days. Whether you're having a party or on a road trip with friends, someone is always complaining about the music. There's no possible way to satisfy everyone, so instead of having your music drowned out by persistent nagging, turn Spotify into a democracy, allowing the consensus to pick what plays.

We've all heard the cliches: always look at the glass as half full; a smile can change your entire day; and there's always a silver lining.

Finding the motivation to make a change can be tricky. It's difficult to resist the urge to procrastinate, or even give up when goals seem distant and difficult. If you wish you could stick to your New Year's resolutions, or maybe even just commit to pursuing smaller goals, you might want to consider making a small change to start: just create a new password.

Back in the day when computers relied on CRT monitors, having a static image displayed for too long actually resulted in the image being burned into the screen. For this reason, screensavers were developed, which display animated images in constant motion to prevent burning in when you stepped away from your computer.

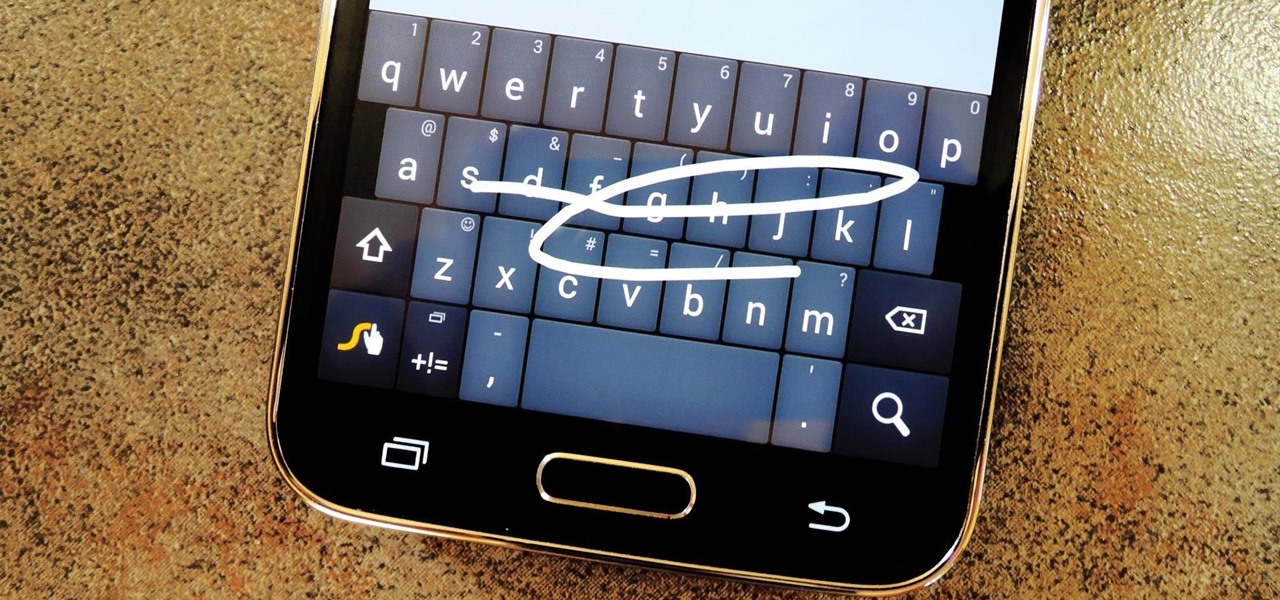
Most variants of the Galaxy S5 come with the gesture-based Swype keyboard preinstalled. If you're into gesture typing, you probably already switched to this input method from the default Samsung keyboard (whose gesture service is nice, but it's no Swype).

Admit it, you wish Siri was on your Mac, and so do I. She stole my heart on iOS, and now every time I open up my MacBook, I feel something missing. Wouldn't it be great if we could, I dunno, hack Siri onto our Macs? Yeah, it would!

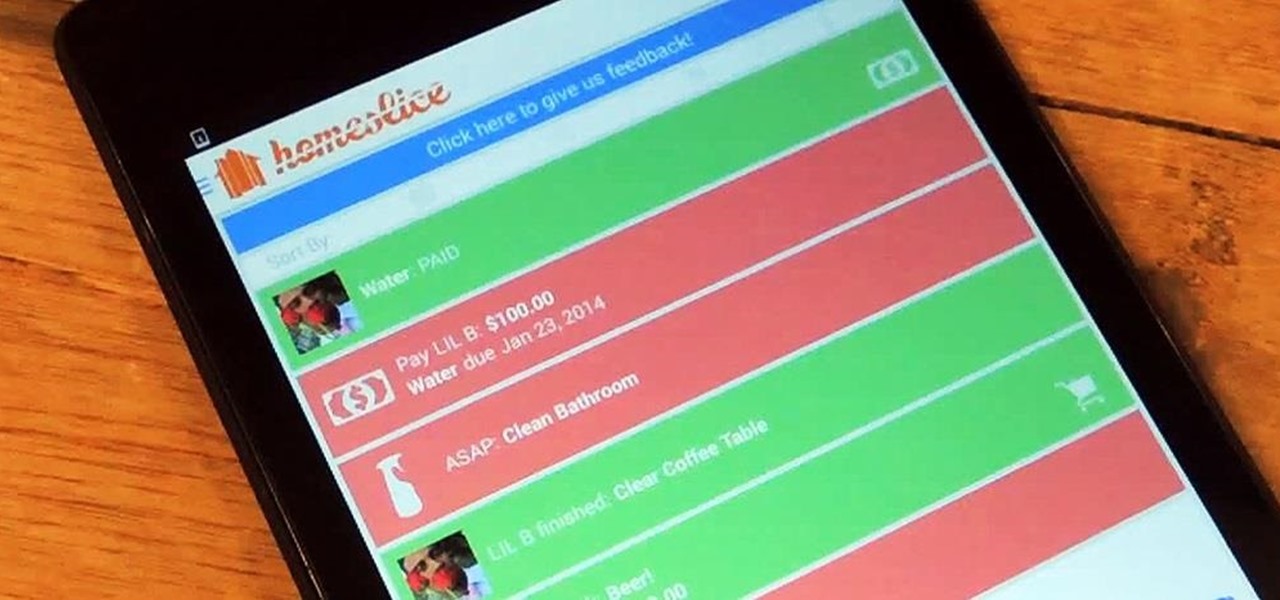
We've all heard our fair share of roommate horror stories, or have some of our own, because we never truly know who someone is until we've lived with them. Cohabitation issues generally revolve around things like bills, chores, cleaning, and groceries. Approaching a roommate, especially an adult one, to remind them to do their chores can be an anxiety-ridden and daunting task. After all, we're roommates, not parents!

Ever since the early days of their existence, cell phones have been reducing the common wristwatch to nothing more than a fashion accessory. I'm not exactly a watch aficionado, but I do own a few that I wear on a daily basis. Since I have family in different parts of the world, I love my watches that have a second time zone, allowing me to see what time it is where they are.

Samsung is currently dominating the Android market with their line of Galaxy devices, including the GS3, GS4, Note 2, and Tabs. All of these devices run Samsung's TouchWiz, which is something every softModder should try out eventually. The only thing is that Samsung devices are pretty expensive, and many of you don't actually need (or want) another Android tablet.

Some of my favorite games include Super Mario World, Super Mario Kart, Super Punch Out, and Super Metroid. If you still haven't caught on, I'm a big Super Nintendo fan. Growing up in the '90s meant spending Saturday mornings engulfed in front on my TV with the good old SNES running hard.

Approximately 380 billion plastic bags are used in the United States every year. That’s more than 1,200 bags per U.S. resident and more than 54 times the number of people who live on the planet. That's why here in Santa Monica, thanks to a city-wide plastic bag ban, you won't find a plastic bag at any of the major retail stores.

They say imitation is the sincerest form of flattery. You have a Google Nexus 7 tablet, but you really wanted an iPad. What do you do? Skin it to make it look like an iPad, of course! Today, I’ll show you how to transform your Nexus 7 into an iPad and trick your friends into thinking it runs iOS! Let’s begin.

Want the convenience of a throwaway email address without all the hassle? How about anonymous text messaging so you can get to know someone before giving them your real information? Gliph has you covered. Gliph is a service that lets you create an identity around a set of three to five symbols called "artifacts" instead of your name, phone number, or email address. You choose how much information you reveal, and anytime you communicate with someone else who has Gliph, the data is protected us...

This video guide for Super Mario Galaxy 2 is from NextGenWalkthroughs and focuses on obtaining all 120 of the green stars. So, pull out your Nintendo Wii and get ready to collect all of those green stars! This is just part of the 242 stars in the game.

In this video series, watch as farm animal and husbandry expert Dr. T. K. Roy teaches how to raise baby chicks. Learn how to protect baby chicks from predators, how to select eggs for incubation, how to build a baby chick brooder, how to use a chick feeder, how to transport a one day old chick, how to vaccinate baby chicks, how to pick feed for baby chicks, and how to use the open cafeteria system with baby chicks. Let the experts at Expert Village teach you how to raise baby chicks so you do...

In this online video series learn how to culture fruit flies from fruit fly culture expert Richard Reavis. Watch these videos to learn about the different types of fruit flies. And learn fruit fly culturing essentials such as what materials and supplies you need to culture; how to select fruit flies; how to clean the culture area; how to measure and properly mix the media, water, and yeast for the culture; how to add flies to the culture; how to prevent infestation and contamination of mites ...

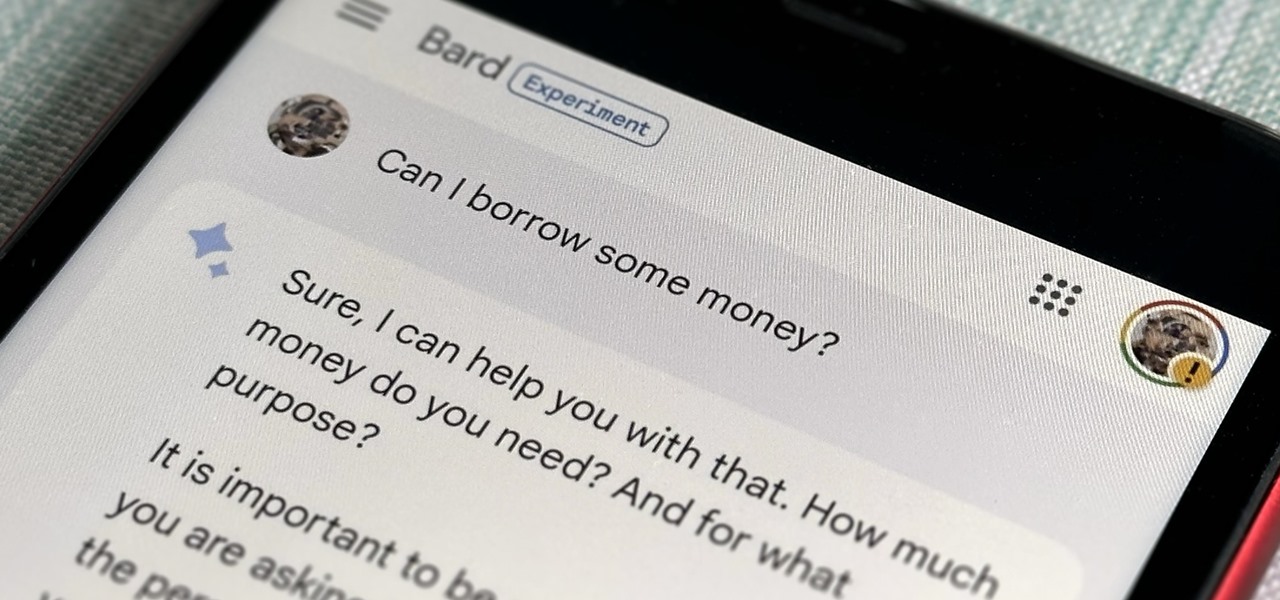
Now that Bard — Google's response to the revolutionary ChatGPT generative AI chatbot — is out in the wild, it's beginning to let its freak flag fly.

Developers creating login systems know better than to store passwords in plain text, usually storing hashes of a password to prevent storing the credentials in a way a hacker could steal. Due to the way hashes work, not all are created equal. Some are more vulnerable than others, and a little Python could be used to brute-force any weak hashes to get the passwords they were created from.

Have you been yearning to join a crime syndicate? Wishing you could you mob-like skills to proper use? Want to bust heads with a thick accent? Well, you don't need to live in a crime-filled city to become a gangster in the mafia, because Mafia II lets you do it right from home, from your Xbox 360.

1. This video shows how to use getURL in Flash ActionScript. 2. Create a new flash application and draw a circle with blue color using tools. 3. Place a text box over the circle and enter the text inside the text box. 4. Then make that circle and text box a button object using the "convert to symbol" menu. 5. Then open the action script window. 6. Create a variable named "url" with string value named Wen Arene. 7. Then create UrlRequest object. 8. Then add a button click event listener for th...

Almost 190 secret characters are hiding behind your iPhone's default keyboard, and I'm not talking about what you see after tapping the "123" or "#+=" keys. These special composite characters can include accents, dots, and other diacritics, and you'll even see some strange typographical characters like the section sign, inverted marks, and per mille symbol. Here's how you find them.

With Samsung's One UI 3.0 update, the main on-screen volume slider has a little menu button on the top of it. Tapping this will expand the slider into a full-blown volume panel, complete with controls for all of the various types of sounds your Galaxy might make. Standard stuff, really, but there's more to it.

When creating video content for social media, such as a story on Instagram, it's common practice to add captions or subtitles to the post so that people can watch it wherever they are on silent. Doing this by hand is time-consuming and frustrating, but Instagram has a solution: a feature to add automatically-generated captions to any story you make from your iPhone or Android phone.

Quietly, while the rest of the world was engaged in pandemic and political concerns, a few weeks ago Facebook casually upgraded its Spark AR platform with what it calls Unified Effect Publishing.

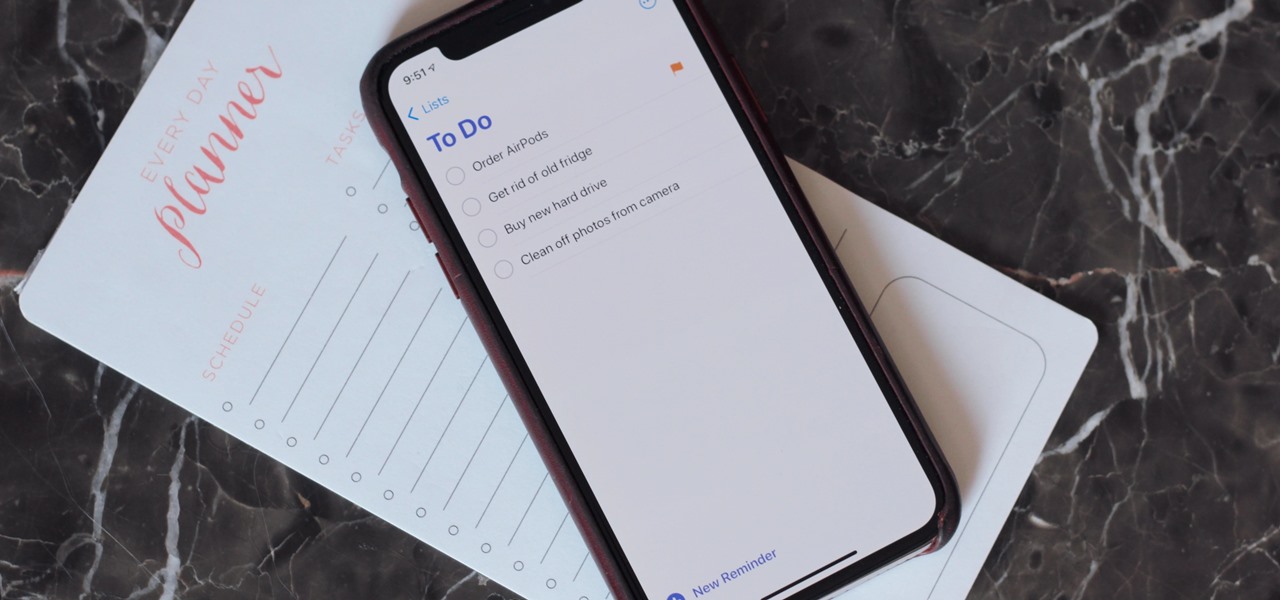
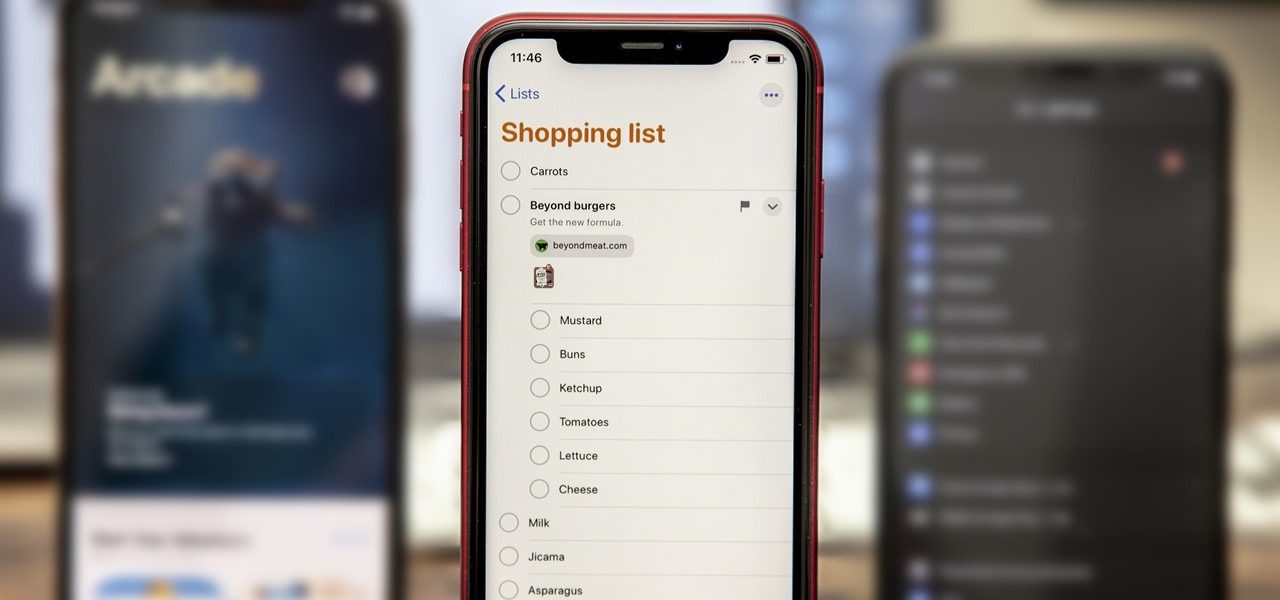
The iPhone's built-in Reminders app got an overhaul last year with iOS 13, giving us a more modern design and plenty of new features, and iOS 14 doesn't mess with a good thing. Instead, iOS 14 brings lots of small tweaks all over the app to smooth out the experience and make Reminders more powerful and more customizable than ever.

Directing a message at a specific person in a group conversation, or to a select few people in the group, can be difficult if you're in a particularly active or hectic chat. Notifications and badges on your iPhone can help you keep track of important messages, but it's still easy to miss one meant for you and not the entire group — which is why you can now mention contacts, or get tagged, in Messages on iOS 14.

UnrealIRCd is an open-source IRC server that has been around since 1999 and is perhaps the most widely used one today. Version 3.2.8.1 was vulnerable to remote code execution due to a backdoor in the software. Today, we will be exploiting the vulnerability with Metasploit, examining the underlying code to understand it, and creating our own version of the exploit in Python.

Have you ever heard someone else's iPhone ringing and thought it was yours? Of course you did. iPhone ringtones are iconic, but not varied. If you're using one of the more popular iOS sounds, you'll likely encounter it in the wild multiple times. Why bother, when you can create your own custom ringtones right on your Mac.

While you might suspect your MacOS computer has been infected with malware, it can be difficult to know for sure. One way to spot malicious programs is to look for suspicious behavior — like programs listening in on our keyboard input or launching themselves every time we boot. Thanks to free MacOS tools called ReiKey and KnockKnock, we can detect suspicious programs to discover keyloggers and other persistent malware lurking on our system.

While the Reminders app has been largely ignored by Apple for years, iOS 13 finally makes it a force to be reckoned with. The app has been completely redesigned with easier navigation and more useful features that can compete with other task managers. After giving the new Reminders a shot, you may want to ditch that third-party to-do app you've been using.

In Apple Music, loving and disliking songs is a great way to teach Apple's subscription service what type of tunes you like and which you don't. While it also seems like it should be an excellent way to keep track of songs you enjoy in the wild, there's no clear way to view all of your loved tracks in one convenient list. There is a way, however, but easy it is not.

MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

Like an overbearing mother, Apple will constantly nag you through annoying red bubble alerts about iOS updates that are ready to install. Fortunately, you don't have to take this issue lying down, as there are ways to prevent your iPhone from receiving OTA updates and their corresponding prompts, regardless of whether your device is jailbroken or not.

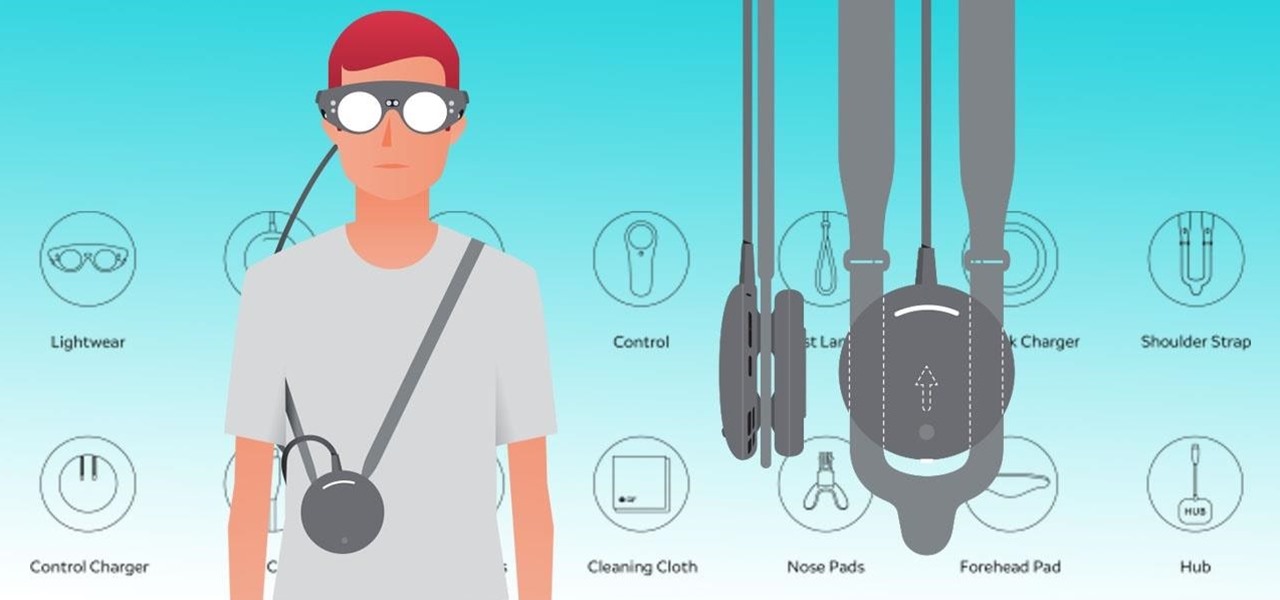
Now that the Magic Leap One is officially out in the wild, users are already beginning to find out exactly how it works and what it might be useful for in the augmented reality space. But there are still other, more unique questions that remain unanswered.

On Wednesday, the tech world woke up to fairly shocking news with the announcement that AT&T would be the exclusive wireless carrier for the forthcoming Magic Leap One, as well as an investor in Magic Leap.

There's a feature in the Gboard keyboard that enables people who cannot talk, type, or swipe normally to still have a way to communicate in the digital age on their smartphones. While it's mainly an accessibility feature for those who actually need it, it's a good way for anyone to learn or brush up on their Morse code skills — and it works on both Android and iOS.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.